Over 485,000 Ubiquiti devices vulnerable to new attack

Security
Ubiquiti Networks is working on a fix for a newly discovered security issue affecting its devices that attackers have been exploiting since July last year.
The issue impacts over 485,000 devices, according to an internet scan conducted by US cyber-security firm Rapid7.
Also: Japanese government plans to hack into citizens' IoT devices
Mass-exploitation attacks were first spotted last week by Jim Troutman, co-founder of internet exchange point NNENIX (Northern New England Neutral Internet Exchange).
Troutman said threat actors have been using a service running on port 10,001 on Ubiquiti devices to carry out weak DDoS amplification attacks.
Attackers are sending small packets of 56 bytes to port 10,001 on Ubiquiti devices, which are reflecting and relaying the packets to a target's IP address amplified to a size of 206 bytes (amplification factor of 3.67).
The exploitation attempts are in their incipient stages, and attackers are still experimenting with the best way to carry out the attacks. There haven't been any major outages caused by DDoS attacks carried out via this attack vector, industry insiders have told ZDNet.
Attacks happening on port 10,001
In a security alert published by Rapid7, senior security researcher Jon Hart explained that attackers are exploiting a "discovery service" running on port 10,001, which Ubiquiti Networks included in its devices so the company and internet service providers (ISPs) can use it to find Ubiquiti equipment on the internet and in closed networks.
Hart said the amplification factor of this service can go up to 30-35, posing the real danger that attackers could find a way to weaponize this service and carry out DDoS attacks in excess of 1Tbps, which Hart described as "a crippling amount of traffic to all but the most fortified infrastructure."
The Rapid7 researcher said that the only good news at the moment is that this discovery protocol "does not appear to suffer from multi-packet responses," making exploitation extremely hard for the time being, as attackers can only "reflect" small amounts of DDoS traffic.
However, hackers should never be underestimated, a reason why Ubiquiti Networks announced last week that it was preparing a patch, even if in its current form the protocol doesn't seem to be that harmful.
"To our current knowledge, this issue cannot be used to gain control of network devices or to create a DDoS attack," the hardware maker said.
"As a temporary workaround for this issue while it is being investigated and resolved by the development team, network operators can block port 10001 at the network perimeter," Ubiquiti Networks added.
Also as a side effect, as an attacker is trying to use this service for DDoS attacks, remote access to the device via its SSH service is also cut out.
While larger exploitation attempts have been spotted recently, Rapid7's Hart said that the first attacks trying to exploit the Ubiquiti discovery service had been spotted last July, when some Ubiquiti device owners reported problems accessing SSH services on their devices.
Most affected devices are high-grade WISP equipment
Hart says that this discovery port isn't specific to one Ubiquiti device, and is found on a wide variety of the vendor's equipment, such as NanoStation (172,000 devices), AirGrid (131,000 devices), LiteBeam (43,000 devices), PowerBeam (40,000), and others.
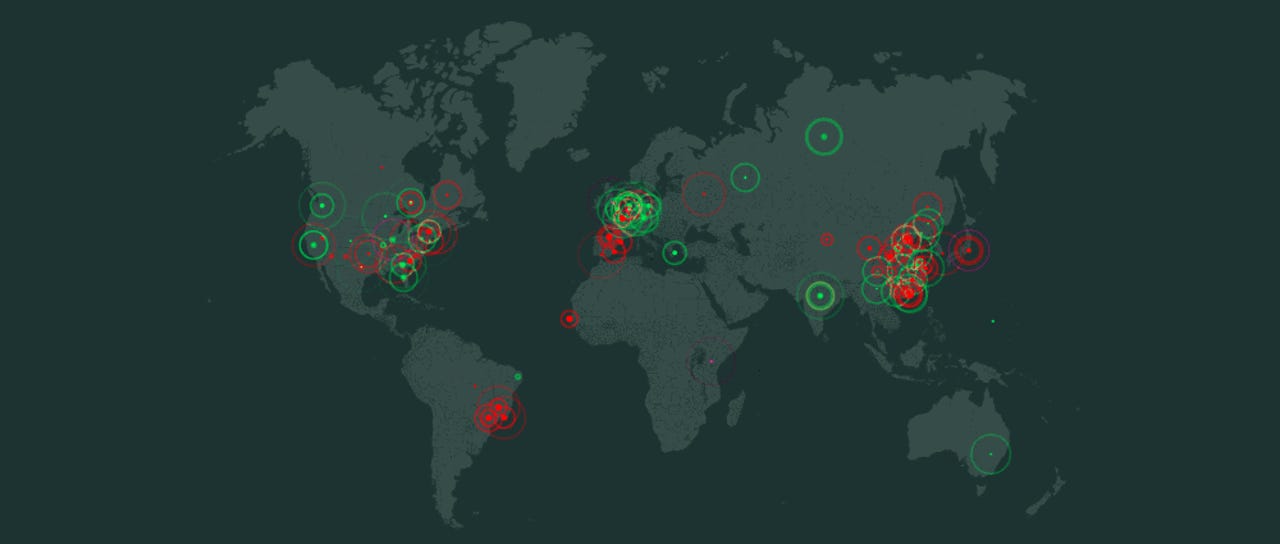
Most of the devices are WiFi antennas, bridges, and access points --equipment typically found on the network of wireless ISPs (WISPs). Hart says that while devices exposing port 10,001 are located all over the world, a large number of them are amassed in Brazil, the US, Spain, and Poland.
Of the 485,000 devices exposing this port, 17,000 have also been defaced already, according to Hart, featuring non-standard hostnames. This means that these devices are also most likely running outdated firmware.
Ubiquiti devices have been defaced on a regular basis in the past years. For example, in January 2018, a hacker changed the hostnames of over 36,000 Ubiquiti devices to names such as "HACKED FTP server," "HACKED-ROUTER-HELP-SOS-WAS-MFWORM-INFECTED," or "HACKED-ROUTER-HELP-SOS-HAD-DEFAULT-PASSWORD."
Must read
- 5 ways to enforce company security (TechRepublic)
- Data breaches can sucker-punch you. Prepare to fight back (CNET)
In 2016, Ubiquiti devices were defaced again after hackers accessed devices, changed hostnames, but also access credentials --username "mother" and password "[expletive]er".
Device owners and ISP employees worried about attacks against their devices can follow this advice from Ubiquiti on how to disable the discovery service on their devices.
When IoT/home automation devices explode
More security coverage:
- Hackers are going after Cisco RV320/RV325 routers using a new exploit
- DOJ moves to take down Joanap botnet operated by North Korean state hackers
- Police are now targeting former WebStresser DDoS-for-hire users
- IoT botnet used in YouTube ad fraud scheme
- The DDoS that wasn't: a key takeaway for web domain security
- California governor signs country's first IoT security law CNET
- 5 steps to a new IoT support strategy TechRepublic