Microsoft reveals audacious plans to tighten security with Windows 10

Most of the early coverage of the Windows 10 Technical Preview has focused on the new Start menu, virtual desktops, and other highly visible parts of the user experience. But even in these early builds there are hints of much more momentous changes to come, especially in the crucial realm of security.
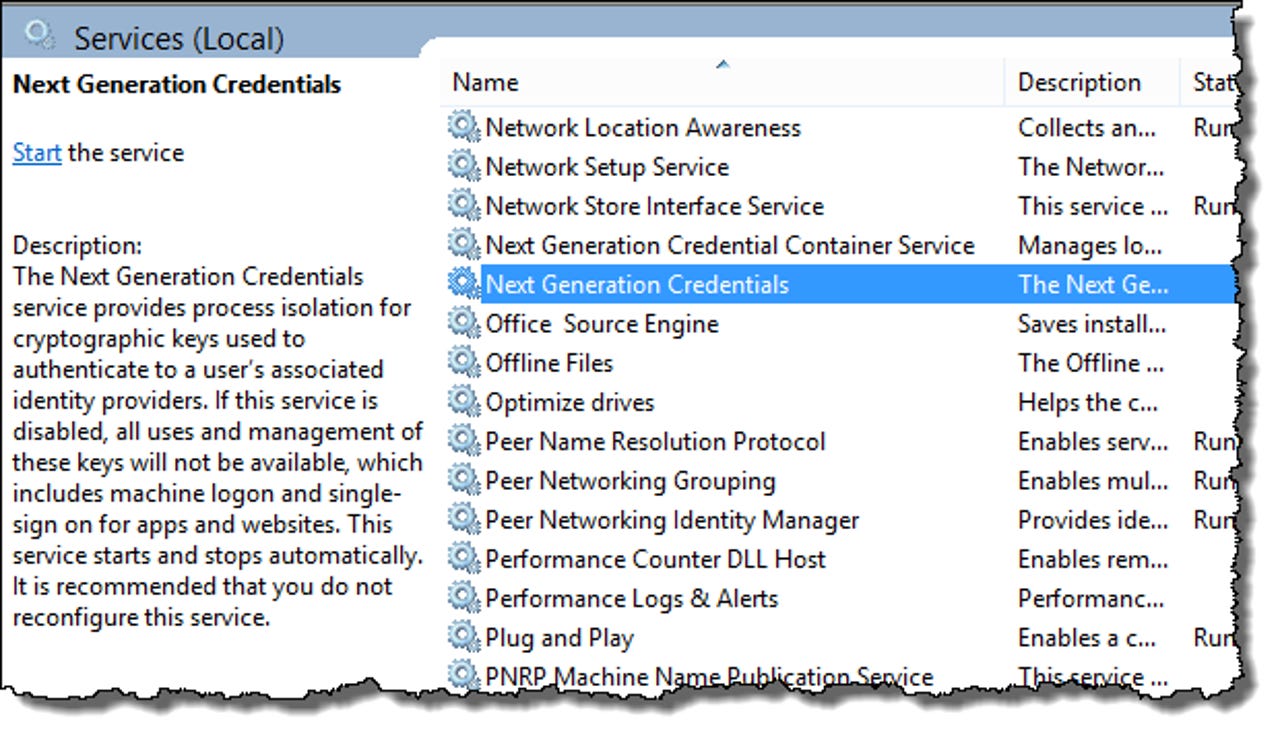
The most tantalizing hint so far has been a new service called Next Generation Credentials, which is installed but not started in the most recent preview builds.
Today, Microsoft revealed more details about its plans to "move the world away from the use of single factor authentication options, like passwords." The feature, which isn't currently enabled in Windows 10 Technical Preview builds, will allow the owner of a Windows 10 device (PC, tablet, or phone) to enroll that device as trusted for the purposes of authentication. In combination with a PIN or biometric proof, such as a fingerprint, the user will be able to sign in to any supported mobile service.
The PIN, Microsoft says, can be any combination of alphanumeric characters--it doesn't have to be restricted to a short numeric code. If that PIN is stolen in a database breach or phishing attack, the thief will be unable to access any services, because the hardware part of the two-factor authentication requirement isn't present. Likewise, a stolen device without the necessary PIN will be useless.
More Windows 10
The authentication scheme isn't proprietary. Instead, it's based on standards from the FIDO Alliance, whose membership includes a who's who of computing giants (Google, Microsoft, Lenovo, and more), banking and payments companies (BofA, PayPal, Visa and MasterCard), and established security firms like RSA and IdentityX.
On the device itself, the required public and private keys can be issued by an enterprise using its existing PKI infrastructure, or for consumer devices they can be generated and securely stored by Windows 10 itself.
According to Microsoft, Windows 10 users will be able to enroll any or all of their devices with these new credentials. As an alternative, they can choose to enroll a single device, which then serves as a virtual smart card. A mobile phone, for example, can offer two-factor authentication using Bluetooth or WiFi for signing in on local devices or accessing remote resources.
The user access tokens themselves will be stored in a virtualized secure container (running on top of Hyper-V technology), eliminating the effectiveness of common attacks such as Pass The Hash.
In today's announcements. Microsoft also laid out two new features in Windows 10 that will tighten security for its enterprise customers.
The first is a set of information-protection capabilities that make it possible to protect corporate data even on employee-owned devices. Windows 10, the company says, will allow network administrators to define policies that automatically encrypt sensitive information, including corporate apps, data, email, and the contents of intranet sites.
Read this
Because support for this encryption will be built into the APIs for common Windows controls, such as Open and Save dialog boxes, it will be available to all Windows apps that use those controls. For tighter security, administrators can create lists of apps that are allowed to access encrypted data as well as those that are denied access--a network administrator might choose to deny access to cloud services such as Dropbox, for example.
A final security measure is potentially a big winner for organizations with high-security needs, such as banks and other regulated industries as well as defense contractors and government agencies concerned about online espionage. With Windows 10 Enterprise edition and specially configured OEM hardware, administrators will be able to completely lock down devices so that they're unable to run untrusted code.
In this configuration, the only apps that will be allowed to run are those signed by a Microsoft-issued code-signing certificate. That includes any app from the Windows Store as well as desktop apps that have been submitted for approval through Microsoft. Enterprises with internal line of business apps can get their own key generator, which will allow those apps to run on their network but won't work outside the network.
For more details on the changes, see this blog post from Microsoft.