Security researcher discloses four IBM zero-days after company refused to patch

A security researcher has published today details about four zero-day vulnerabilities impacting an IBM security product after the company refused to patch bugs following a private bug disclosure attempt.
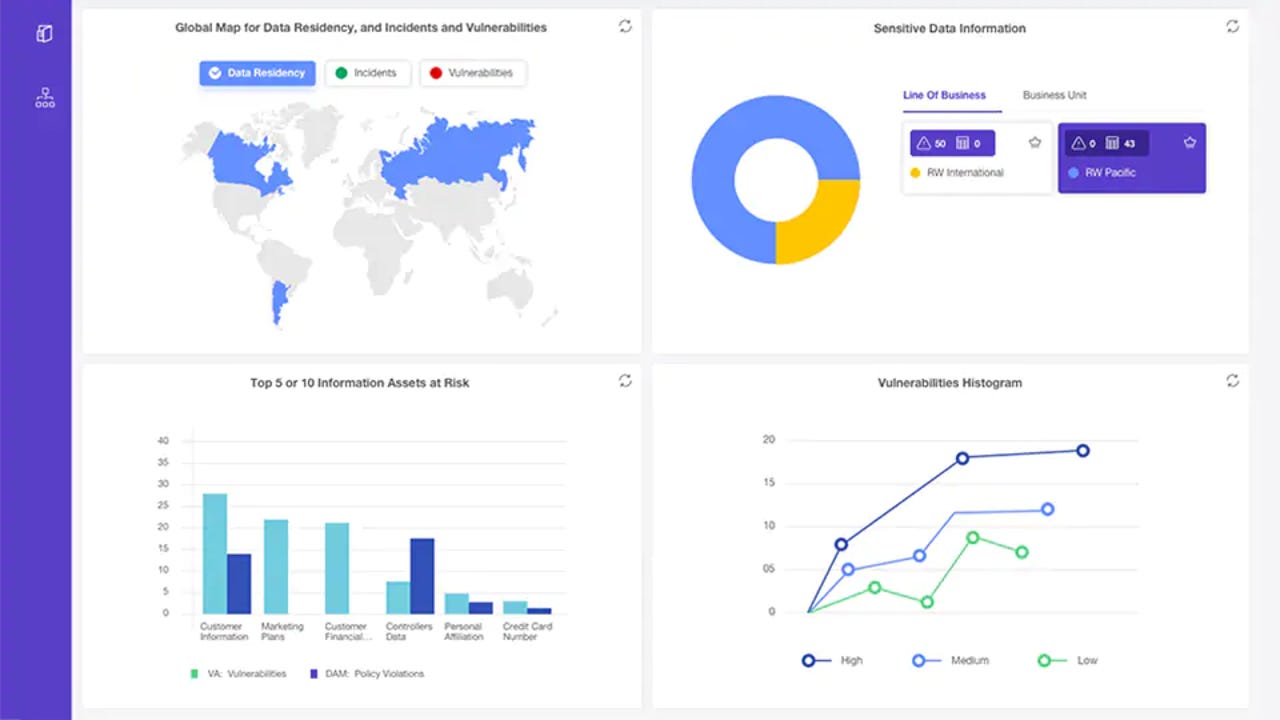
The bugs impact the IBM Data Risk Manager (IDRM), an enterprise security tool that aggregates feeds from vulnerability scanning tools and other risk management tools to let admins investigate security issues.
"IDRM is an enterprise security product that handles very sensitive information," said Pedro Ribeiro, Director of Research at Agile Information Security, and the one who discovered the four bugs.
"A compromise of such [a] product might lead to a full scale company compromise, as the tool has credentials to access other security tools, not to mention it contains information about critical vulnerabilities that affect the company," he added.
IBM refused to patch the reported issues
Ribeiro said he found four bugs in IDRM and worked with the CERT/CC team to report the issues to IBM through its official bug vulnerability disclosure program.
The security researcher said that despite of the severity of four bugs he reported, IBM refused to accept the bug disclosure answering with what appears to be a nonsensical response:
we have assessed this report and closed as being out of scope for our vulnerability disclosure program since this product is only for "enhanced" support paid for by our customers. This is outlined in our policy https://hackerone.com/ibm. To be eligible to participate in this program, you must not be under contract to perform security testing for IBM Corporation, or an IBM subsidiary, or IBM client within 6 months prior to submitting a report.
The researcher said that to this day, he has yet to understand what the response actually meant, and still has questions, such as:
- "Why did IBM refuse to accept a FREE detailed vulnerability report?
- "What does their answer mean? Are the only accepting vulnerability reports from customers?
- "Or is the product out of support? If so, why is still being offered for sale to new customers?
- "How can they be so irreponsible while selling an enterprise security product?"
"This is an unbelievable response by IBM, a multi billion dollar company that is selling security enterprise products and security consultancy to huge corporations worldwide," Ribeiro said.
Details published today on GitHub
Seeing that IBM was not interested in patching the bugs, the researcher has published today details on GitHub about the four issues, so that companies that use the product can put mitigations in place to prevent any attacks.
The four issues, as reported, are:
- A bypass of the IDRM authentication mechanism
- A command injection point in one of the IDRM APIs that lets attacks run their own commands on the app
- A hardcoded username and password combo of a3user/idrm
- A vulnerability in the IDRM API that can allow remote hackers to download files from the IDRM appliance
"This advisory describes the four vulnerabilities and the steps necessary to chain the first three to achieve unauthenticated remote code execution as root," Ribeiro said.
"In addition, two Metasploit modules that bypass authentication and exploit the remote code execution and arbitrary file download are being released to the public."
All four bugs are remotely exploitable, Ribeiro added. If the IDRM appliance is exposed online, attacks can be carried out over the internet. Normally these systems aren't accessible on the internet, which reduces the impact to organizations running IDRM.
However, even if the IDRM is not exposed online, an attacker who has access to a workstation on a company's internal network can chain the four bugs together to take over the IDRM appliance, extract credentials for other systems, and move laterally to other systems on the company's network.
IBM calls it a "process error"
In an email to ZDNet today, IBM appears to regret how the incident unfolded and that a patch is now currently in the works.
"A process error resulted in an improper response to the researcher who reported this situation to IBM," a spokesperson told ZDNet.
"We have been working on mitigation steps and they will be discussed in a security advisory to be issued."
We'll update this article with a link to the security advisory containing mitigation and patch information once it goes live.
Updated at 11:40am ET with statement and new information from IBM.