Google lays bare security flaws in anti-malware product with 250 million users

Malwarebytes has now launched a bug-bounty program, offering up to $1,000 to researchers who report flaws in its products.
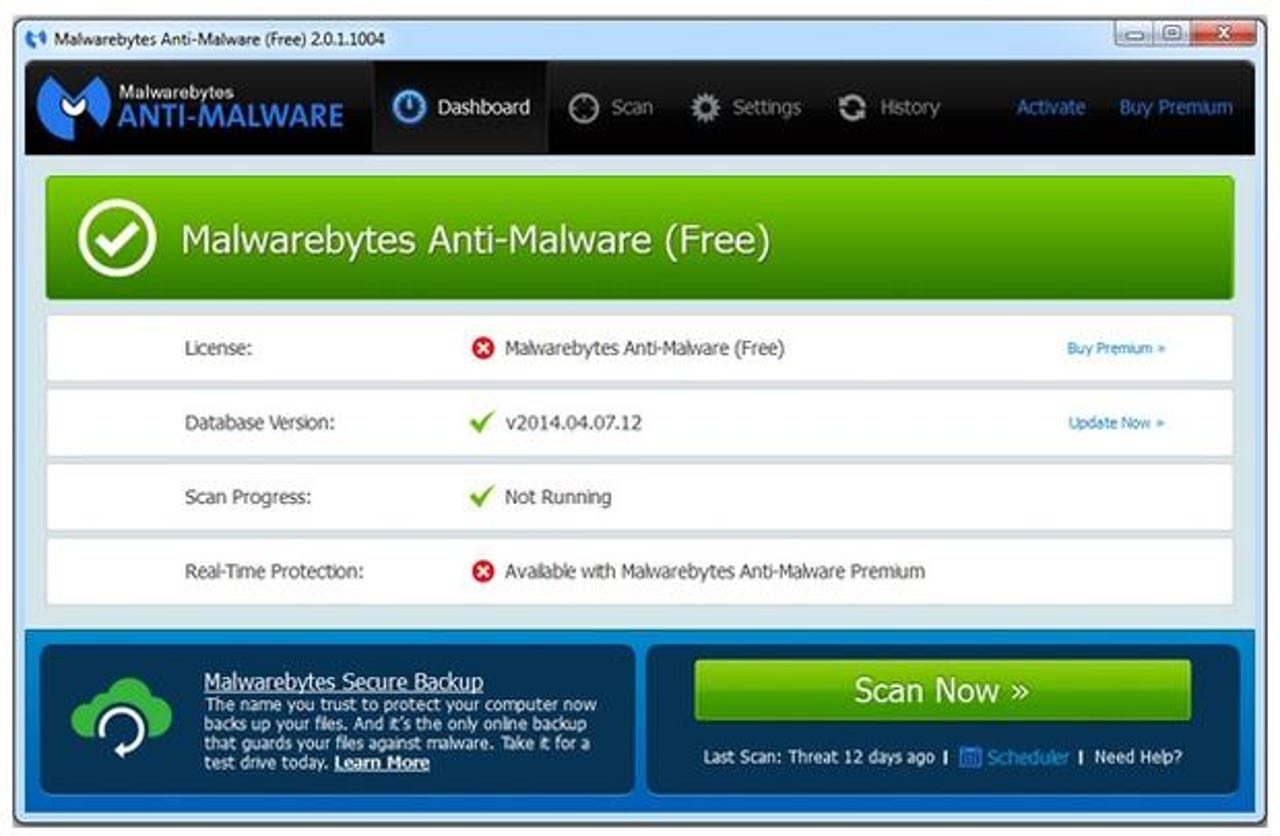
Malwarebytes says it could take three to four weeks to fix security flaws found by Google in its popular anti-malware product .
Google's bug-hunting squad, Project Zero, first notified the internet-security firm of the four vulnerabilities in November but on Tuesday went ahead and detailed the separate flaws and attack methods in a redacted report published on the group's bug repository.
Project Zero researcher Tavis Ormandy found that the Malwarebytes client was fetching malware signature updates over unencrypted HTTP, leaving those definitions open to tampering in a man-in-the-middle attack.
The researcher only probed Malwarebyte's consumer edition. However, the bugs also affect the company's premium product.
Marcin Kleczynski, CEO and founder of Malwarebytes, said enabling 'self-protection' under settings should mitigate the problem while it works on a proper fix.
Malwarebytes recently noted that its software was running on 250 million machines worldwide.
Project Zero offers vendors 90 days to fix flaws and alert customers before publishing details of bugs its researchers have found. Malwarebytes appears to have been given an extension, with its grace period technically having expired on January 11.
Kleczynski apologized to users for the flaws and, in response to Ormandy's efforts, has launched a bug-bounty program, offering up to $1,000 to researchers who report flaws in its products.
"Unfortunately, vulnerabilities are the harsh reality of software development," Kleczynski said. "A vulnerability disclosure program is one way to accelerate the discovery of these vulnerabilities and empower companies like Malwarebytes to fix them."
Bugs in security products do pose a unique threat to users due to the sensitive permissions they have.
They have also come under the spotlight following a report by The Intercept that Britain's GCHQ had sought a warrant to probe Kaspersky antivirus for security flaws to aid its own hacking efforts.
The NSA has also taken a keen interest in non-US antivirus products, including Kaspersky, ESET, and F-Secure.
Malwarebytes anti-malware is the latest security software to be lanced by Ormandy, who has found serious flaws in products from AVG, Kaspersky, FireEye, Trend Micro, ESET, Sophos, and most recently in Comodo's Chromodo Chrome fork.
In all cases, products that are designed to protect users from threats exposed them to further risks through insecure code.