New iOS exploit discovered being used to spy on China's Uyghur minority

Security firm Volexity said today that it discovered a new iOS exploit that was being used to spy on China's oppressed Uyghur minority.
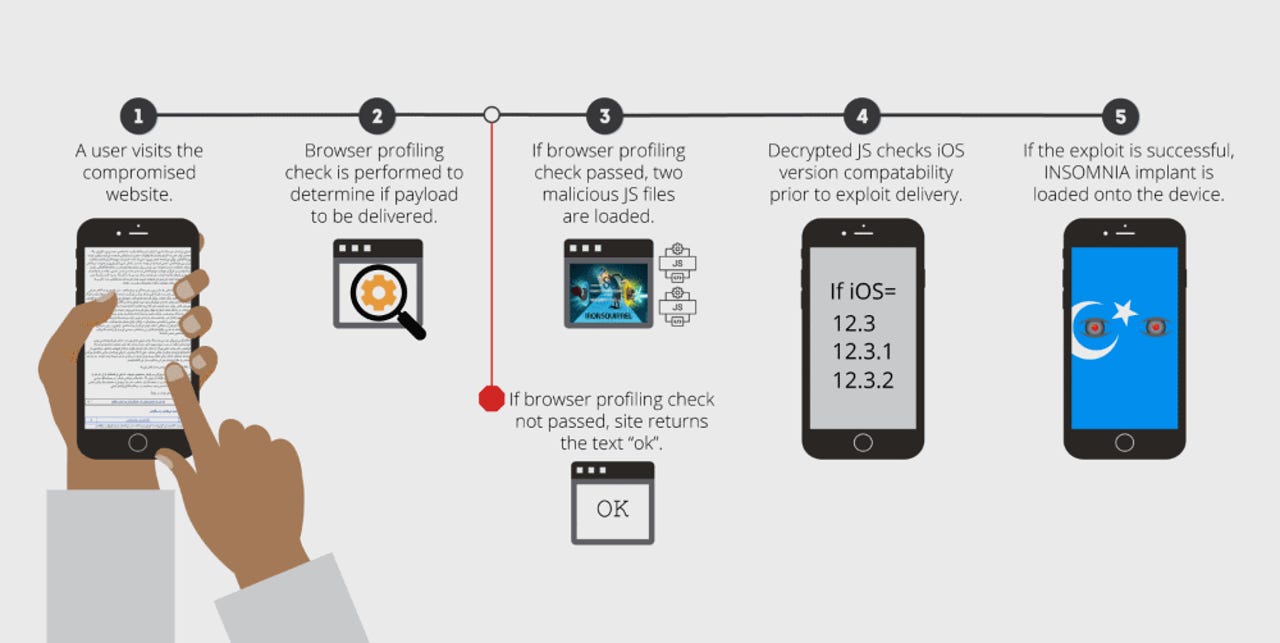
The exploit, which Volexity named Insomnia, works against iOS versions 12.3, 12.3.1, and 12.3.2. Apple patched the iOS vulnerability behind this exploit in July 2019, with the release of iOS version 12.4.
Volexity said the Insomnia exploit was used in the wild between January and March 2020.
The exploit was loaded on the iOS devices of users visiting several Uyghur-themed websites. Once victims accessed the site, the Insomnia exploit was loaded on the device, granting the attacker root access.
Hackers used access to the device to steal plaintext messages from various instant messaging clients, emails, photos, contact lists, and GPS location data.
Insomnia exploit used by Evil Eye group
Volexity said the exploit was deployed by a threat actor the company is tracking under the name of Evil Eye.
The Evil Eye group is believed to be a state-sponsored hacking unit operating at Beijing's behest, and spying on China's Uyghur Muslim minority.
This is the same group that Google and Volexity discovered in August 2019 using 14 iOS exploits to target Uyghurs since at least September 2016. The 14 exploits were also deployed using a similar tactic -- using a "watering hole" technique to plant the exploit on a website and wait users to visit it.
In a new report published today, Volexity says that once Google published its report on the 14 iOS exploits, Evil Eye shut down its infrastructure and stopped using the older exploits.
But according to Volexity, the group came back to life in January 2020 with the new Insomnia exploit, and continued where it left off, targeting the Uyghur minority in a new series of "watering hole" attacks.
Now targeting Signal and ProtonMail as well
Volexity researchers say the new Insomnia exploit also comes with improvements, compared to the 14 iOS exploits the group had used before.
The previous batch of exploits -- used in the attacks between 2016 and 2019 -- could steal GPS coordinates, photos from the iOS Photos app, the address book of the Contacts app, emails from Gmail, and messages from Whatsapp, Telegram, WeChat, iMessage, and Hangouts. [See full Google analysis here]
Per Volexity, the new Insomnia exploit was expanded to also target emails from the ProtonMail app and images transferred via the Signal app.
"The inclusion of Signal and ProtonMail may suggest that the Uyghurs are aware of potential monitoring of their communications and are attempting to use applications with strong security features to avoid this," Volexity said today.
Insomnia works with any WebKit-based browser
The cybersecurity firm says that any iOS users who visited the Insomnia-infested websites were vulnerable to getting hacked.
"Note that exploit can be triggered through any browser on the phone, as they all use WebKit," the research team said. "Volexity was able to confirm successful exploitation of a phone running 12.3.1 via the Apple Safari, Google Chrome, and Microsoft Edge mobile browsers."
Just like the exploits used before, Insomnia still doesn't have a "boot persistence" mechanism included. This means that simply rebooting the phone removes the Insomnia malicious code from the device.
However, the Volexity team also believes that this doesn't necessarily mean that Evil Eye can't get boot persistence if they ever wanted.
"It may be possible the attackers have a method to maintain persistence but only set this up manually after verifying the target," the company said.
Volexity said that while the Insomnia exploit was deployed across several websites, the exploit was found most of the time on the Uyghur Academy website (akademiye[.]org).
Users who visit Uyghur-themed websites and want to make sure they won't get hacked can protect themselves by updating devices to the iOS 12.4 release.