Apple issues security fixes for iPhone, iPad, Apple Watch to fight Predator spyware

Apple has released emergency security patches for its core products just days after rolling out brand new versions of their operating systems. On Thursday, the company updated iOS/iPadOS 17 and WatchOS 10 with fixes aimed at patching several zero-day vulnerabilities that could leave a device open to a particular form of spyware.
Also: The best VPN services for iPhone and iPad: Tested and reviewed
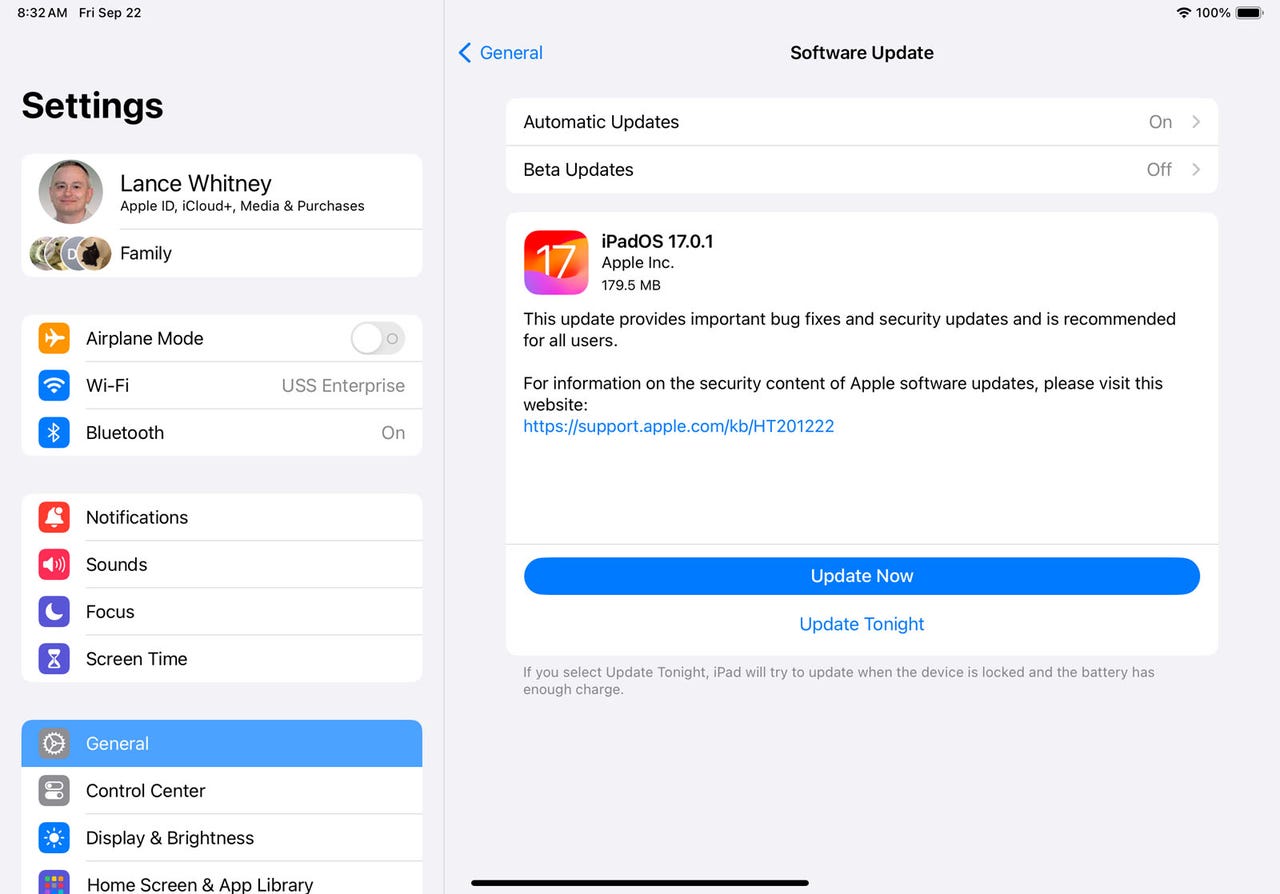
iPhone, iPad, and Apple Watch owners are urged to update their devices with this latest round of security fixes. On your iPhone or iPad, go to Settings, select General, tap Software Updates, and then tap the Update Now button. For an Apple Watch, open the Watch app on your phone. At the My Watch tab, head to General, select Software Update, and install the latest update.
Owners of the new iPhone 15 will find iOS 17.0.2 waiting. Users of older iPhones will jump to iOS 17.0.1. And Apple Watch wearers will install WatchOS 10.0.1.
Also: Buying an Apple Watch? Here's how to pick the best one for you
At its support pages for the iOS/iPadOS updates and the WatchOS update, Apple revealed that the vulnerabilities may have been actively exploited on versions prior to iOS 16.7. The company gave credit for discovering the bugs to Bill Marczak of The Citizen Lab at The University of Toronto's Munk School and Maddie Stone of Google's Threat Analysis Group.
Through Apple didn't reveal the nature of the vulnerabilities, both The Citizen Lab and Google's Threat Analysis Group released their own reports that described the threat to targeted devices.
In a Friday blog post, Google's Threat Analysis Group explained that Apple's security updates were issued in response to a zero-day exploit chain being used to install Predator spyware developed by Egyptian commercial surveillance vendor Intellexa. This type of spyware can record audio from regular phone and VoIP audio calls. Predator is also able to gather data from popular chat and calling apps, including WhatsApp, Telegram, and Signal.
The process worked through a man-in-the-middle attack in which a victim tries to visit an http website. With such traffic unencrypted, the attacker can send fake data back to the user to redirect them to an Intellexa website and exploit server. From there, the spyware could be installed without the user having to open any documents, clicking any specific links, or answering any phone calls.
Also: How to use StandBy Mode on iOS 17 (and which iPhones support it)
In its own report published on Friday, The Citizen Lab explained how and why the spyware was deployed.
Former Egyptian MP Ahmed Eltantawy was targeted with the Predator spyware through SMS and WhatsApp links, an incident that occurred after he announced plans to run for President in the 2024 Egyptian elections.
Egypt is a known customer of Predator, and the spyware itself was delivered from a device physically located in Egypt, according to The Citizen Lab. As result, the group said that it's highly confident that the Egyptian government was behind the spyware attack.
Spyware such as Predator and the NSO Group's Pegasus is used by governments against officials, political activists, dissidents, and journalists. Though individual users are typically not the target of these types of attacks, Apple still must patch any related vulnerabilities discovered on its products to protect all potential victims.
Earlier this month, Apple issued last-minute emergency patches for iOS/iPadOS 16, WatchOS 9.7, and MacOS Ventura 13.5. The company credited The Citizen Lab for finding the bugs, which itself revealed that these zero-click vulnerabilities were being used to deliver the Pegasus spyware. Pegasus is capable of remotely accessing a device to collect data, monitor conversations and email exchanges, and spy on users through the device's camera and microphone.