New FreakOut botnet targets Linux systems running unpatched software

A newly identified botnet is targeting unpatched applications running on top of Linux systems, Check Point security researchers said in a report today.
First seen in November 2020, the FreakOut botnet has surfaced again in a new series of attacks this month.
Its current targets include TerraMaster data storage units, web applications built on top of the Zend PHP Framework, and websites running the Liferay Portal content management system.
Check Point says the FreakOut operator is mass-scanning the internet for these applications and then utilizing exploits for three vulnerabilities in order to gain control of the underlying Linux system.
All three vulnerabilities (listed below) are fairly recent, which means there's a high chance that FreakOut exploitation attempts are succeeding as many systems could still be lagging behind on their patches.
- CVE-2020-28188 - RCE in TerraMaster management panel (disclosed on December 24, 2020)
- CVE-2021-3007 - deserialization bug in the Zend Framework (disclosed on January 3, 2021)
- CVE-2020-7961 - deserialization bug in the Liferay Portal (disclosed on March 20, 2020)
Once the FreakOut bot gains access to a system, it's immediate step is to download and run a Python script that connects the infected devices to a remote IRC channel where the attacker can send commands and orchestrate a varied list of attacks using the enslaved devices.
According to a Check Point technical report published today, the list of commands that FreakOut bots can run includes the likes of:
- Gathering info on the infected system;
- Creating and sending UDP and TCP packets;
- Executing Telnet brute-force attacks using a list of hardcoded credentials;
- Running a port scan;
- Executing an ARP poisoning attack on the device's local network;
- Opening a reverse shell on the infected host;
- Killing local processes; and more.
Check Point argues that these functions can be combined to perform various operations, like launching DDoS attacks, installing cryptocurrency miners, turning infected bots into a proxy network, or launching attacks on the internal network of an infected device.
However, right now, Check Point says the botnet appears to be in its infancy. Researchers said they were able to reverse engineer the malware and then access the IRC channel through which the operator controlled the entire botnet.
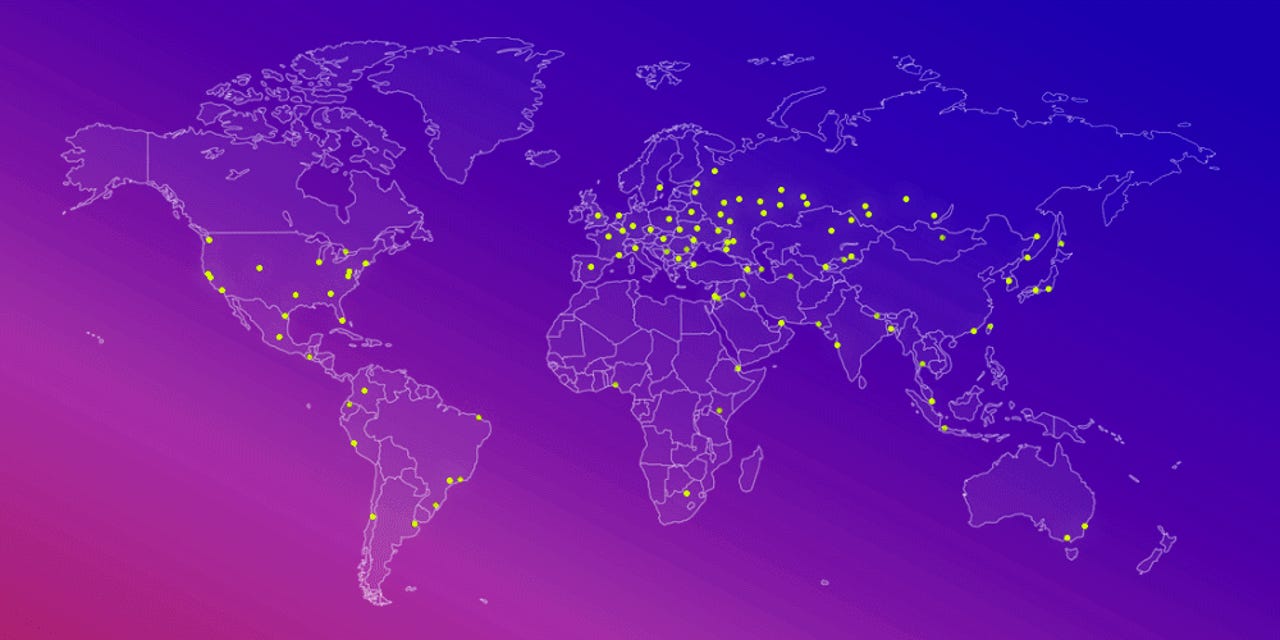
Stats shown in the IRC panel suggest the botnet is only controlling around 180 infected systems, but past figures showed it merely peaked at around 300.
Both are low numbers for a botnet but more than enough to launch very capable DDoS attacks.
Furthermore, Check Point said it also found several clues in the malware's code that allowed it tracked down its creator, a person who goes online by the nickname of Freak.
Some clever sleuthing later, researchers said they were able to link this nickname to an older hacker acronym of Fl0urite, which was the creator of the now-defunct N3Cr0m0rPh, a similar botnet malware strain that was sold on hacking forums and targeted Windows devices.
According to a screenshot of past N3Cr0m0rPh ads, many of the older botnet's features are identical to the ones found in the current FreakOut malware targeting Linux systems.