Android malware can steal Google Authenticator 2FA codes

Security researchers say that an Android malware strain can now extract and steal one-time passcodes (OTP) generated through Google Authenticator, a mobile app that's used as a two-factor authentication (2FA) layer for many online accounts.
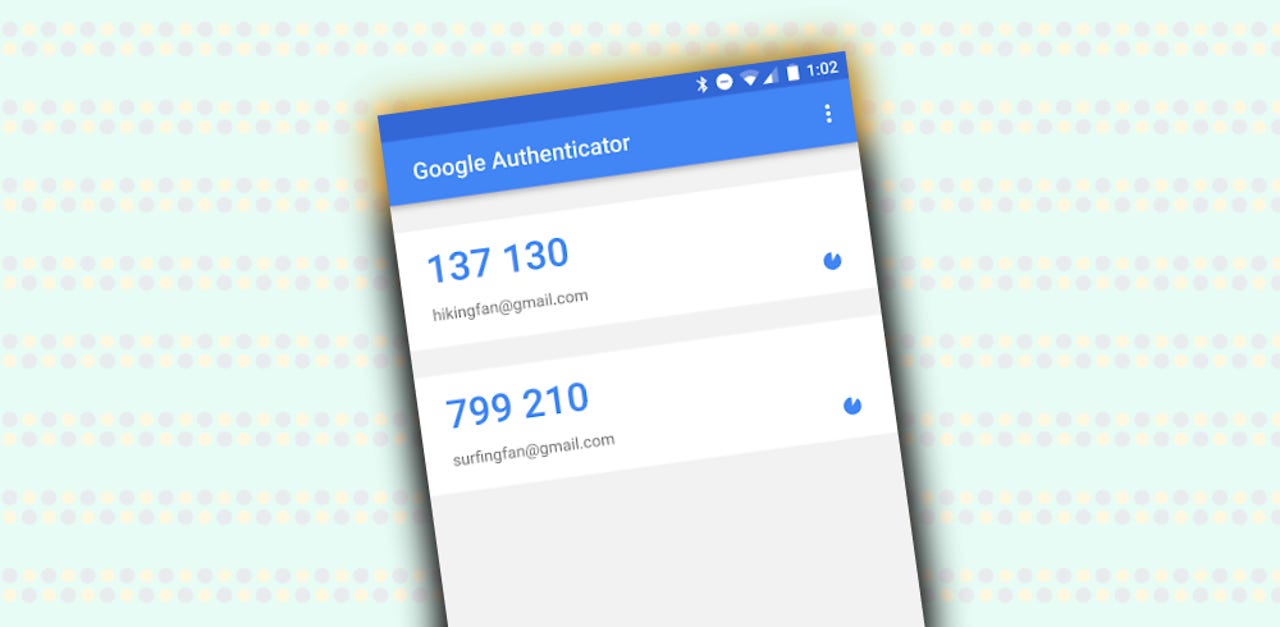
Google launched the Authenticator mobile app in 2010. The app works by generating six to eight-digits-long unique codes that users must enter in login forms while trying to access online accounts.
Google launched Authenticator as an alternative to SMS-based one-time passcodes. Because Google Authenticator codes are generated on a user's smartphone and never travel through insecure mobile networks, online accounts who use Authenticator codes as 2FA layers are considered more secure than those protected by SMS-based codes.
SEE: Cybersecurity: Let's get tactical (ZDNet/TechRepublic special feature) | Download the free PDF version (TechRepublic)
Cerberus gets Authenticator OTP-stealing capabilities
In a report published this week, security researchers from Dutch mobile security firm ThreatFabric say they've spotted an Authenticator OTP-stealing capability in recent samples of Cerberus, a relatively new Android banking trojan that launched in June 2019.
"Abusing the Accessibility privileges, the Trojan can now also steal 2FA codes from Google Authenticator application," the ThreatFabric team said.
"When the [Authenticator] app is running, the Trojan can get the content of the interface and can send it to the [command-and-control] server," they added.
ThreatFabric said this new feature is not yet live in the Cerberus version advertised and sold on hacking forums.
"We believe that this variant of Cerberus is still in the test phase but might be released soon," researchers said.
Feature developed for bypassing 2FA on banking accounts
All in all, the ThreadFabric team points out that current versions of the Cerberus banking trojan are very advanced. They say Cerberus now includes the same breadth of features usually found in remote access trojans (RATs), a superior class of malware.
These RAT features allow Cerberus operators to remotely connect to an infected device, use the owner's banking credentials to access an online banking account, and then use the Authenticator OTP-stealing feature to bypass 2FA protections on the account -- if present.
ThreatFabric researchers believe the Cerberus trojan will most likely use this feature to bypass Authenticator-based 2FA protections on online banking accounts, however, there's nothing stopping hackers from bypassing Authenticator-based 2FA on other types of accounts. This includes email inboxes, coding repositories, social media accounts, intranets, and others.
Historically, very few hacker groups and even fewer malware strains [1, 2] have ever had the ability to bypass multi-factor (MFA) authentication solutions.
If this feature will work as intended and will ship with Cerberus, this will put the banking trojan in an elite category of malware strains.
The new Cerberus capabilities are detailed in a ThreatFabric report that summarizes all the recent remote access-related upgrades detected in Android malware strains. The report contains additional insights about other Android malware operations, such as Gustuff, Hydra, Ginp, and Anubis.