Crypto-mining worm steals AWS credentials

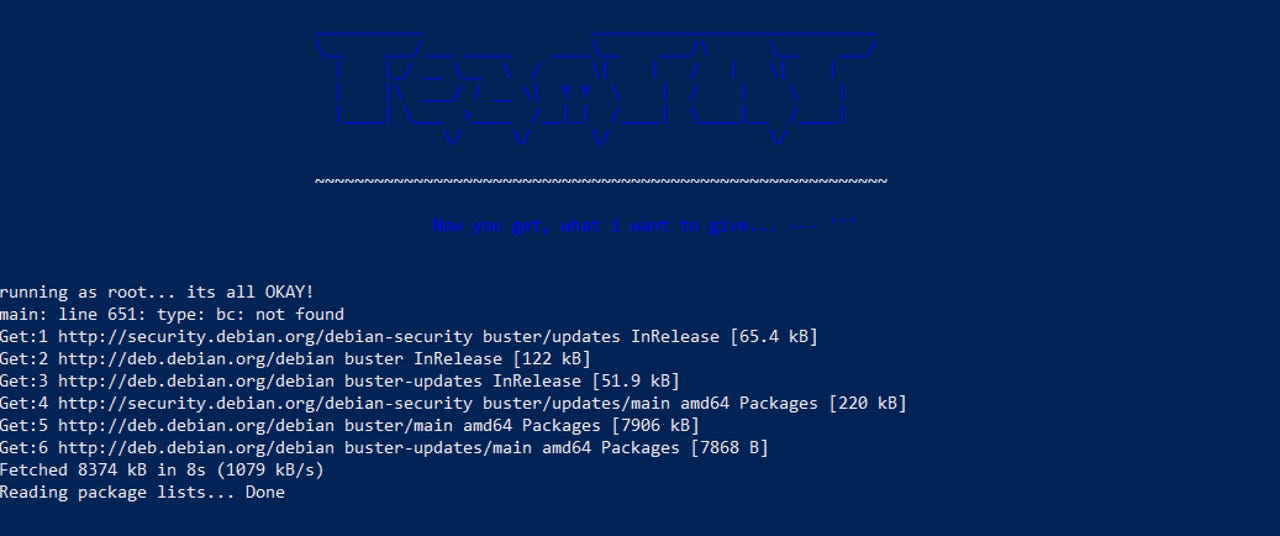
TeamTNT placing its logo on the terminals of systems it infects.
Security researchers have discovered what appears to be the first crypto-mining malware operation that contains functionality to steal AWS credentials from infected servers.
This new data-stealing feature was spotted in the malware used by TeamTNT, a cybercrime group that targets Docker installs.
The group has been active since at least April, according to research published earlier this year by security firm Trend Micro.
Per the report, TeamTNT operates by scanning the internet for Docker systems that have been misconfigured and have left their management API exposed on the internet without a password.
The group would access the API and deploy servers inside the Docker install that would run DDoS and crypto-mining malware. Their tactics are not as unique as multiple other cybercrime groups using the same playbook.
But in a new report published Aug. 17, UK security firm Cado Security says the TeamTNT gang has recently updated its mode of operation.
Cado researchers say that, besides the original functionality, TeamTNT has now also expanded its attacks to target Kubernetes installations.
TeamTNT now steals AWS credentials
But while expanding its targets base is generally pretty important, Cado researchers said there's even a bigger update -- namely a new feature that scans the underlying infected servers for any Amazon Web Services (AWS) credentials.
If the infected Docker and Kubernetes systems run on top of AWS infrastructure, the TeamTNT gang scans for ~/.aws/credentials and ~/.aws/config, and copies and uploads both files onto its command-and-control server.
TeamTNT code that steals and uploads the AWS credentials and config files.
Both of these files are unencrypted and contain plaintext credentials and configuration details for the underlying AWS account and infrastructure.
Cado researchers believe the attacker has not yet moved to use any of the stolen credentials. They said they sent a collection of canary credentials to the TeamTNT C&C server, but none of those accounts have been accessed prior to Aug. 17, when they published their research.
Nevertheless, when the attackers decide to do so, TeamTNT stands to seriously boost its profits, either by installing crypto-mining malware in more powerful AWS EC2 clusters directly or by selling the stolen credentials on the black market.
Right now, Cado has only a limited view into TeamTNT's operation, as the security firm has been able to track only a few of the Monero wallet addresses that the group uses to collect mined funds. While right now TeamTNT looks to have made only around $300, the reality is that it made many many times more, as crypto-mining botnets usually employ thousands of different wallet addresses, to make tracking or seizing funds harder.