Microsoft SmartScreen: Now Windows 10 Edge and Internet Explorer can block zero-day web attacks

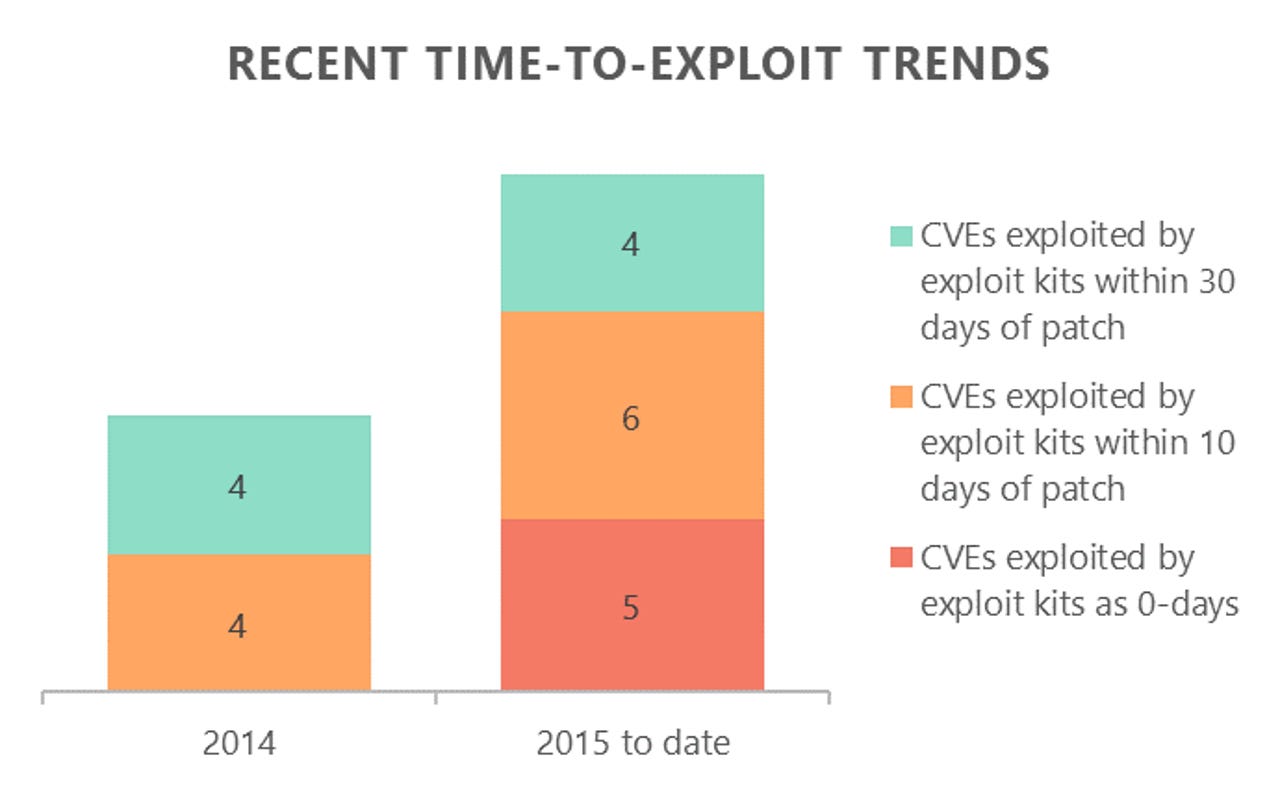
Exploit kits have employed five zero-day flaws this year to attack PC browsers.
Windows 10 Edge might have its fair share of bugs but Microsoft says the browser now stops web attacks against it -- even if Adobe's Flash Player plugin is installed and "even if a patch isn't yet available".
Automated attacks on the browser remain a favourite technique for money-minded hackers, spurring the growth of so-called malvertizing, where they abuse ad networks to deliver malware to mostly Windows PCs. The malicious ads target high-traffic sites such as popular news publishers, torrent sites and news portals, often attempting to install file-encrypting ransomware.
In these instances, just rendering the ad in a browser will lead to malware being installed, typically by exploiting an un-patched instance of Flash Player or flaws in the browser itself -- a method the security industry has dubbed "drive-by download".
Microsoft is promising a game-changer on this front, thanks to new enhancements to its SmartScreen technology, which is integrated with its Windows 10 Edge browser. SmartScreen has been protecting users from phishing and malware downloads since IE7, but until now the Redmond company hasn't had an answer to drive-by downloads.
Microsoft announced on Wednesday that both Edge and Internet Explorer 11 are now equipped with drive-by download protection, which comes as a result of its "cross-company data intelligence". In practice that means it's sourcing data from its browsers, Bing search, its free Windows Defender anti-malware program, and EMET or Enhanced Mitigation Experience Toolkit, which enterprise can employ to block exploits against flaws in Microsoft products in the absence of a patch.
"This cross-company data intelligence effort is unique since it brings together information not just about the browsing experience or web infrastructure, but also about behavioral telemetry from across the Windows operating system. This can help us to detect potential attacks in progress and detect emerging threats," Microsoft's Edge team said.
As Microsoft highlights, for-hire exploit kits such as the notorious Angler are at the root of large-scale web attacks. The kits contain numerous attacks and use publicly available information about software bugs to scan PCs for the presence of one and then try to exploit it. Sometimes, the exploit kits are integrated with highly-prized flaws unknown to a vendor, called zero-day flaws.
Exploit kits have employed five zero-days this year, according to Microsoft's data, while six flaws have been attacked within 10 days of a patch's release. Microsoft claims that with the new drive-by protection, zero day attacks "may be prevented before a user is infected, even if a patch isn't yet available".
That could be a game changer, given that in those instances, users are often advised to disable or uninstall the affected product until a patch is available. Alternatively, as happened this July after zero-day Flash Player flaw was discovered, Mozilla blocked all versions of Adobe's product.
Time will tell if SmartScreen lives up to its promise, but anecdotally, Microsoft says that last December, during SmartScreen's development, its security products detected a zero-day Flash flaw being used in a malicious ad campaign.
"SmartScreen intelligence systems were detecting this attack even before it was identified as a new 0-day exploit," Microsoft said.
According to Microsoft, the new SmartScreen protection aims to block drive-by attacks before any web content is parsed or rendered. SmartScreen generates a small cache file that is periodically updated to ensure calls are made to the service if there's a high chance a page is hosting malicious content.
In that instance, Edge and IE 11 will generate a red splash page, warning that "this website has been reported as unsafe" and then report the visit back to Microsoft. Users can still bypass the warning but Microsoft advises against doing so.
The new SmartScreen also has a better way of handling malicious frames, often used in malicious ads. Instead of blocking the page the ad is hosted on, SmartScreen will isolate the malicious ad.
"In the past, unsafe frames on a page would result in a full-page warning, even if the webpage hosting the content was safe. Now, SmartScreen can show you warnings for only the frames that are found to be malicious, letting you continue to interact with the rest of the page," it said.