Free decryptor available for ThiefQuest ransomware victims

Cyber-security firm SentinelOne has released today a free decryptor app that can help victims of the ThiefQuest ransomware recover their locked files.
The ThiefQuest ransomware -- initially identified under the name of EvilQuest -- targets only Mac users.
ThiefQuest's classification as a ransomware strain is tenuous. The malware is a smorgasbord of malicious code that includes modules for logging keystrokes, installing a reverse shell for backdoor access to infected hosts, code for stealing cryptocurrency-related data, and encrypting files (the so-called ransomware part).
Security researchers have seen the malware distributed in the wild for more than a month, usually hidden inside pirated software shared on torrent portals and online forums.
ThiefQuest contains a faulty ransomware component
Based on previous analysis [1, 2, 3], the malware is considered to be in its early stages of development, and, as a result, some of its components don't seem to function correctly.
Unfortunately for victims, the ransomware part is one of those faulty components and appears to contain many unpolished features.
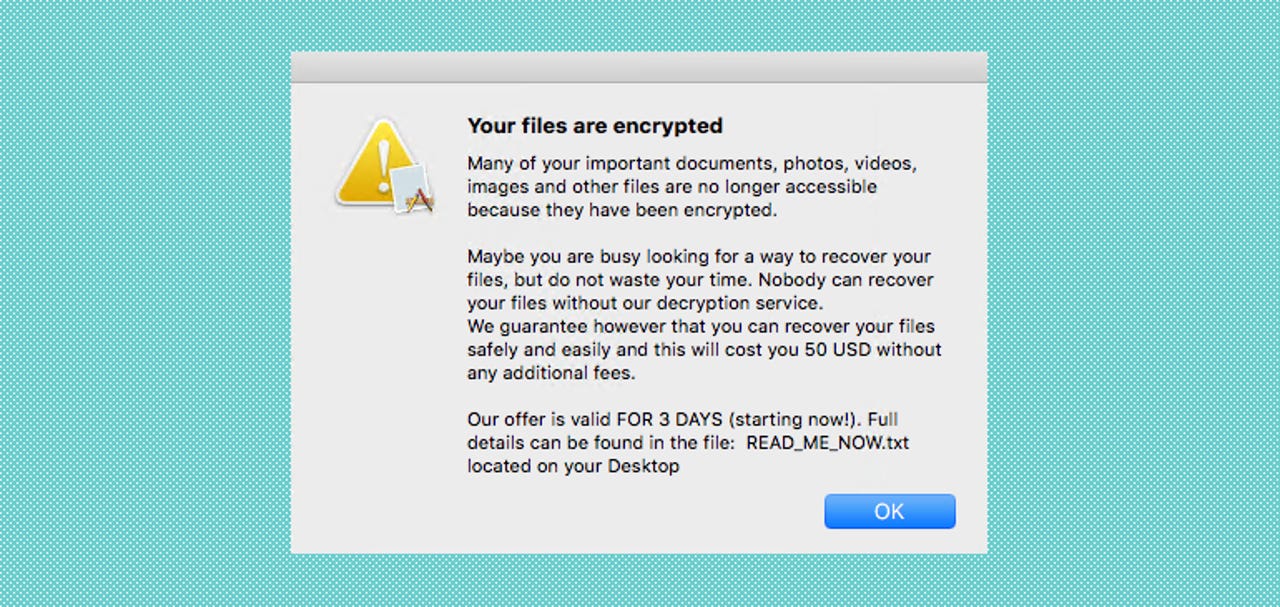
Researchers say that while ThiefQuest encrypts files as soon as it infects a macOS system, the malware does not come with a mechanism for tracking users who paid the ransom demand, nor does it provide a contact method so users can contact the ThiefQuest team with details about their payment and receive instructions on how they could unlock their files -- a detail that is obvious from reading its ransom note below.
Since early June, users who have been infected with ThiefQuest have had their files permanently locked without a method of recovering their files -- even if they paid the ransom demand.
SentinelOne releases free decryptor
However, security researchers from SentinelOne announced that after analyzing the ransomware source code and the differences between encrypted files and their original versions, they were able to reverse engineer ThiefQuest's encryption mechanism.
In a technical blog post published earlier today, researchers said that ThiefQuest uses a simple symmetric-key encryption system based on the RC2 algorithm and that the ransomware stores the encryption/decryption key inside each locked file.
The SentinelOne teams said it was able to create an application (known as a decryptor) that extracts this key and unlocks victims' files.
SentinelOne's ThiefQuest decryptor is provided in a binary form for now but the company said it plans to open-source the code at a later date.
The decryptor can be downloaded directly from this link or via the download link at the bottom of the SentinelOne's technical report here. A video demo on how to use the decryptor is available here.
However, a new report from Malwarebytes published today also warns that besides encrypting files, ThiefQuest also infects other local files in a virus-like beahavior, so additional clean-up may be necessary to prevent future re-infections or the infection of other Mac systems.