Browser vendor leaks data via open server

A browser vendor leaked user data after it accidentally left an Elasticsearch server exposed on the internet without a password.
The leak occurred at Blisk, an Estonian company that develops the eponymously named Blisk browser.
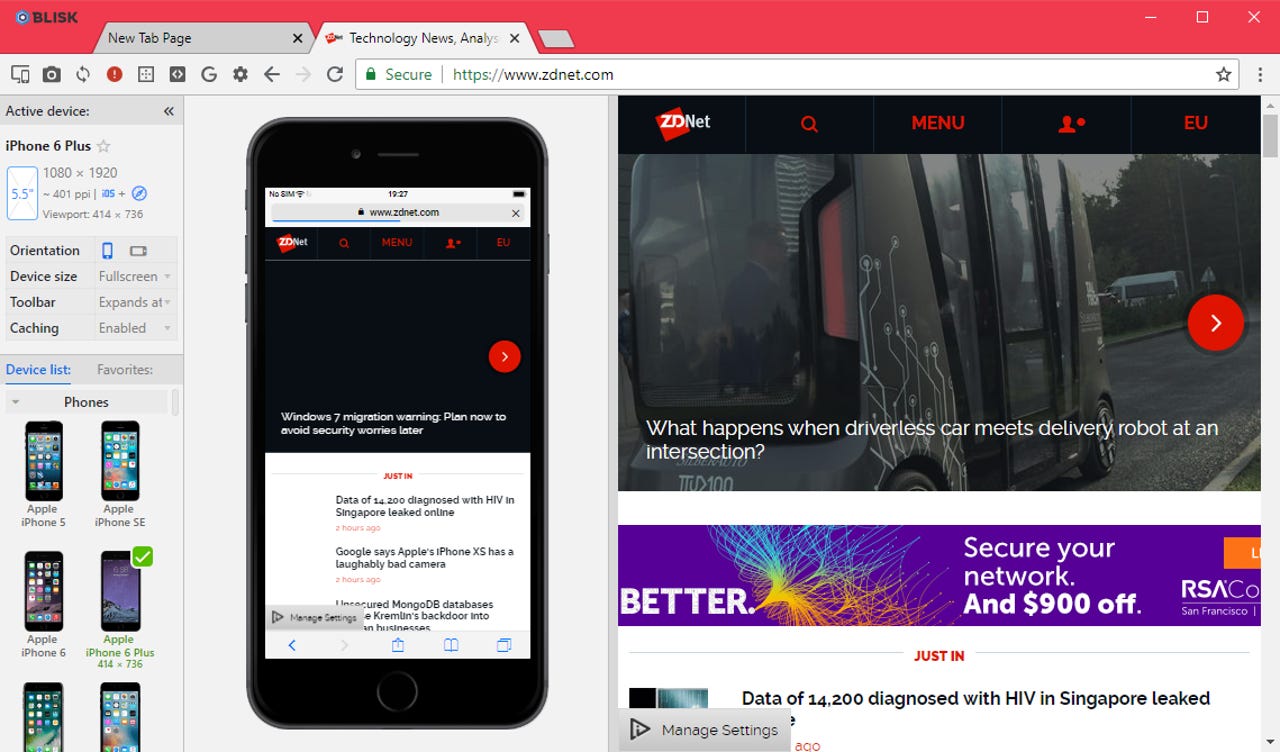
The Blisk browser is a Chromium-based offshoot tailored for the web and app development community, and comes with support for enhanced developer tools, device previewing capabilities, and project collaboration tools.
Launched in May 2016, the browser has gained a following in the web development market. On its site, Blisk says its browser is used by more than 40,000 companies, including some big names such as HP, Xerox, NASA, Unicef, Deloitte, UEFA, Vice News, and Pandora.
Last December, the company suffered an accidental data breach. On December 2, 2019, Noam Rotem and Ran Locar, two researchers with vpnMentor, discovered an Elasticsearch server belonging to the company that was accidentally left exposed online.
In a report shared exclusively with ZDNet this week, the vpnMentor researchers said they found personal details for thousands of web developers that had registered profiles with the Blisk website/browser.
In total, they found 2.9 million records, amounting for 3.4 GB of data, left exposed online.
The data appeared to be log entries for actions developers were taking inside the browser, such as registering profiles or inviting friends.
Personal details leaked via the exposed servers included email addresses and user-agent strings.
vpnMentor said it notified Blisk on December 4 and the browser maker had secured the server by the next day.
In an email yesterday, the Blisk team confirmed the leak and said that despite their error, the leak did no result in the exposure of sensitive information, such as passwords, financial information, or personally identifiable information (PII), such as names, billing info, or phone numbers, which were not stored on that particular server.
However, vpnMentor claims the data could have some operational value for an attacker if one did ever get their hands on it during the timespan the server was exposed.
The data could be used to target developers working for private companies, and tailor exploits and malware based on their user-agent strings (which include platform details).