Microsoft delivers public preview of Azure Bastion service for remotely accessing VMs more securely

More Microsoft
Bastion hosts are special purpose computers on networks designed specifically to withstand attacks. So it's not too surprising that Microsoft named its newest Azure service after these devices, given its purpose.
The Azure Bastion Service is, in a nutshell (as tweeted by Azure Chief Technology Officer Mark Russinovich) a "service for secure access to your off-Internet VMs." As of today, June 18, it is now in public preview.
A slightly longer explanation via Microsoft's blog post announcing the service:
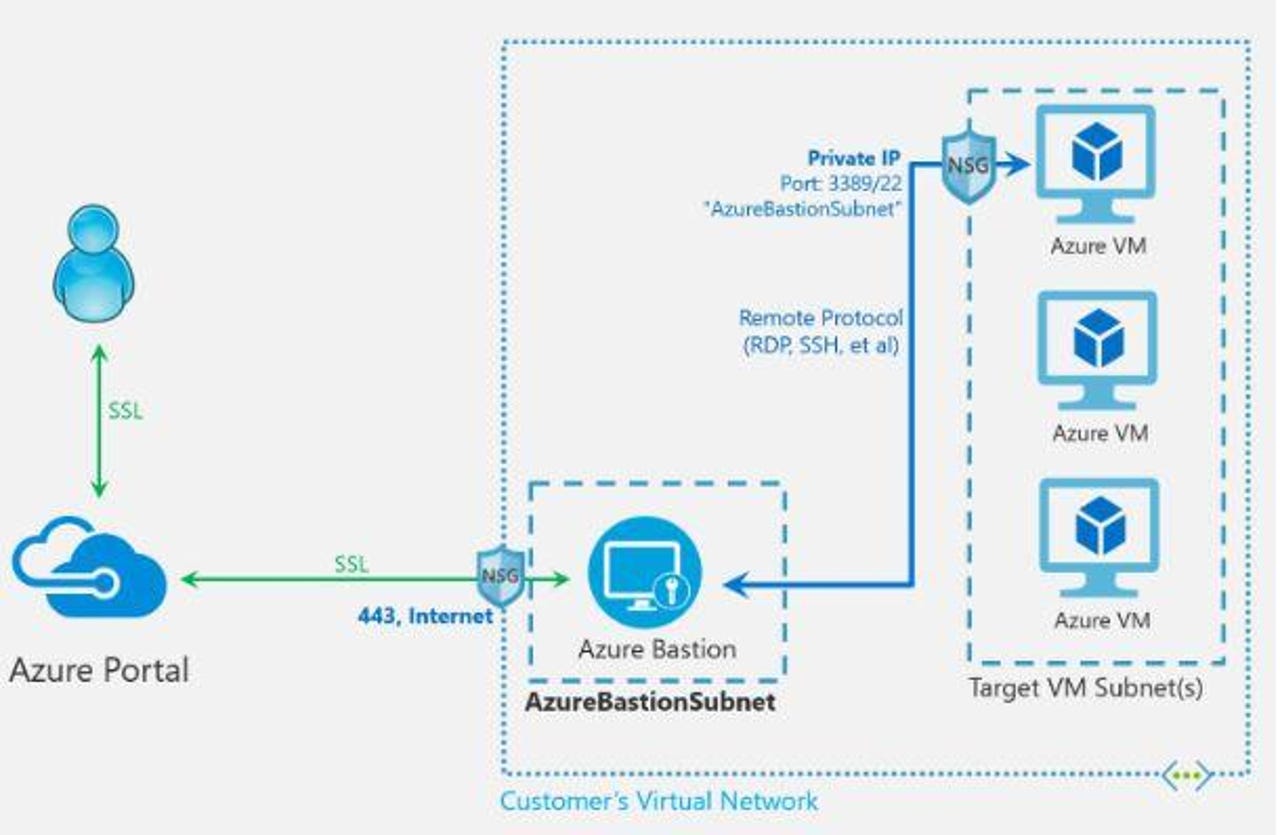
"Azure Bastion is a new managed PaaS service that provides seamless RDP and SSH connectivity to your virtual machines over the Secure Sockets Layer (SSL). This is completed without any exposure of the public IPs on your virtual machines. Azure Bastion provisions directly in your Azure Virtual Network, providing bastion host or jump server as-a-service and integrated connectivity to all virtual machines in your virtual networking using RDP/SSH directly from and through your browser and the Azure portal experience. This can be executed with just two clicks and without the need to worry about managing network security policies."
Microsoft officials said they've been working with "hundreds" of customers leading up to the preview. Customers who participated wanted an easy way "to deploy, run and scale jump-servers or bastion hosts within our Azure infrastructure," Microsoft's post by Yousef Khalidi, Corporate Vice President of Azure Networking, adds.
Bastion allows users to initiate Remote Desktop Protocol (RDP) and SSH sessions directly int he Azure portal. No public IP is required on Azure virtual machines, which limits exposure of users' infrastructure to the public internet. And it delivers increased protection against external port scanning.
Moving forward, Khalidi said, Microsoft is looking to add Azure Active Directory integration for single sign-on and Multi-Factor Authentication for RDP/SSH connections at some point. Microsoft also is working to add support for native RDP/SSH clients to the service.
Pricing details for Azure Bastion and more info is here.