'ZDNET Recommends': What exactly does it mean?
ZDNET's recommendations are based on many hours of testing, research, and comparison shopping. We gather data from the best available sources, including vendor and retailer listings as well as other relevant and independent reviews sites. And we pore over customer reviews to find out what matters to real people who already own and use the products and services we’re assessing.
When you click through from our site to a retailer and buy a product or service, we may earn affiliate commissions. This helps support our work, but does not affect what we cover or how, and it does not affect the price you pay. Neither ZDNET nor the author are compensated for these independent reviews. Indeed, we follow strict guidelines that ensure our editorial content is never influenced by advertisers.
ZDNET's editorial team writes on behalf of you, our reader. Our goal is to deliver the most accurate information and the most knowledgeable advice possible in order to help you make smarter buying decisions on tech gear and a wide array of products and services. Our editors thoroughly review and fact-check every article to ensure that our content meets the highest standards. If we have made an error or published misleading information, we will correct or clarify the article. If you see inaccuracies in our content, please report the mistake via this form.
How to use Tor browser (and why you should)

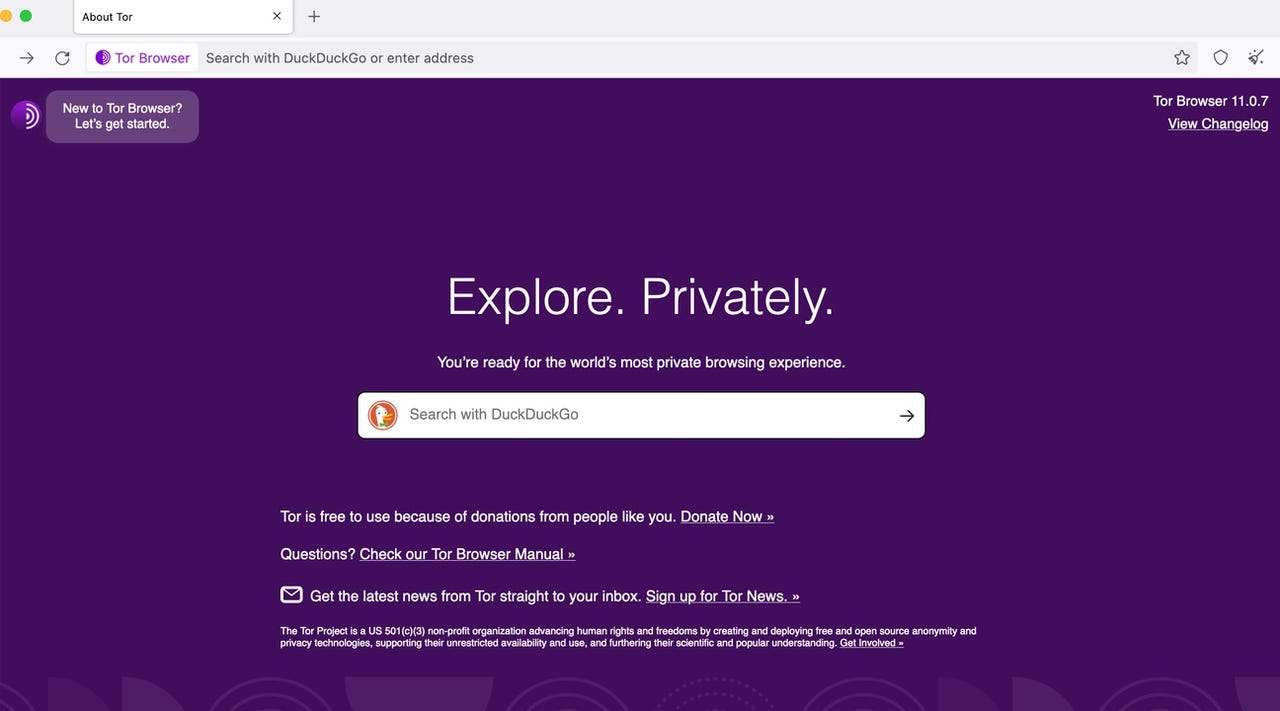
A while ago, I wrote a piece on the best way to ensure your privacy with a web browser. A part of that advice was to use the Tor browser. In simplest terms, you cannot get more privacy and security from a web browser than when using Tor. And given how important privacy and security is now, Tor should be on your radar.
Also: The best browsers for privacy
The Tor browser uses the Onion network to ensure privacy and security. What is the Onion network? First off, Tor is short for "The Onion Router". When using the Onion network, all traffic is encapsulated in layers of encryption, which are transmitted through a series of nodes called "onion routers". As the traffic passes through a node, it peels away a single layer that reveals the next destination for the data. This makes it very difficult for a third party to trace your internet activity (more than any other browser).
Now that you know what Tor is, let me show you how easy it is to use.
How to connect Tor to the Onion network
What you'll need: The only thing you'll need is Tor Browser installed on your desktop or mobile device. I'll demonstrate Tor Browser on Linux, but the platform you use won't matter. You can download the Tor Browser for your desktop from the official download page. The link for the Android version will take you to a page with downloads for .apk files. On that same page, you'll find a link to the Google Play Store Tor entry. I would suggest installing Tor on Android from the Google Play Store.
Also: Your guide to the dark web and how to safely access .onion websites
When using Linux, you can also install Tor from the standard repositories, which means it should be available to install from your desktop app store.
Once you have Tor installed, proceed to step one.
1. Open Tor Browser
The first thing to do is open Tor Browser, which you can do from your desktop menu.
2. Connect to Tor
If you've installed Tor on Linux from the standard repository, when you first launch it, it will automatically download the latest version of Tor for you.
Once opened, you'll see a button labeled Connect. When you open Tor, it is not set to automatically connect to the Onion network. Until you connect to the Onion network, the Tor browser cannot be used. I would suggest enabling the connection automatically by clicking the checkbox labeled "Always connect automatically". Once you've done that, click Connect and Tor will work its magic.
Also: This might be my new favorite browser
The connection won't happen immediately, so give the browser time to complete the process. If you find Tor cannot make the connection, close the browser and try again. I've had to do this task almost every first time I've launched Tor. The next time you open Tor, it shouldn't have any problem connecting.
Once Tor is connected, you can start using it as you would any browser.
Enable automatic connection after you're certain Tor works as expected.
3. Resolve Error: Forbidden
I have discovered, however, that some sites cannot be viewed with Tor browser. For example, when attempting to view ZDNET.com, Tor displays a 403 Error: Forbidden. Your client does not have permission to get a URL from this server.
Should that occur, click the padlock icon to the left of the URL in question and, from the popup, click New Circuit for this Site. Once the new circuit is created, the site should load as expected.
Fixing the 403 error.
And that is the why and how of using the Tor browser. Even though you'll find it slower than your average browser, the added privacy and security you get from Tor is very much worth the reduction in speed.
Also: The easiest thing you can do to keep your phone secure
I use Tor when I require heightened security for a particular site or service (otherwise, I just use Firefox). Give this browser a try and see if you don't find the added privacy and security worth the effort.