KDE rips out ability for KConfig to run shell code

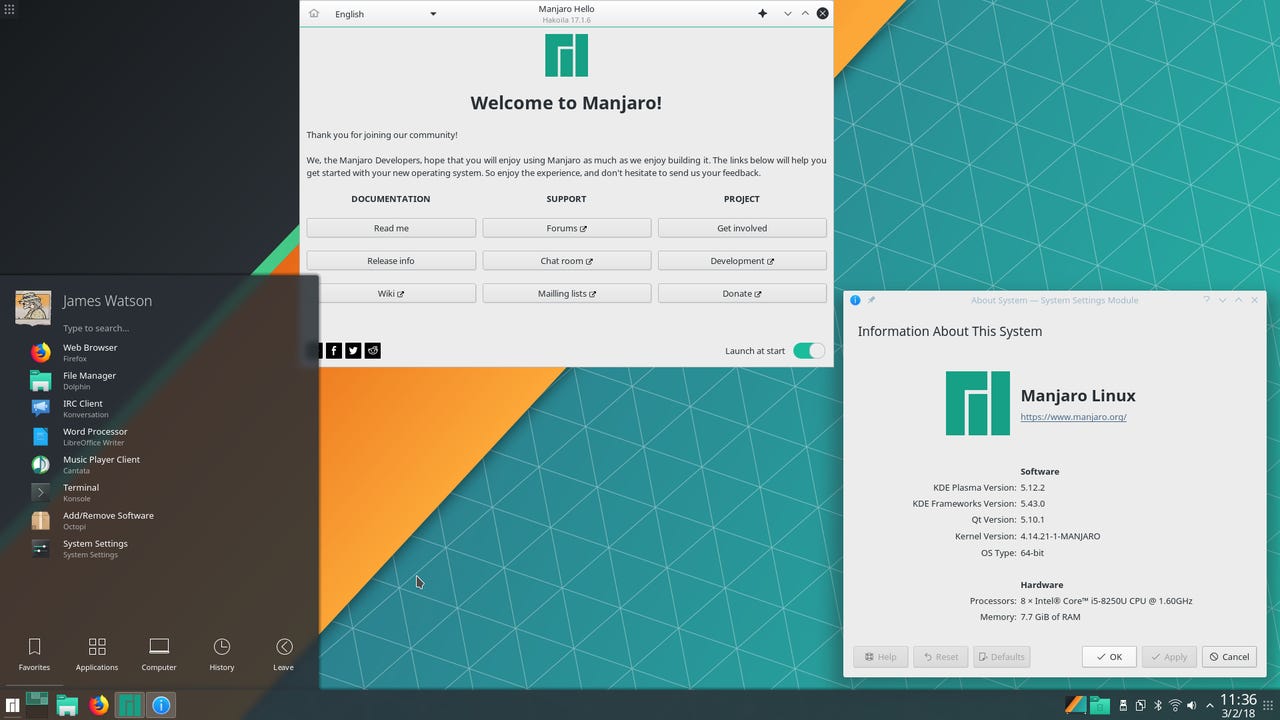
Manjaro Linux - KDE Desktop
KDE has fixed a vulnerability within its KDE Framework that allowed for malicious code execution simply by viewing a .desktop file, by removing the feature being exploited altogether.
Earlier this week, a security researcher Dominik Penner published a proof of concept that showed how users could be compromised simply by viewing a malicious .desktop file, which is typically used to show an icon for a file or directory, in the KDE file browser.
The researcher did not notify KDE before dropping the vulnerability.
KDE responded on Wednesday by removing the feature to have shell commands as values in the KConfig files, which was described as an intentional feature that allowed for flexibility.
"A file manager trying to find out the icon for a file or directory could end up executing code, or any application using KConfig could end up executing malicious code during its startup phase for instance," a KDE Project security advisory said.
"After careful consideration, the entire feature of supporting shell commands in KConfig entries has been removed, because we couldn't find an actual use case for it."
KDE said anyone that uses the feature should contact the project, in order to determine whether creating a "secure solution" is needed.
"Thanks to Dominik Penner for finding and documenting this issue (we wish however that he would have contacted us before making the issue public) and to David Faure for the fix," the advisory said.
Users of KDE Frameworks 5 would update to 5.61.0, while those on kdelibs should apply the patch in the advisory.
Related Coverage
Unpatched KDE vulnerability disclosed on Twitter
Just viewing --not running-- a malicious .desktop or .directory file inside a file browser can run malicious code on a user's system.
New long-term support version of Linux Mint desktop released
The best Linux desktop gets a refresh that will last users until 2023.
The VR Linux desktop is on its way
Want to use the GNOME or KDE Linux desktops on your virtual reality headset? A new open-source project aims to let you play games and use your Linux desktop with your VR head-mounted display.
Debian 10 'Buster' Linux arrives
Over two years in the making, the latest version of Debian Linux arrives.
First truly open-source smartphone? Necuno unveils its KDE on Linux handset
Necuno hopes its forthcoming Linux smartphone will offer users an escape from the walled gardens created by Google and Apple.