Company behind LeakedSource pleads guilty in Canada

Security
Defiant Tech Inc., the company behind the LeakedSource.com portal, pleaded guilty this week, according to a press release from the Royal Canadian Mounted Police (RCMP).
The LeakedSource website launched in late 2015 and rose to infamy in 2016. Its operators gathered data from hacked companies, either from the public domain or by buying it from hackers.
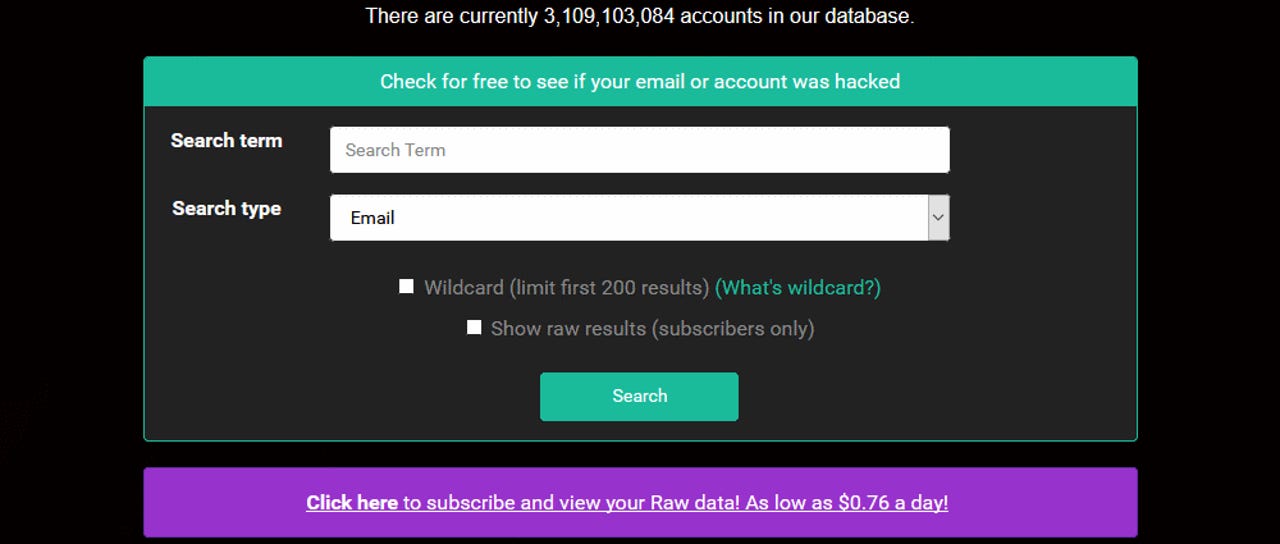
LeakedSource provided access to this illegally obtained information via a search form on site, to anyone willing to pay a fee. During its lifetime, it collected information such as usernames, real names, emails, home addresses, phone numbers, and even plaintext passwords.
The site made a living by advertising on public hacking forums, where it claimed it could help hackers gain access to high-profile accounts.
While it often tried to pass as a legal business, Canadian police began an investigation into the site's shady practice in 2016.
Site owner arrested in late 2017
An arrest was made in December 2017, when the RCMP took into custody the site's main operator, a man named Jordan Evan Bloom.
According to Canadian authorities, Bloom ran LeakedSource via a front company named Defiant Tech, from servers rented in Quebec.
The RCMP said they believe that Bloom's company made around CAN$247,000 (US$183,000) from "trafficking identity information."
During 2016 and 2017, the site listed hacked information for over 3.1 billion accounts. High profile companies that had their users' data sold on the site included Twitter, Last.fm, LinkedIn, VK.com, AdultFriendFinder, Mate1, Shadi, Weebly, and others.
Bloom was officially charged in January 2018. This week, his company pleaded guilty to charges of "trafficking in identity information and possession of property obtained by crime."
"We are pleased with this latest development," said Superintendent Mike Maclean, Officer in Charge Criminal Operations of the RCMP National Division. "I am immensely proud of this outcome as combatting cybercrime is an operational priority for us."
Canadian authorities have worked with the FBI and Dutch National Police to track down Bloom, in an investigation codenamed "Project Adoration."
While authorities charged only Bloom and his company DefiantTech in the investigation, there is also evidence to suggest Bloom didn't act alone. An investigation by infosec journalist Brian Krebs claimed that a second suspect, a US man named Jeremy Wade, was also behind the service. He was never charged.
These are the worst hacks, cyberattacks, and data breaches of 2018
Related malware and cybercrime coverage:
- Europol arrests GozNym malware group members
- Hacktivist attacks dropped by 95% since 2015
- North Korean cyberspies deploy new malware that harvests Bluetooth data
- Stack Overflow hacker went undetected for a week
- Chinese cyberspies breached TeamViewer in 2016
- Two crypto-mining groups are fighting a turf war over unsecured Linux servers
- The dark web is smaller, and may be less dangerous, than we think TechRepublic
- Game of Thrones has the most malware of any pirated TV show CNET