United Airlines offers air miles as bug bounty reward

As cybercrime rises, security experts are in high demand and short supply. During the software development lifecycle, the more eyes on a program the better -- in order to detect and iron out bugs before they are released into the commercial or consumer sector.
If a cyberattacker is able to find a flaw in programs or websites, they are able either to sell the information on the black market or exploit it for their own ends. If they choose to use system security flaws as an entry point into corporate networks, they may be able to steal valuable data and damage business systems -- which in turn can be costly in both financial terms and reputation for victim companies.
As a result, offering rewards for bug disclosure is becoming a popular method for third-party security professionals to contribute to the protection of a corporate network. However, now that cybersecurity is a hot topic and hiring is at a premium, researchers may expect more than just credit in return for their time.
Companies such as Google, Microsoft and Facebook offer monetary rewards for bug disclosure. United Airlines, in keeping with the company's services, has chosen to offer air miles.
See also: Bug bounties: 'Buy what you want'
"We believe that this program will further bolster our security and allow us to continue to provide excellent service," United says. "If you think you have discovered a potential bug that affects our websites, apps and/or online portals, please let us know. If the submission meets our requirements, we'll gladly reward you for your time and effort."
If a researcher discovers bugs in the system which affect the "confidentiality, integrity and/or availability of customer or company information," through customer-facing websites and third-party programs used by United, they may be eligible for reward. Low-severity rated vulnerabilities, such as cross-site scripting, cross-site request forgery and third-party problems which affect United are worth 50,000 air miles.
Featured
However, medium-severity problems, such as authentication bypass, brute-force attacks, timing attacks and security problems which could lead to personally identifiable information disclosure are worth far more, clocking in at 250,000 miles per vulnerability.
Finally, if developers want to earn enough for a first-class flight or two, high-severity vulnerabilities related to remote code execution are worth a maximum of 1,000,000 air miles.
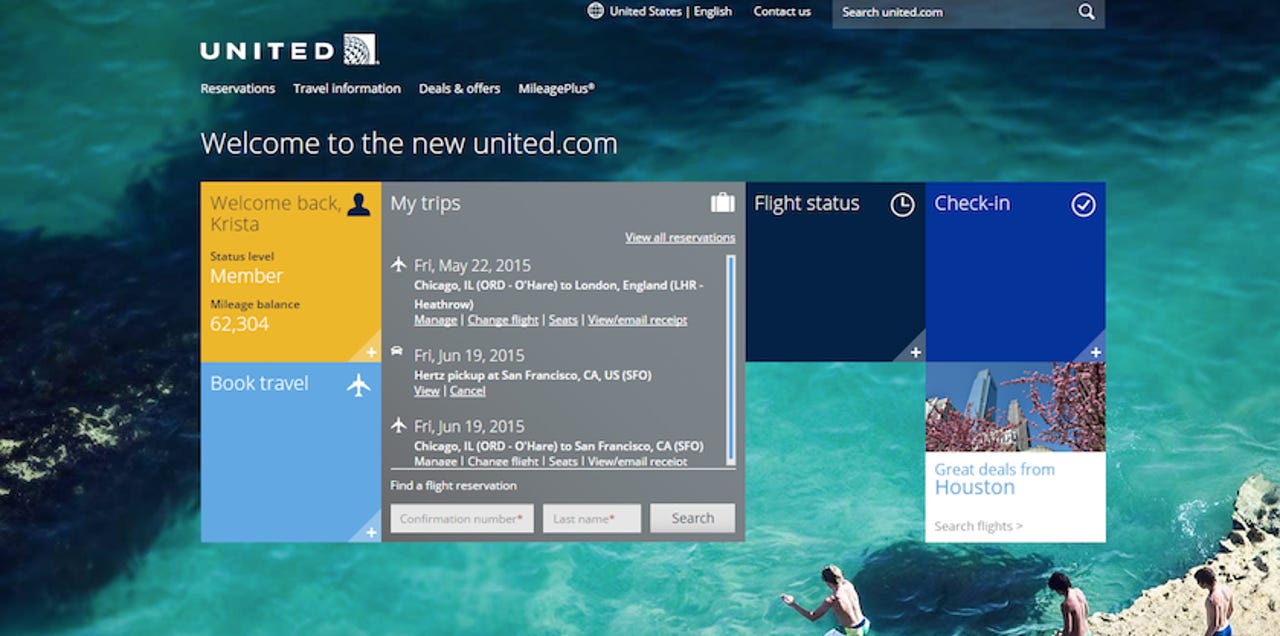
Security researchers must be MileagePlus members in order to submit a vulnerability and potentially collect their rewards. In addition, bugs which only affect legacy systems or unsupported browsers, plugins and operating systems are not eligible; onboard Wi-Fi, entertainment systems and avionics are also out-of-bounds. Vulnerabilities in internal websites used by United employees are also not eligible for rewards.
Interested researchers need to watch their step, however. The airline says brute-force attacks, code injection on live systems, DDoS attacks, testing on MileagePlus accounts that are not your own and testing on in-flight systems will result in disqualification and possible criminal investigation.