OwnStar: Unlock and track any GM OnStar connected car for $100

A security researcher has revealed OwnStar, a gadget which is capable of tracking and remotely unlocking OnStar-enabled General Motor vehicles.
On Thursday, security researcher Samy Kamkar unveiled the OwnStar, a gadget which turns OnStar's promise of keeping drivers "safe, connected and ready for the road" on its head. OnStar is a connected car system you can find on modern vehicle models provided by General Motors and is designed to increase the connectivity of your car by linking the vehicle to your mobile device.
OnStar offers various services including crash reports, remote unlocking, ignition blocks in the case of theft and navigation services. While such packages have appealed to consumers, just like with any other computer system or software, the risk of vulnerabilities which can place systems at risk exists. In OnStar's case, this has now become a reality.
Featured
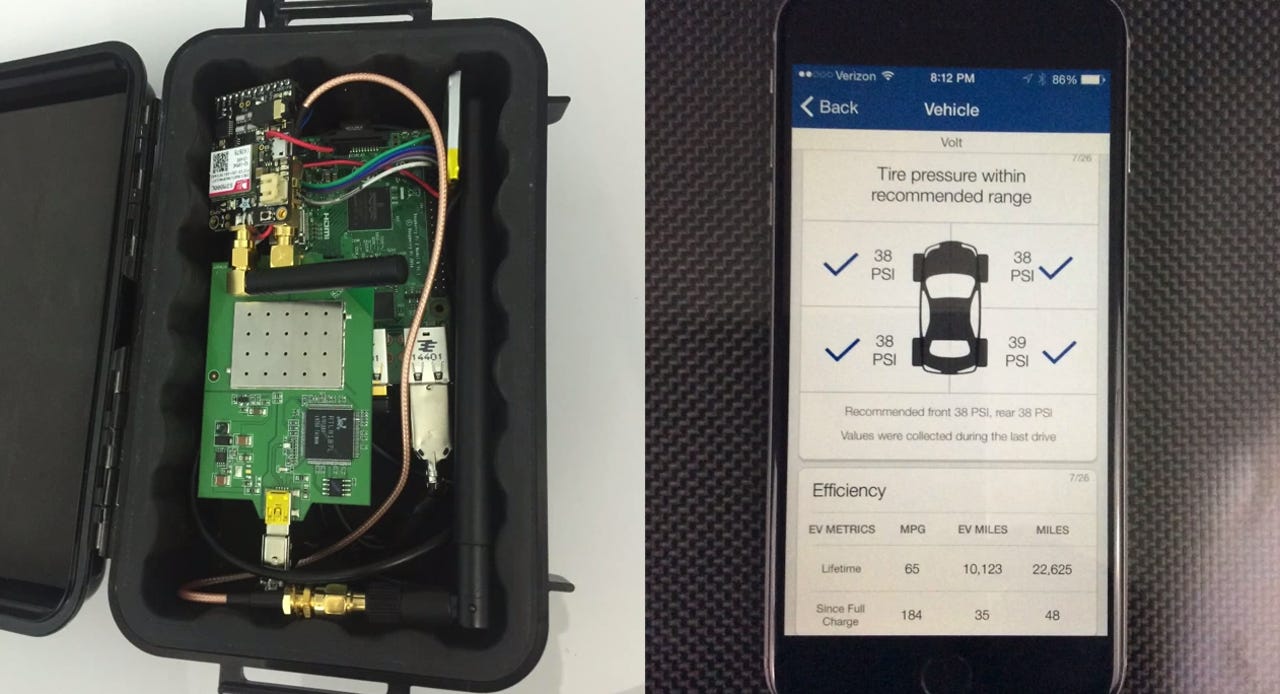
Kamkar's Raspberry Pi-based device, which cost less than $100 to make, has been described as an invention which can "locate, unlock and remote start any vehicle with OnStar RemoteLink after intercepting communication between the RemoteLink mobile app and OnStar servers," in other words, perform a man-in-the-middle (MITM) attack to steal data across a communication channel and potentially plant code suitable for exploiting software.
Details are sketchy, but the security expert plans discuss his research at length at the annual DefCon security conference in Las Vegas, Nevada, as well as in a future video. For now, however, Kamkar is content to demonstrate OwnStar in action via an uploaded YouTube video:
Within the video, Kamkar says that once a user opens the OnStar application on their smartphone, the OwnStar gadget is able to intercept this communication and send specially-crafted packets of data to the victim's device.
These packets of malicious code are able to then use a privilege escalation flaw to acquire high user credentials, before notifying the OwnStar attacker remotely that access has been granted "indefinitely" to the hacker. The OwnStar device is also able to access information including a car's make and model.
By using OwnStar, Kamkar is able to lock and unlock a vehicle -- targeted for demonstration purposes -- through the smartphone-linked key fob functionality, as well as sound the horn or start its engine, according to Wired. The security researcher has promised to reveal the details of this exploit at a later date, most likely once the vulnerability has been patched.
"Fortunately, the issue lies within the mobile software, and is not a problem with the vehicles themselves," Kamkar says. "GM and OnStar have so far been receptive to me and have been working quickly on a resolution to protect consumers."
In the interim, the security researcher recommends that OnStar uses refrain from using the remote link app until an update and patch has been provided.
In a statement, GM said:
"Cybersecurity is a global issue facing virtually every industry today, and a lot of work continues to been done at GM in this space.
Our customers' safety and security is paramount and we are taking a multi-faceted approach to secure in-vehicle and connected vehicle systems, monitor and detect cybersecurity threats, and design vehicle systems that can be updated with enhanced security as these potential threats arise."
Top 5 security practices in staying safe online: From the experts
Read on: Top picks
- How to access Wi-Fi anonymously from miles away
- Hammertoss: Russian hackers target the cloud, Twitter, GitHub in malware spread
- Getting physical: A $10 device to clone RFID access keys on the go
- Amazon dreams of drones-only airspace
- Army exoskeletons train soldiers to shoot
- Hornet Tor alternative for high-speed anonymous browsing revealed
In pictures: