After alleged iCloud breach, here's how to secure your personal cloud

In light of the news that an alleged hacker cracked the iCloud accounts of celebrities, such as Jennifer Lawrence and Kate Upton, to reveal their private, intimate photos, there remains a high level of speculation and rumor over exactly what happened.
Since the photos showed up immediately after an Apple "Find My iPhone" exploit was revealed, many are pointing their fingers at Apple's own security situation.
The security exploit in question "ibrute" was published on GitHub on Saturday. It used a security hole in the Find My iPhone service application programming interface (API). The hole allowed hackers to keep trying one password after another until they found one that worked. Once a password was found, it could then be used to access a user's iCloud account.
Apple told Recode on Monday it was "actively investigating" if these iCloud accounts had been hacked. The iPhone and iPad maker rarely talks to the press, suggesting it is taking the alleged breach very seriously.
While this was an awful security hole, the exploit relies on ordinary account owners using bad passwords. The automated exploit uses a list of just 500 common passwords.
Indeed, with this hacker tool, you can't really call these attacks "hacks" at all. All a would-be attacker needed is the email address you use for your Apple ID. If you had a common and easy-to-guess password, your files could have been in an attacker's hands in less time than it will take you to read this story.
Some experts believe that this is only the beginning of a flood of iCloud security hacks.
So, if you want to keep your intimate photos private, or your company's industry secrets safe you must start by using something other than "password" or "123456" for your password.
Tech Pro Research: Security
Rather than lecture you yet again on why you should use good passwords, let me suggest that you use easy-to-remember, but hard to crack passwords that use phrases rather than random characters. So, for example, "Steelers?Win!Cowboys?Lose!" or "Volt!Amp!Tesla!Edison?" won't be cracked by any common password cracker program but you'll be able to recall such phrases much more easily than say "ufc#1310."
Safe passwords don't have to be memory twisters. They just have to be hard for computers to work out, and phrases make great passwords.
If you don't think you can keep track of phrase passwords, password managers are readily available. Such programs as RoboForm and LastPass make it easy to stay on top of your passwords.
