Microsoft updates Windows Defender to remove Superfish infection

Updated 20-Feb to include comments from Mozilla and Symantec and to add details about third-party antivirus software. Updated 21-Feb with additional details about Norton software.
Several hours after this article was published,Lenovo acknowledged security issues with the preinstalled software on its consumer PCs and released its own removal tool.
The Microsoft Security Response Team can move very quickly.
The tech world exploded Thursday with the revelation that Lenovo had preinstalled an adware program called Superfish Visual Discovery on an unknown number of its consumer PCs, with the extra bonus of a local root certificate that posed a frightful risk to owners of the affected machines.
On Friday, Microsoft released the latest definitions for its Windows Defender software, which is included as a standard feature on all Windows 8.x PCs. The new definitions, which are installed automatically, detect and remove the offending app and the certificate.
To test the effectiveness of the removal process, I installed the Superfish package using a copy provided by a security researcher, who had extracted it from a Lenovo PC. I confirmed that the software added both the Superfish application and the dangerous root certificate.
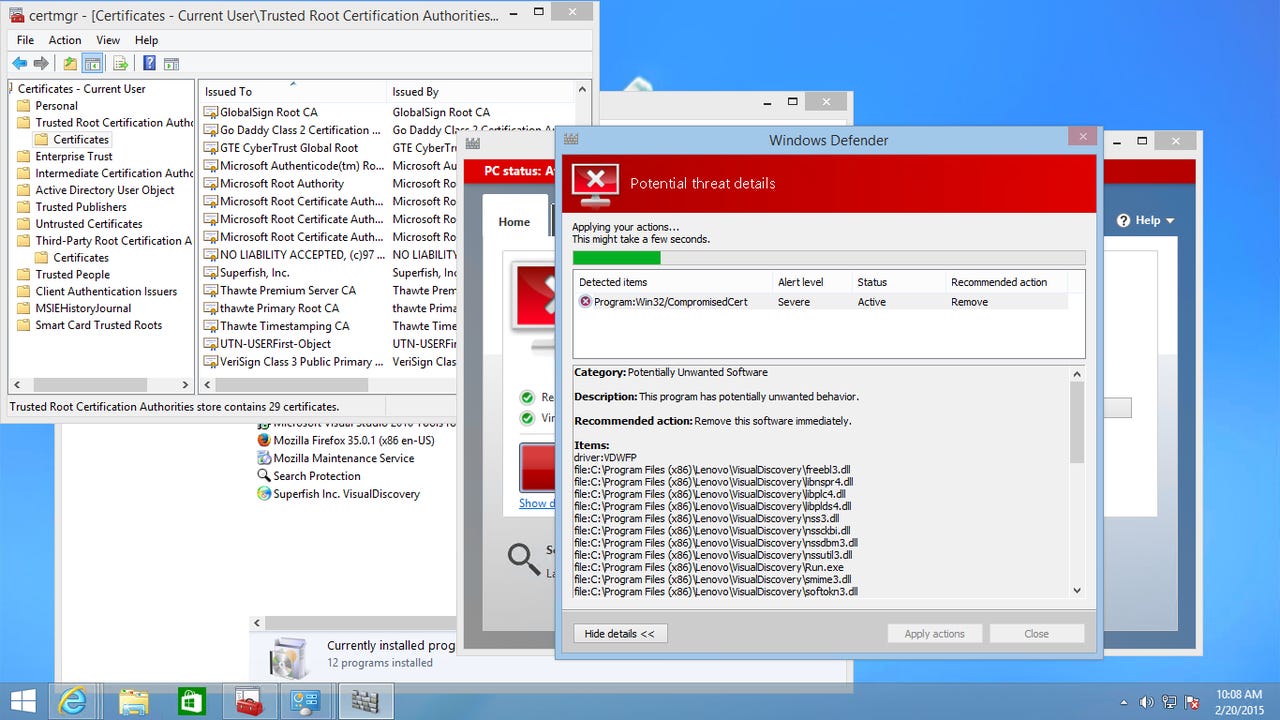
Windows Defender had scanned my virtual PC early this morning, using definitions that had been installed automatically at 3AM, and had detected nothing. After I manually updated to the most recent definitions and ran a quick scan, however, the system detected the Lenovo certificate and recommended its immediate removal.
After OKing the cleanup and restarting, I opened Certificate Manager and confirmed that the offending root certificate was indeed gone.
On systems that don't have active and up-to-date antivirus software, Windows Defender runs automatically. The event logs on my test system show several scans and multiple definition updates every day.
If another antivirus program is running, Windows Defender is disabled. It won't do scheduled scans, nor can you run manual scans. As Peter Bright of Ars Technica notes, this is problematic on Lenovo PCs where the buyers have set up trial antivirus software included as part of the same third-party software load that includes Superfish and its accompanying certificate.
There's no guarantee that other security software makers will detect and remove this dangerous software. I installed a trial version of Symantec's latest Norton Security software, updated it with the most recent definitions, and then performed a quick scan of a system infected with the Lenovo version of the Superfish software. The Norton software didn't trigger any warnings, even though Symantec's Security Response database identifies Superfish as adware (classifying it as low risk).
I then performed a full scan, which also failed to turn up any warnings. Strangely, the Norton log contained detections for both Superfishcert.dll and Visualdiscovery.exe, but both files were listed as "Exonerated."
Via email, Brian Ewell, Threat Intelligence Officer for Symantec Security Response, said he was unable to explain why the Norton software didn't detect these threats:
We have released detections so it's hard to say why this didn't trigger for you without knowing what version of definitions you were running and what version of the Superfish program you had installed.
We're continually updating our detection for this as we encounter new samples and are investigating any additional remediation opportunities.
Update 21-Feb: Overnight, the Norton software downloaded and installed new detection signatures, and when I checked in this morning the Norton software was displaying a dialog box noting that it had detected Superfish.adware as a threat. The recommended action, however, was to exclude the Superfish files. I had to manually change that option to "Fix" in three different places. The Norton software did not detect or offer to remove the potentially dangerous Superfish certificate.
One caveat: Windows Defender doesn't monitor Mozilla Firefox, which maintains its own certificate store. After successfully running the cleanup, I checked the certificate store in Firefox and discovered that the potentially dangerous root certificate was still installed in that browser and would require manual removal. Mozilla's Cryptographic Engineering Manager, Richard Barnes, says via email that the company is "investigating this situation" and will provide further updates when their investigation is complete.
My test system didn't have Google Chrome installed, so I was unable to check whether it requires manual removal of the certificate. Because Chrome uses the Windows certificate store, it's unlikely that this represents a risk, but I've asked Google for confirmation and will update this post with any response
(Note that this check of third-party browsers is necessary because I installed Superfish after Firefox was already installed. On an OEM system, where an alternative browser is installed after the fact, this step might not be necessary. Still, better safe than sorry.)
In recent months, Microsoft has come under fire for slow response to security flaws in Windows. This case is qualitatively different in that the offending code isn't a part of Windows and doesn't require extensive testing. For Windows users who aren't willing or technical able to perform the tricky manual removal process, this is very good news.
The unwelcome and potentially dangerous software was preinstalled on some Lenovo consumer PCs between September and December 2014. If you purchased a Lenovo PC before that date, you're unlikely to be affected. PCs sold in January or February might still be at risk if they were shipped during the last quarter of 2014 and have been on warehouse or store shelves in the interim.