France: Russian state hackers targeted Centreon servers in years-long campaign

France's cyber-security agency said that a group of Russian military hackers, known as the Sandworm group, have been behind a three-years-long operation during which they breached the internal networks of several French entities running the Centreon IT monitoring software.
The attacks were detailed in a technical report released today by Agence Nationale de la Sécurité des Systèmes d'Information, also known as ANSSI, the country's main cyber-security agency.
"This campaign mostly affected information technology providers, especially web hosting providers," ANSSI officials said today.
"The first victim seems to have been compromised from late 2017. The campaign lasted until 2020."
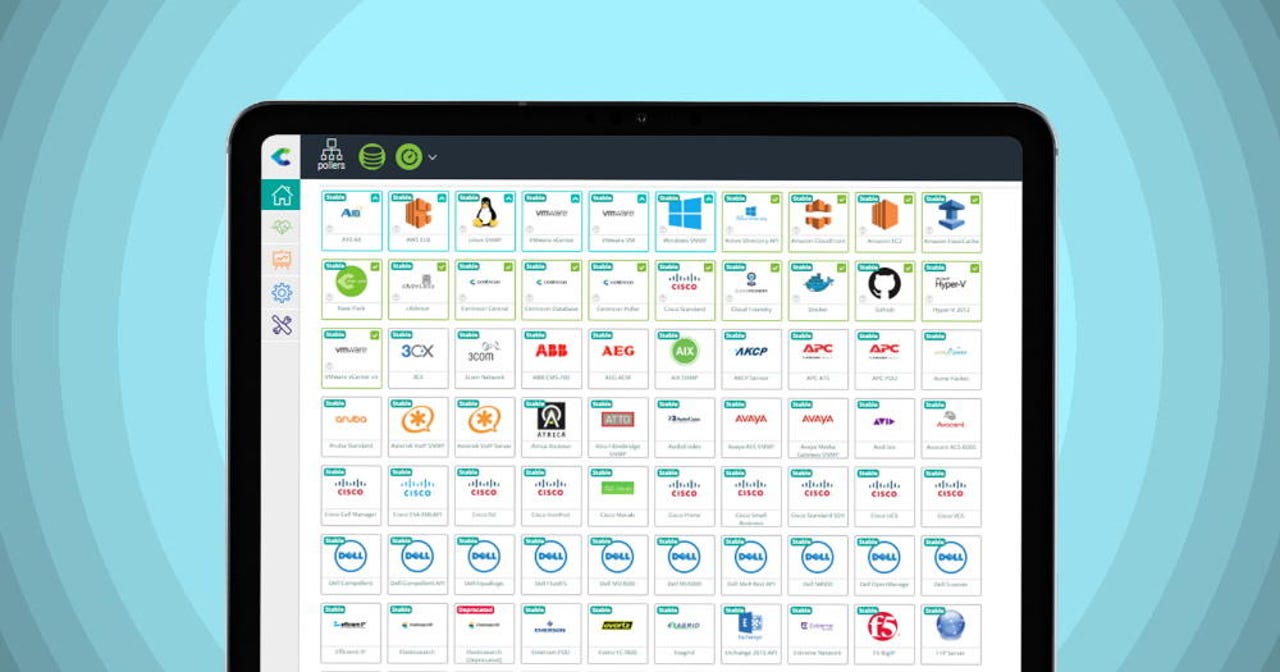
The point of entry into victim networks was linked to Centreon, an IT resource monitoring platform developed by French company CENTREON, and a product similar in functionality to SolarWinds' Orion platform.
ANSSI said the attackers targeted Centreon systems that were left connected to the internet. The French agency couldn't say at the time of writing if the attacks exploited a vulnerability in the Centreon software or if the attackers guessed passwords for admin accounts.
However, in the case of a successful intrusion, the attackers installed a version of the P.A.S. web shell and the Exaramel backdoor trojan, two malware strains that when used together allowed hackers full control over the compromised system and its adjacent network.
According to Costin Raiu, Director of the Global Research and Analysis Team (GReAT) at Kaspersky Lab, the attackers heavily relied on the P.A.S. web shell.
"This would commonly be deployed in the Centreon web server folder, (eg /usr/local/centreon/www/search.php) and created by the Apache user," Raiu said.
"In addition to the webshell, attackers also deployed the Exaramel backdoor. Exaramel is a multiplatform backdoor; Windows and Linux versions are known to exist. The Linux version is written in Golang. On infected systems, ANSSI found it was created by the Apache user, same as the P.A.S. webshell," he added.
Think links to Sandworm
In a rare step, ANSSI said it managed to link the malware used in these attacks to an advanced persistent threat (APT) group known in the cyber-security industry under the name of Sandworm.
"Sandworm is the only known group that uses Exaramel," Raiu also added in a Twitter thread yesterday.
In October 2020, the US Department of Justice formally charged six Russian military officers for their participation in cyber-attacks orchestrated by this group, formally linking the Sandworm APT to Unit 74455 of the Russian Main Intelligence Directorate (GRU), a military intelligence agency part of the Russian Army.
Cyber-attacks previously carried out by this group included the energy grid crashes across Ukraine in 2015 and 2016, the NotPetya ransomware outbreak of 2017, the attacks on the PyeongChang Winter Olympics opening ceremony in 2018, and a mass defacement of Georgian websites in 2019.
In addition, the DOJ also linked this group to attacks against France, namely to spearphishing campaigns and related hack-and-leak efforts targeting French President Macron's "La République En Marche!" political party —an operation also referred to as the Macron Leaks.
Through the release of its report today, the ANSSI is now warning and urging both French and international organizations to inspect their Centreon installations for the presence of the two P.A.S. and Exaramel malware strains, a sign that companies been breached by Sandworm attacks in previous years.
A Centreon spokesperson did not reply to a request for comment before this article's publication.
Despite the similarity in functionality between Centreon and the SolarWinds Orion apps, the Centreon attacks appear to be opportunistic exploitation of internet-exposed systems rather than a supply chain attack, as several security experts have pointed out today on Twitter.
Sandworm has been using webshells and the Linux version of the backdoor Exaramel against French entities undetected for more than three years.
— Timo Steffens (@Timo_Steffens) February 15, 2021
Initial attack vector is unclear, but malware was found on servers running Centreon (vulnerability more likely than supply-chain). https://t.co/ieUYV57hCF
Several security researchers have pointed online today that this particular campaign appears to have all the signs of a classical cyber-espionage operation. The attackers appear to have focused on stealth and data exfiltration, rather than previous Sandworm-linked attacks where the purpose was destruction.
The targeting of IT companies, and especially hosting providers, suggests the attackers might have focused on gaining access to email servers, which are often hosted or provided as part of web hosting packages.
This pattern of attacks also fits in with an NSA alert the US government published last spring, linking the Sandworm group to attacks targeting Exim email systems.