Google finds Android zero-day impacting Pixel, Samsung, Huawei, Xiaomi devices

Google disclosed today that they found evidence of an Android unpatched vulnerability being used in attacks in the real world -- a so-called "zero-day."
The vulnerability resides in the Android operating system's kernel code and can be used to help an attacker gain root access to the device.
Ironically, the vulnerability was patched in December 2017 in Android kernel versions 3.18, 4.14, 4.4, and 4.9, but newer versions were found to be vulnerable.
Google researchers believe that the vulnerability impacts the following Android phone models, running Android 8.x and later:
- Pixel 2 with Android 9 and Android 10 preview
- Huawei P20
- Xiaomi Redmi 5A
- Xiaomi Redmi Note 5
- Xiaomi A1
- Oppo A3
- Moto Z3
- Oreo LG phones
- Samsung S7, S8, S9
Google researchers also said that the "exploit requires little or no per-device customization," meaning it should be able to work on a wide range of handsets, although they have not confirmed this with manual reviews, as they did for the devices listed above.
Google: Zero-day linked to NSO Group
The vulnerability was discovered by Google's Project Zero team, and later confirmed to have been used in real-world attacks by the company's Threat Analysis Group (TAG). These are the two teams that discovered last month a batch of 14 zero-days being used against iOS users.
However, the Android zero-day and the iOS zero-days appear to be unrelated. While the attacks on iOS users have been linked to a Chinese state-sponsored group conducting surveillance operations against their own citizens, details about the Android zero-day are currently limited.
Google's TAG said it believes the Android zero-day is the work of NSO Group, a well-known Israeli-based company known to sell exploits and surveillance tools.
The company has been criticized for selling hacking tools to oppressive regimes, but facing rising criticism, has recently pledged to fight customers who abuse its tools to spy on innocents or political opponents. Responding to a request for comment from ZDNet, the company had the following to add, denying that the exploit is one of their own.
"NSO did not sell and will never sell exploits or vulnerabilities," an NSO Group spokesperson said. "This exploit has nothing to do with NSO; our work is focused on the development of products designed to help licensed intelligence and law enforcement agencies save lives."
Not as dangerous as it could have been
The good news is that the Android zero-day is not as dangerous as other past zero-days. For starters, it's not an RCE ( remote code execution) that can be exploited without user interaction. There are certain conditions that need to be met before an attacker can exploit this vulnerability.
"This issue is rated as High severity on Android and by itself requires installation of a malicious application for potential exploitation," a spokesperson for the Android Open Source Project said. "Any other vectors, such as via web browser, require chaining with an additional exploit.
"We have notified Android partners and the patch is available on the Android Common Kernel. Pixel 3 and 3a devices are not vulnerable while Pixel 1 and 2 devices will be receiving updates for this issue as part of the October update," the Android team said.
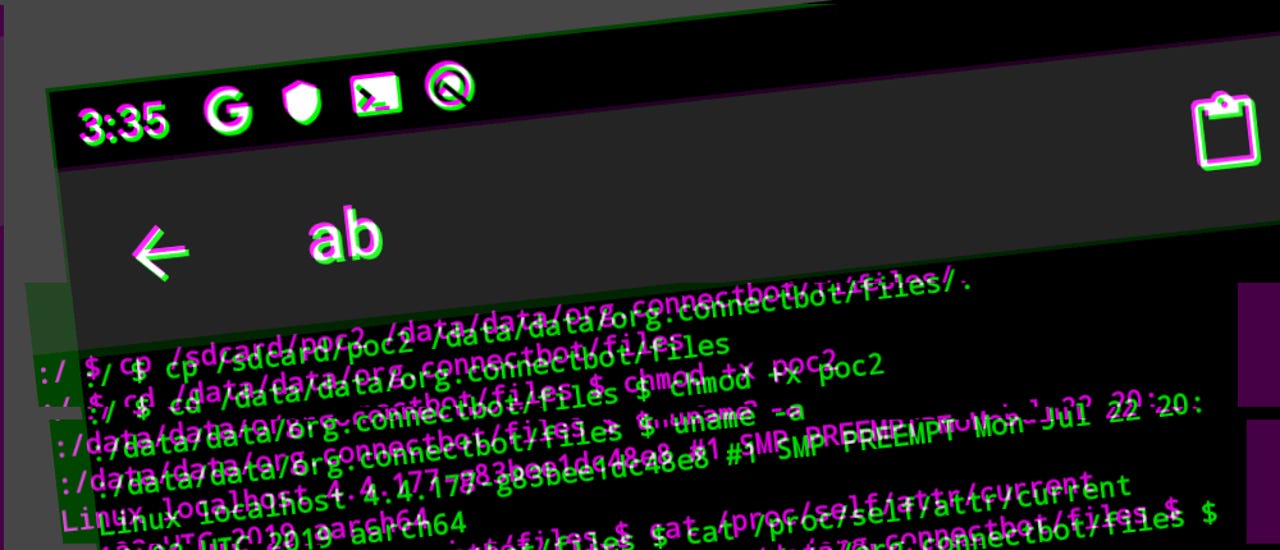
The zero-day is now being tracked as CVE-2019-2215. This bug tracker entry from the Project Zero team holds proof-of-concept code and additional details for security researcher who want to reproduce the bug and test other devices.
Updated at 9:25am ET with comment from NSO Group.