Israeli companies targeted with new Pay2Key ransomware

Several companies and large corporations from Israel have been breached and had their systems encrypted using a new strain of ransomware named Pay2Key, in what appears to be a targeted attack against Israeli networks.
The first attacks were seen in late October but have now grown in numbers while also remaining contained to Israel.
"As days go by, more of the reported ransomware attacks turn out to be related to the new Pay2Key ransomware," Israeli cyber-security firm Check Point said in a security alert published today.
According to the company, attacks usually happened after midnight, when companies have fewer IT employees at work.
The initial entry point for all intrusions is currently believed to be weakly secured RDP (Remote Desktop Protocol) services.
Access to company networks appears to have been obtained "some time before the attack," but once the ransomware crew begins its intrusion, it usually takes them an hour to spread to the entire network and encrypt files.
To avoid having their activities detected, the Pay2Key operators usually set up a pivot point on the local network, through which they proxy all their communications to reduce their detectable network footprint.
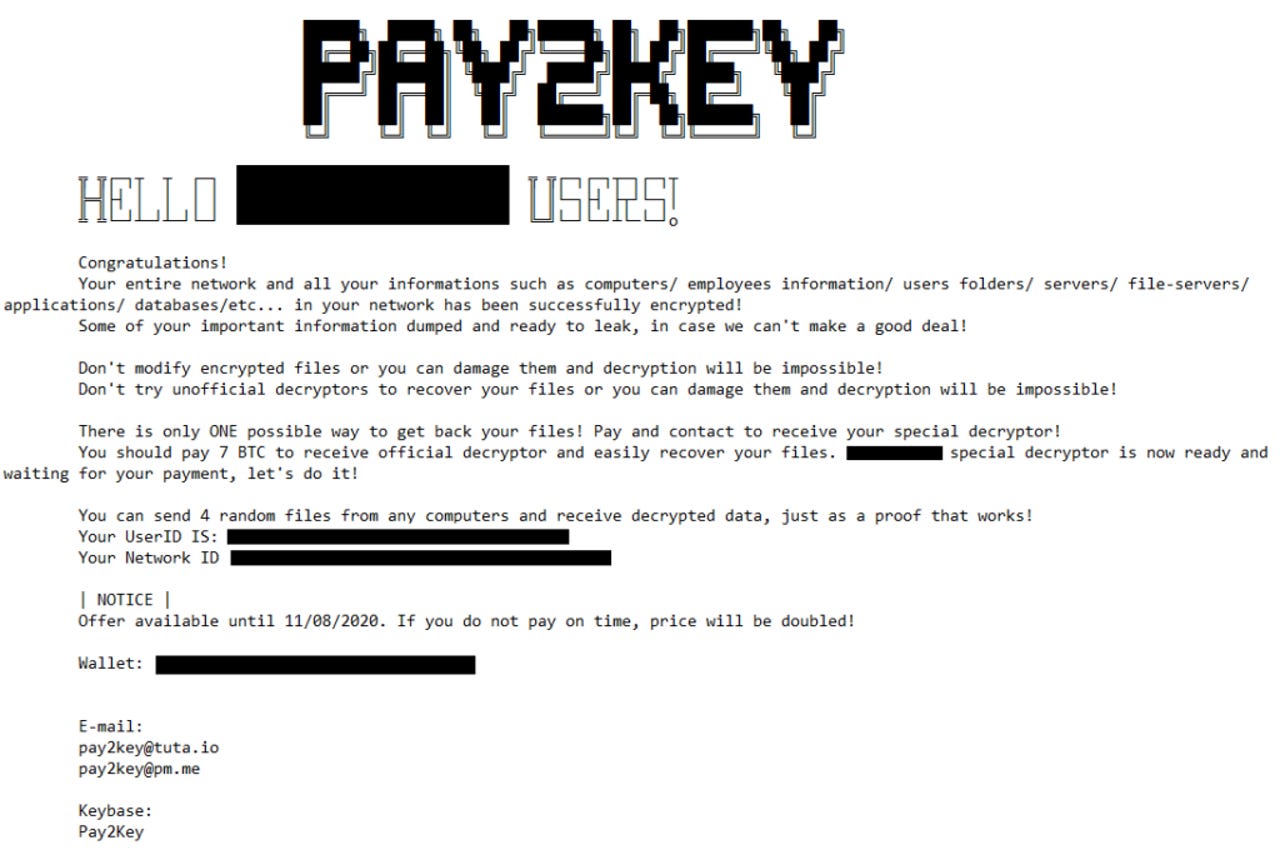
Once the encryption ends, ransom notes are left on the hacked systems, with the Pay2Key gang usually asking for payments of 7 to 9 bitcoins (~$110K-$140K).
Based on current analysis, Check Point said the encryption scheme appears to be solid (using the AES and RSA algorithms), which unfortunately has prevented the company from creating a free decrypter for victims.
Researchers say the ransomware has been created from scratch, with no overlaps with other known ransomware strains, and appears to have been named "Cobalt" during a previous/development phase.
Some sleuthing from the Check Point team has also linked the ransomware to a Keybase account using the same Pay2Key name, registered earlier this year in June, but it is currently unclear who developed the ransomware and why are they targeting only Israeli companies.
Great writeup by @_CPResearch_ on "Pay2Key" #Ransomware. Can confirm 3 unique businesses in Israel submitted to ID Ransomware in the past week.https://t.co/OcFZ9Wrxs1 pic.twitter.com/XYhJl4JzEV
— Michael Gillespie (@demonslay335) November 6, 2020