Pro-Palestine DNS hack under investigation

The domain registrar and host supporting sites disrupted by cyberattacks in the past week, Network Solutions, is investing a pro-Palestinian group which has claimed responsibility.
Owned by Web.com, Network Solutions manages domain names and hosted for companies including LeaseWeb, anti-virus software maker AVG, pornography site RedTube, Whatsapp and web statistics firm Alexa. In the past week, all of the above have been hit by DNS hijacks that have redirected website users to other domains promoting a pro-Palestinian message.
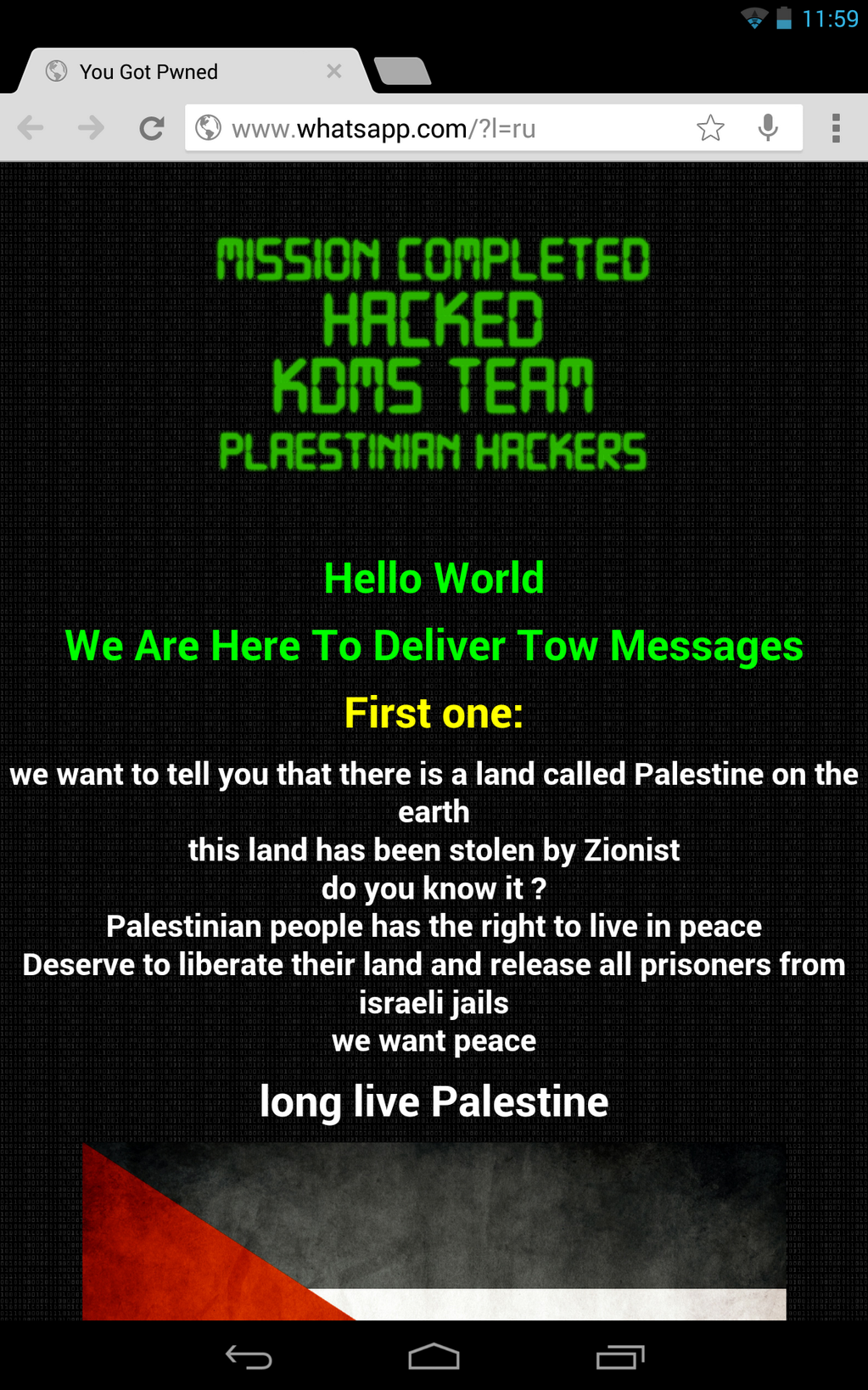
As reported by CIO, pro-Palestinian group KDMS Team claimed responsibility for the attacks on social media platform Twitter.
The defaced messages have included assertions that Palestine has been stolen, prisoners held in Israel should be released, and peace needs to be secured by the two regions.
AVG confirmed on Tuesday that "a select number of online properties were defaced as a result of our domain name system (DNS) registrar being compromised." At the time of writing, Whatsapp and Avira are still offline.
According to CIO, while Avira's blog was still accessible, the company said it was aware that DNS (Domain Name System) records were pointed to other domains, otherwise known as DNS hijacking. The pro-Palestinian group were able to send a fake password reset request that was honored by the provider, and then change the entries to point to KDMS Team-controlled domains.
Featured
Earlier this week, LeaseWeb's domain was redirected after the group obtained an administrator password from the domain's registrar. The company said in a blog post that the leaseweb.com DNS was changed at the registrar, and for a short period of time some visitors were redirected to another, non-LeaseWeb IP address.
Network Solutions said it was aware of the attack, writing on the company's blog:
"Network Solutions experienced a distributed denial of service (DDoS) attack on its servers that affected our customers. The Network Solutions technology team quickly identified the issue and implemented measures to mitigate the attack.
We apologize to our customers who were impacted."
John Herbkersman, Web.com's senior director for public communications, told the publication that while "cybercrime today is rampant, we just continue to try to do our best to bring in the best people and bring in the best equipment."
The KDMS Team have posted a number of screenshots of the attacks on Twitter, and while some Twitter users have questioned the group's political protest methods, wrote back:
Another well-known example of DNS hijacking is that of Australian IT services company Melbourne IT. In August, The New York Times and Twitter revealed that their DNS entries had been modified, with the Syrian Electronic Army taking credit for the attack. Valid credentials were used to log in to a reseller account responsible for the affected domain names.