But for the sites and services that really care about keeping data safe, two-factor authentication can be the strongest tool ordinary users have to prevent unauthorized access to their data.
With this method, even if someone has your password to change it they must also have access to a device that should only be in your hands such as a phone. Typically, two-factor authentication systems will send you an e-mail or text message, or call you, requiring you to enter a code before your password can be changed.
Here's how to turn on two-factor authentication on the most popular personal cloud storage services:
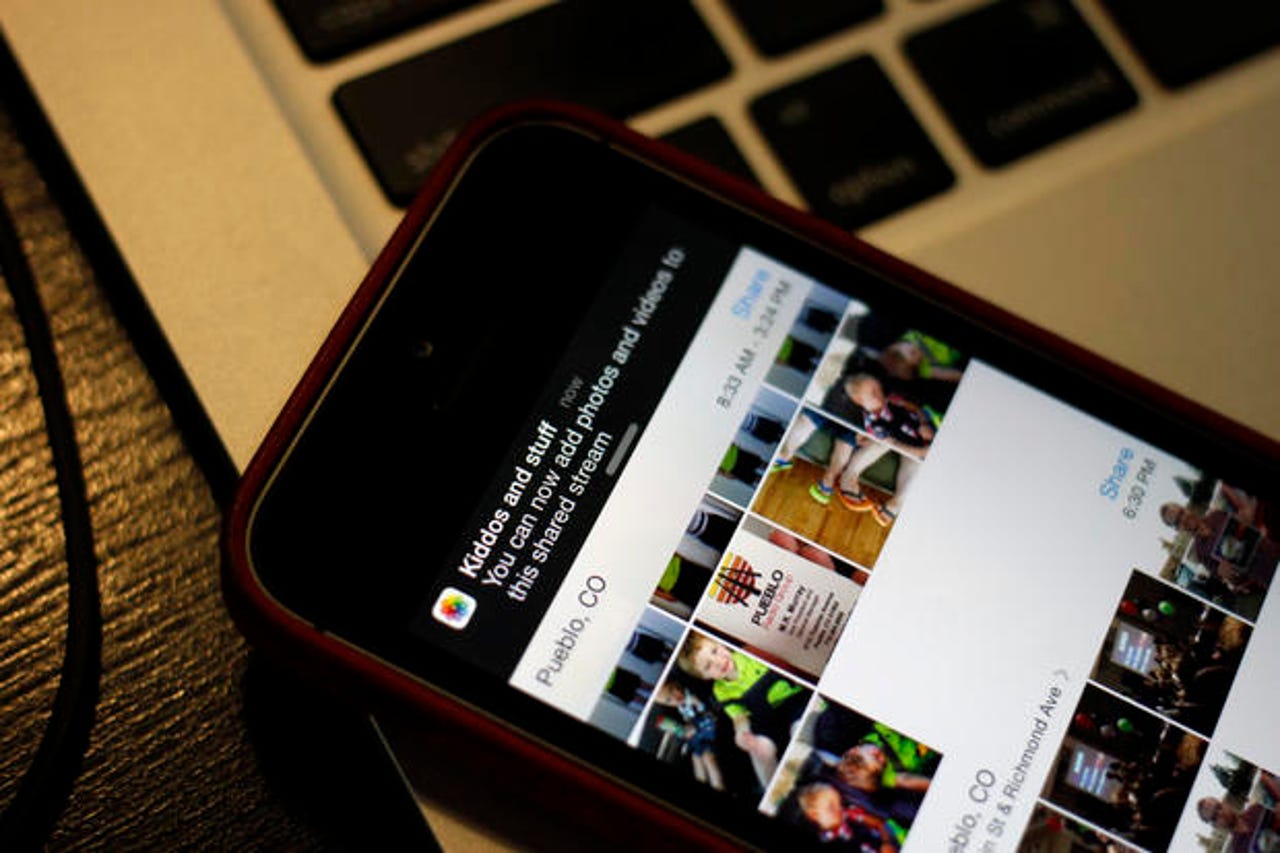
Apple iCloud
- Login to My Apple ID.
- Pick "Manage your Apple ID and sign in"
- Select "Password and Security"
- Under "Two-Step Verification," select "Get Started," and follow the instructions.
Note: Be aware that when you change your Apple ID to two-factor authentication, it's a one-way journey. You can only change your password afterwards by using the two-factor method.
Dropbox
- Sign in to Dropbox.
- Click on your name from the upper-right of any page to open your account menu.
- Click "Settings" from the account menu and select the "Security" tab.
- Under "Two-step verification" section, click "Enable."
- Click "Get started" and follow the instructions.
Note: You will need to re-enter your password to enable two-factor verification. Once you do, you'll be given the choice to receive your security code by text or to use a mobile app.
Google Drive
- Login to Google from this link.
- Enter your phone number.
- Enter the code that you'll get from either a text or a voice phone call.
- Follow the instructions.
Note: You will need to get a new code for each PC or device that uses any Google services. For some services, such as Gmail when accessed on an Apple device or by a mail client or some instant message clients, you'll also need to set an application specific password.
Featured
Microsoft OneDrive
- Login to your Microsoft Account.
- Go to "Security & Password."
- Under "Password and security info," tap or click "Edit security info."
- Under "Two-step verification," tap or click "Set up two-step verification."
- Click "Next," and then follow the instructions.
Note: Microsoft may require you to enter a security code that the company will send to your phone or email before you can turn on two-step verification.
Many other services now offer two-step authentication. Here are ZDNet articles detailing how to set it up on Facebook, Twitter, and Google.
Two-factor authentication won't protect you if your photos or data are already out there, but it will help prevent such attacks from succeeding in the future.
Related stories: