Most malspam contains a malicious URL these days, not file attachments

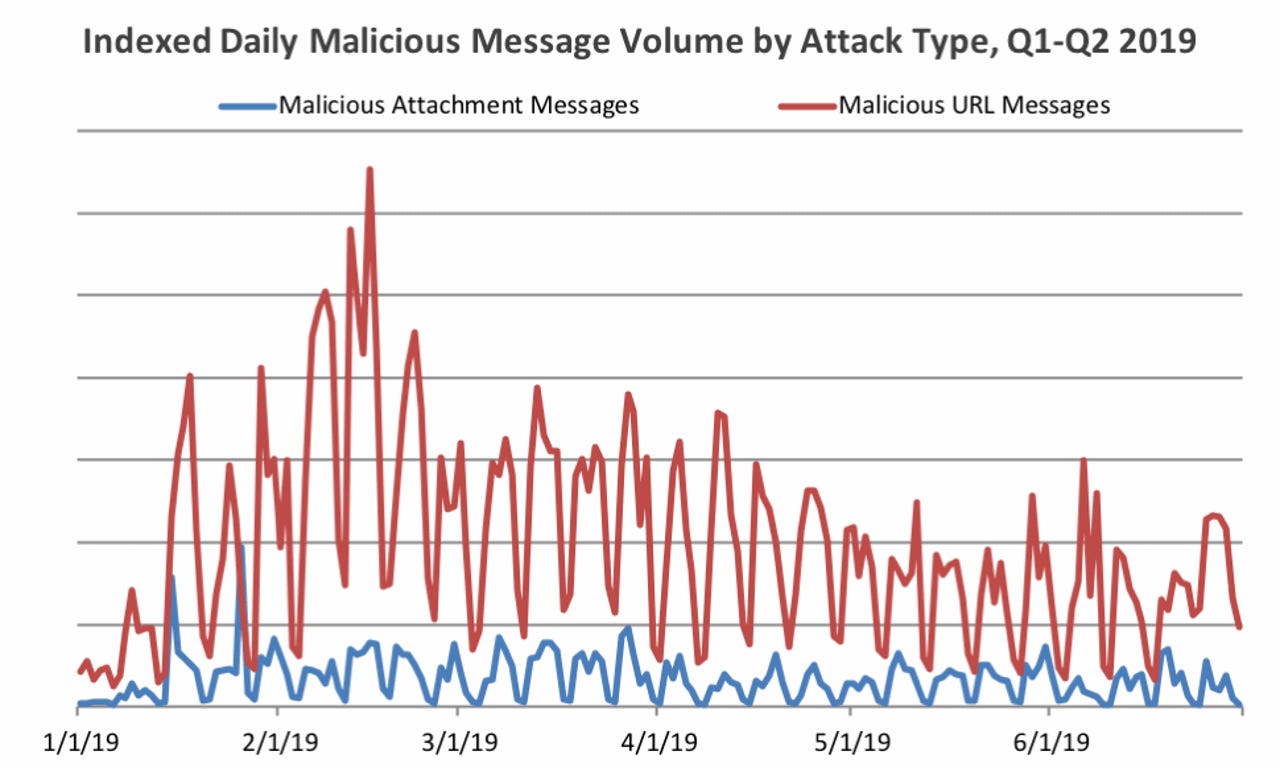
Most malicious email spam (malspam) sent in the first half of the year has contained links to malicious files, rather than file attachments, according to telemetry gathered by cyber-security firm Proofpoint.
More precisely, 85% of all malspam sent in Q2 2019 (April, May, and June) contained a link to a malicious file download, rather than the actual malicious file attached to the email.
The Q2 number continues a Q1 trend, where malicious URLs also dominated as the favorite way of distributing malware via email spam.
But while email spam botnet operators may be criminals, they are in no way stupid. They can be as focused on running an efficient operation like any other Silicon Valley engineer, if not more.
If the majority of malspam content sent out these days leverages malicious links, this means operators are getting higher clickthroughs and infections when compared to the classic technique of attaching files to emails.
"While the reason for the continued dominance of URLs may be due to a range of factors, it is likely that most end users have been conditioned to be suspicious of attachments in unsolicited email," Proofpoint said.
"URLs, on the other hand, are increasingly common in business email as we regularly receive notifications of shared files and collaboration updates via email as organizations move to the cloud," it added.
Proofpoint's findings should have repercussions across the entire cyber-security market. Companies which provide anti-phishing training should be the ones taking notes and adapting courses accordingly; focusing on preparing employees for this recent trend.
And employee training helps.
A previous Proofpoint report found that 99% of all email-based cyberattacks require human interaction, namely that the target open files, click on links, or carry out some other sort of action. With a little training, employees can be taught to recognize and avoid falling victims to these attacks.
Other findings from the Proofpoint Q2 2019 Threat Report, published earlier this month, include:
- 57% of all malspam uses domain spoofing.
- Botnet-based malware was the most popular malware payload sent via malspam campaigns, accounting for 37% of all emails.
- Botnet malware was followed by banking trojans (23%), infostealers (16%), malware loaders (8%), remote access trojans (6%), and backdoor trojans (5%).
- As in recent quarters, ransomware was virtually absent in Q2.
- Ursnif accounted for 80% of all banking trojan payloads sent via email. It was followed by URLZone, The Trick, and Dridex.
- The ranking for infostealer had Pony in front, followed by AZORult, Loki Bot, and Formbook.