ATM malware available online for only $5,000

Researchers have discovered malware crafted to compromise ATMs available for sale in the underbelly of the internet.
Security
On Tuesday, cybersecurity firm Kaspersky Labs said that anyone can buy such malware for only $5000 through darknet markets.
With the rise of prolific cyberattacks, data breaches, and information theft, ATMs have become victims of cybercriminal operations in recent years.
ATMs often run on outdated operating systems -- Windows XP being one such OS linked to ATMs which is no longer supported -- and successful heists can lead to thousands in cash being stolen.
Malware which forces dispensers to throw out cash uncontrollably, mules paid by cybercriminal gangs to pick up the proceeds, hardware which tampers with the machinery involved -- there are many methods to steal funds, and it appears that making ATM malware available for a relatively cheap price is just going to add to the problem.
In a blog post, Kaspersky researchers said that in May this year they discovered a forum post in a darknet market advertizing specific vendor ATM malware for $5000.
The forum post contained a description of a crimeware kit able to empty ATMs with a vendor-specific API without the need to tamper with ATM users or their data.
In addition, the seller included details of necessary equipment, a detailed manual, and tips and tricks to encourage an ATM to dispense cash.
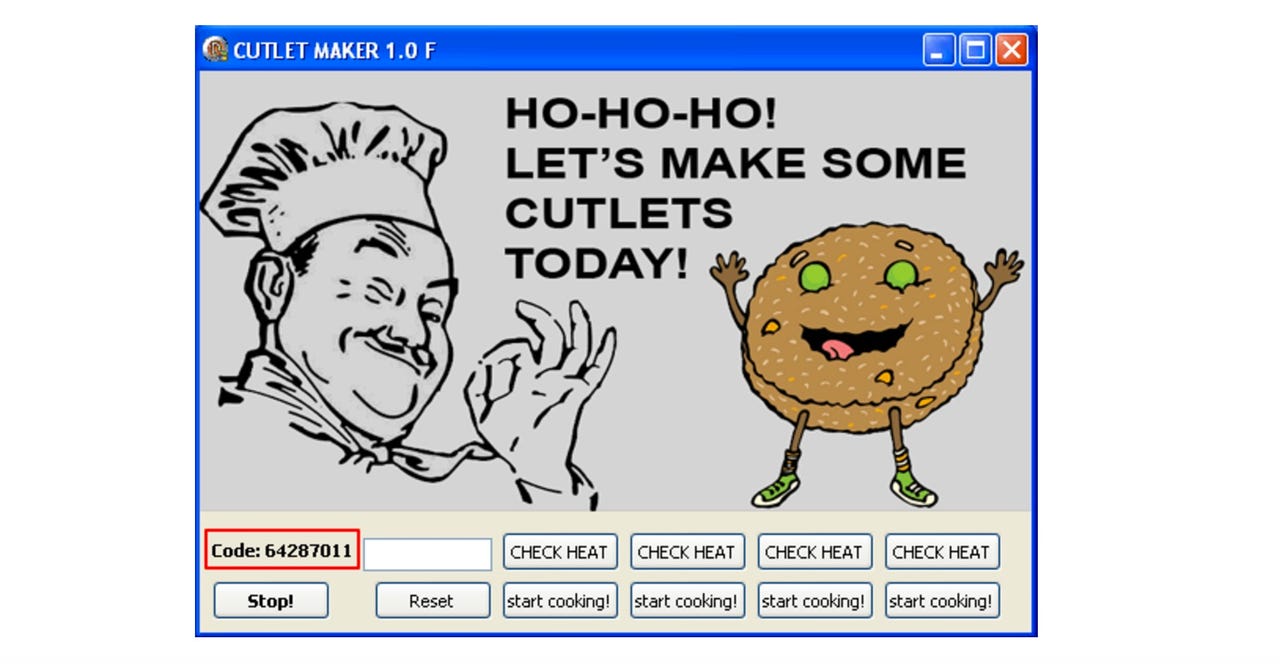
In order for the malware, dubbed Cutlet Maker, to succeed, the purchased software needed to be stored on a flash drive and then the attacker would need to use a drill to open the ATM system.
The flash drive would then need to be plugged into a USB port and the malware executed. The toolkit also contained a password generator called c0decalc which would then crack the system, and a simulator which is then able to scour ATM cassettes for funds, mimic a transaction and force the ATM to dispense cash.
Originally, the post was published on AlphaBay, which has since been seized by the FBI.
"The "Cutlet Maker" malware functionality suggests that two people are supposed to be involved in the theft -- the roles are called "drop" and "drop master," the researchers say. "Access to the dispensing mechanism of Cutlet Maker is password protected. Though there could be just one person with the c0decalc application needed to generate a password."
"Either network or physical access to an ATM is required to enter the code in the application text area and also to interact with the user interface," Kaspersky added.
While "cutlet" is often referred to as a meat dish, in Russian, the translation is a "bundle of money," which may suggest the malware's authors come from this region.
The cybercriminals behind the Cutlet Maker malware utilized not only malicious code, but were also able to snag proprietary libraries to dupe ATMs. However, they do need physical access to the inner workings of an ATM and with a few changes, device control software could be used to prevent new devices from connecting and the malware entering the ATM system at all.
When there is lax security and easy pickings to be had, cybercriminals will take advantage of it -- and it is up to banks, financial institutions, and ATM manufacturers to make the source more difficult to crack.
Previous and related coverage
ATM skimmers who stole $420,000 plead guilty in US court
The cybercriminals used card readers and pinhole cameras to steal the details of ordinary citizens.
Europol cracks down on ATM black box attack scheme
The "black box" attacks compromise ATMs to dispense cash.
ATM hackers release cold, hard cash at the click of a remote button
The ATMitch heist has shown attackers are now able to remotely create an ATM tunnel to financial reward with little effort.