Thousands of 3D printers may be leaking private product designs online

Nearly 3,800 3D printers have been left exposed online without a password, two security researchers from the SANS ISC organization have warned last week.
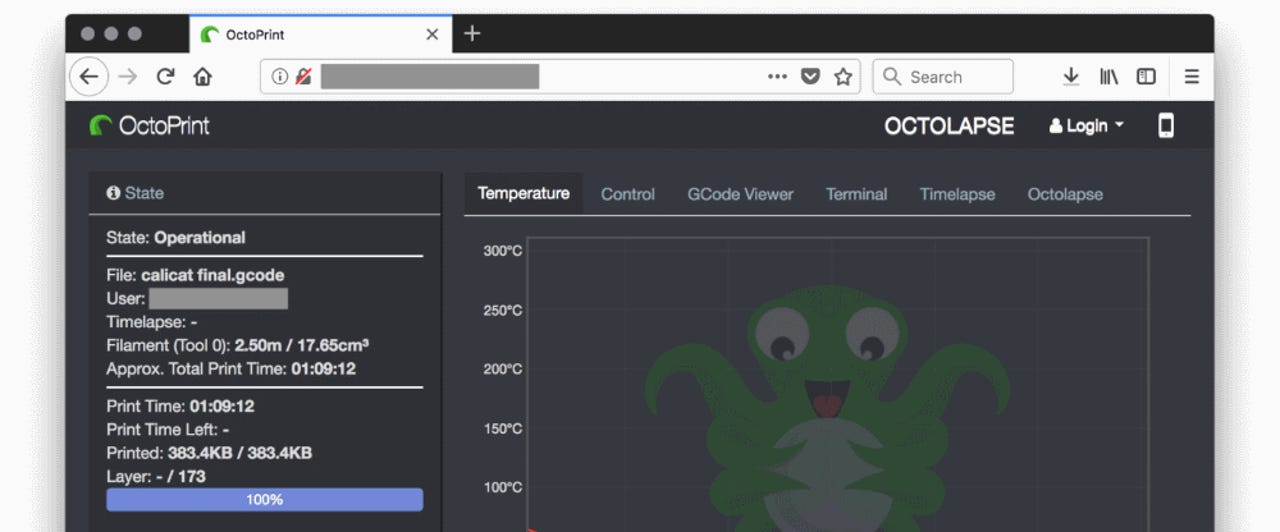
The common link between all printers is an open-source project named OctoPrint. This project is a free web interface that some 3D printer manufacturers have embedded with their devices to allow users remote access to printing stations.
The OctoPrint interface provides a wide array of features, such as the ability to download and upload 3D models (as .gcode files), but also the ability to view webcam feeds, if the 3D printer supports such a feature.
But SANS ISC researchers Richard Porter and Xavier Mertens say that thousands of 3D printers sporting an OctoPrint interface have been carelessly exposed online, allowing anyone to modify a printer's settings.
The two argue that such a decision from the devices' owners is complete folly. Anyone could access these printers and steal 3D models uploaded on the OctoPrint interface.
These 3D models aren't encrypted, and attackers could very easily use 3D rendering software to reconstruct the original components, potentially revealing private or proprietary information about unreleased products.
See also: 1990s technology exposes 32,000 smart homes, businesses to exploit
But corporate theft is just one of the possible scenarios. Sabotage is another. Porter and Mertens also argue that a malicious competitor could download a rival's 3D model, make a small modification, and re-upload the model on the exposed OctoPrint interface, leaving the victim to print out hundreds or thousands of incorrect or faulty products.
Furthermore, accessing a 3D printer's webcam can also reveal additional details regarding the manufacturing process, details that aren't normally revealed by downloading a 3D model file, and which can also reveal various other manufacturing secrets.
The two researchers aren't fearmongering. Academic research published in 2016 predicted and highlighted the dangers that come from the proliferation of Internet-connected 3D printers among today's manufacturing sector. Porter and Mertens' findings merely confirm what academics have predicted years before.
See also: New Hakai IoT botnet takes aim at D-Link, Huawei, and Realtek routers
But the biggest issue is that searching for exposed printers is relatively easy thanks to tools like Shodan, a search engine for Internet-connected devices.
Finding 3D printers with an exposed OctoPrint interface requires a carefully crafted search query, but results will include details like IP addresses and network names, which gives an attacker a general idea of the printer's location. Nearly 3,800 3D printers with OctaPrint interfaces are available online today.
Viewing the actual OctoPrint interface only requires accessing the IP address on port 5000, the default OctoPrint web interface port.
This is really not that complicated. A cursory search by this reporter quickly identified two 3D printers belonging to two US manufacturers, highlighting the danger to which some companies and sysadmins are exposing themselves.
CNET: IoT attacks are getting worse -- and no one's listening
"Things like a printer - regardless whether it prints in 2D or 3D - do not belong on the public internet," Gina Häußge, creator and maintainer of the OctoPrint project, told ZDNet in an interview.
"Sadly a lot of users actively ignore such recommendations," she added. "We have to educate users, so they don't take unnecessary risks for the sake of convenience."
For its part, OctoPrint published a blog post this week with advice for 3D printer owners on how they could secure their devices against unauthorized access, but still allow remote access to authorized personnel.
But the blog post also points out that intellectual property theft is also not the worse thing that could happen. For example, attackers could reflash the device's firmware and do damage to the 3D printer itself. If this results in a fire, as it happened before with 3D printers, this may also lead to the destruction of entire factories if fires get out of control.
But things don't need to reach this stage if device owners act and secure any exposed dashboards before it's too late.
The same advice goes for any device, not just 3D printers. There's nothing good that can come from leaving any admin panel for any type of device exposed online.