IoT botnet targeting your enterprise? Nope. Just a kid with an ExploitDB account

Headlines like "IoT botnet targets enterprise devices" sound very scary, but the reality is that many of these botnets are the work of kids playing around with random exploits they found online, and many of these botnets die out in a matter of weeks as the authors get bored or move on to other projects.
Security
The prime example of this is Kepler, an IoT botnet that made the news last month because of its ability to infect signage TVs and presentation systems, two types of devices found in enterprise networks.
On a first read, any report on Kepler would seem like the botnet author was intentionally aiming to get a foothold on corporate networks so they could later deploy more potent malware.
Kepler authors: We were just having fun!
However, things aren't actually so. In a recorded interview with Ankit Anubhav, security researcher for NewSky Security, and published on Soundcloud, the botnet's two authors admitted that they built the botnet for fun, adding exploits taken from the ExploitDB website at random.
"We're just a couple of friends having fun," the two said before admitting that this was actually the second botnet they put together, after also creating one last year.
Despite Kepler generating some scary headlines, the duo didn't take the work on their botnet seriously, admitting that they didn't even bother counting the number of devices their botnet infected.
Further, the botnet didn't use 27 exploits, as Palo Alto Networks initially reported, but 43, according to Nipsu, one of the Kepler authors --all, of course, chosen at random.
According to the interview, the two hackers, one of which is a minor, were just testing random vulnerability exploits, wanting to see which one gathered more bots.
The two said they have no current plans to sell the Kepler botnet to other cybercrime gangs or rent it for DDoS attacks --a common practice and a source of profit for many IoT botnet authors.
Kepler is a trend, not an edge case
These revelations aren't just an isolated edge case in the IoT botnet scene. Many botnet authors are just kids taking their first steps in the world of programming and cybersecurity, playing around with exploits, before realizing the legal problem they could be in, and moving on to other careers --or getting arrested [1, 2].
A large part of the IoT botnet operators listed on this Top 20 IoT Blackhat Hackers list have now moved on from running IoT botnets.
One of them, Switch (#15 on the list), offered his insights on the current IoT botnet scene. Asked how easy it would be to integrate code taken from ExploitDB into a botnet, Switch, who is the author of many YouTube tutorials on building IoT malware, provided the following answer.
"If you're talking auto scanners such as [the ones looking for] Huawei, Realtek, ThinkPHP etc., it's VERY easy," Switch said. "There is only a few lines of code to it. I have made a tutorial before on how to do it as it only takes a few minutes."
"I have seen a few people write scanners [for vulnerable devices] into sources before, and by what I can see it's mainly copying and pasting," he said.
Anubhav, a security researcher who spends his whole day looking at IoT botnets, also shares Switch's opinion.
"The majority of IoT exploit code is heavily borrowed from ExploitDB," Anubhav said.
"In many cases, the vulnerabilities are not able to infect a lot of devices, hence the attackers are trying as many vulnerabilities as they can to further assess which one is going to reap maximum benefits."
It's a Mirai/Gafgyt party
But besides Kepler, another recent example of an IoT botnet that is not as dangerous as it looks is the one documented by Trend Micro this week.
This botnet, which has no particular name, runs on a variant of the Bashlite (Gafgyt) IoT malware, which is used as a skeleton and customized with several ExploitDB exploits on top --which in this case targeted Belkin WeMo devices.
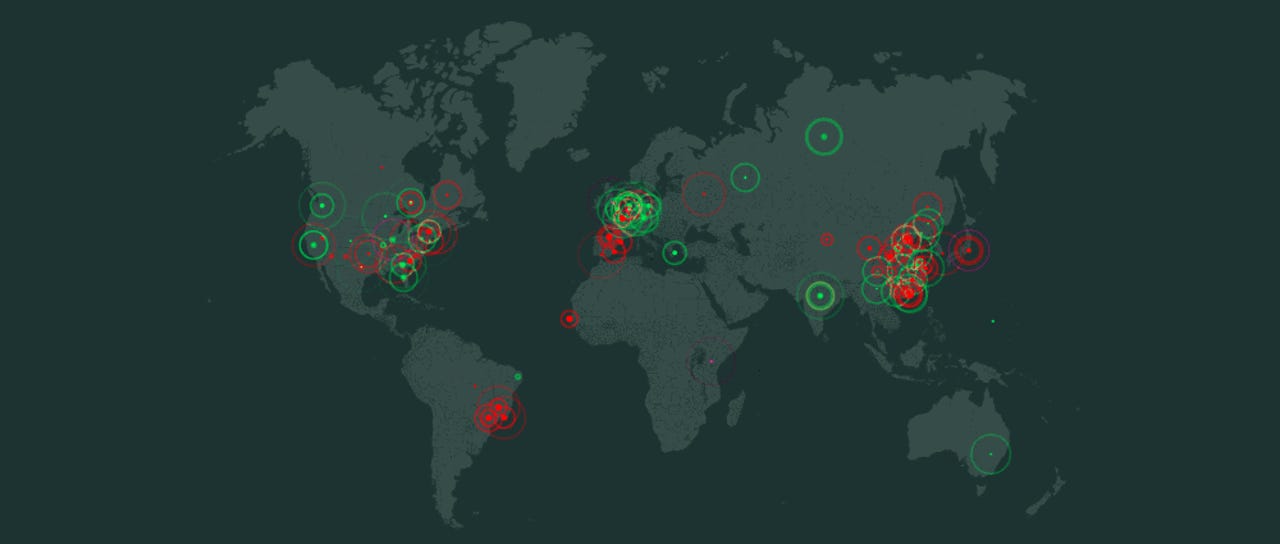
The anatomy of this botnet is representative of the whole IoT malware scene these days. Botnet operators use the source code of IoT malware that previously leaked online in past years as a wireframe for the delivery of random exploits they've copied from ExploitDB.
In most cases, these botnets are built on the Bashlite (Gafgyt) or Mirai IoT malware strains, and only very rarely does a true malware coder come around to innovate and create new malware strains --such as hackers like Wicked or the Janit0r (the BrickerBot author).
Cybercrime and malware, 2019 predictions
Related malware and cybercrime coverage:
- Over 58,000 Android users had stalkerware installed on their phones last year
- A dozen US web servers are spreading 10 malware families, Necurs link suspected
- Asian woman with a thumb drive containing malware arrested at Mar-a-Lago
- Bashlite IoT malware upgrade lets it target WeMo home automation devices
- Facebook closes groups that offered phishing services, hacked data for sale
- Hacker group has been hijacking DNS traffic on D-Link routers for three months
- How the United Nations helps fight global cybercrime TechRepublic
- Apple removed popular app that was secretly stealing your browser history CNET