Want ransomware-proof Windows? It won't work against Windows 10 S, claims Microsoft

Ransomware is on the rise again, but Windows 10 has you covered, according to Microsoft.
Microsoft boasts that "no known ransomware works against" Windows 10 S, its locked-down and hardened operating system announced in May.
The company made the bold claim in announcing the release of a white paper that details the Windows 10 Creators Update's next-generation protections against ransomware, which also offers an updated snapshot of "ransomware encounters" it detects on Windows machines worldwide.
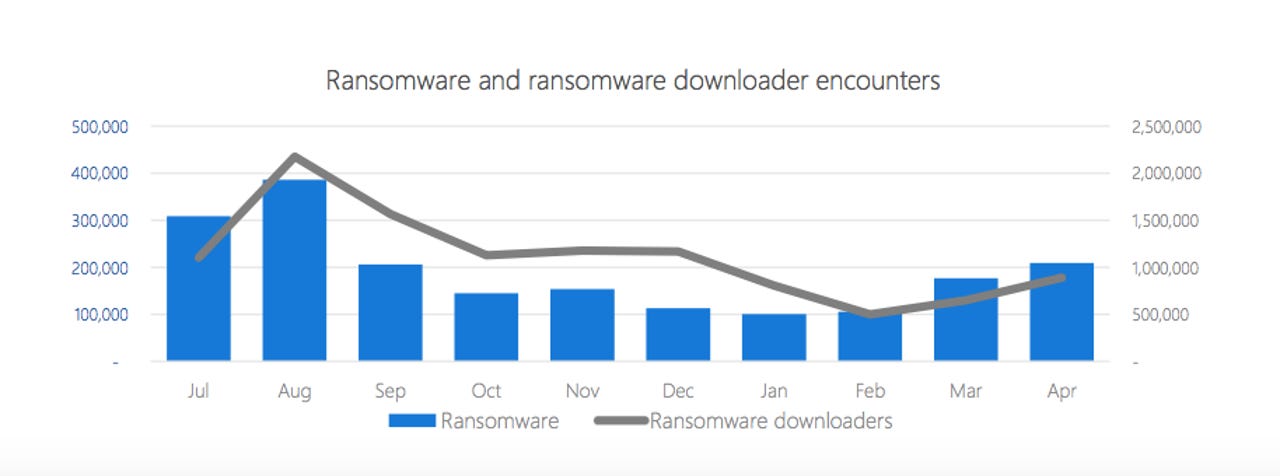
Throughout 2016 ransomware encounters were steadily declining from a peak in August, but they started climbing again in February 2017 and doubled in number by April.
It hasn't released figures for May, when the WannaCry ransomware attack infected several hundred thousand Windows 7 PCs and Windows 2008 Server machines in a matter of hours.
Microsoft also highlights that "no Windows 10 customers were known to be compromised by the recent WannaCrypt global cyberattack".
Time will tell whether ransomware attackers figure out a way to infect Microsoft's Windows 10 S or whether they consider it worth the effort, given easier and more prevalent targets like Windows 7.
As it is, there are no machines running Windows 10 S in the wild yet. The Windows 10 S Surface Laptop is currently in pre-order and third-party hardware has yet to be announced.
Windows 10 S is undoubtedly more secure because of its iPhone-like walled-garden security model, which restricts installs to verified and sandboxed apps from the Windows Store, cutting off malware threats from the web.
Some have criticized the locked-down concept, but Windows 10 S is for a specific market. Unlike Windows RT, it will run on the same hardware as Windows 10, so it is possible to upgrade to Windows 10 Pro.
It removes the risk posed by some older Win32 apps, and offers a unified update mechanism for all applications it's allowed to run. It also features many of the enterprise security features of Windows 10 Pro to help IT departments manage fleets.
Microsoft's Windows 10 Creators Update white paper notes the sizable decline in drive-by downloads or exploit kits to infect machines with ransomware. Email continues to remain popular, while WannaCry and other ransomware families, such as Spora, are exploring the network to spread infections.
Microsoft breaks down Windows 10 defenses into three categories, including protections off the machine, as well as pre-breach and post-breach on machine defenses.
Off-machine security include features such as Office 365's URL detonation service and Edge browser's reputation-based download blocker.
Pre-breach on-machine defenses include Windows Defender, Device Guard, and the Antimalware Scan Interface. Its enterprise-focused post-breach tools include the Windows Defender AV behavioral engine, and Windows Defender ATP, which offer security operations a range of tools to identify, block and isolate malware before it becomes a major outbreak.
Windows 10's improved security has been central to Microsoft's efforts to convince enterprises and consumers to upgrade from Windows 7. The WannaCry outbreak and ransomware in general offer it the perfect threat to illustrate the benefits of the upgrade.
More on Windows 10 S and ransomware
- Microsoft launches Windows 10 S, its Store-centric version of Windows 10
- Acer, HP launch $299 Windows 10 S laptops
- 'Safe and predictable' Windows 10 S won't run Linux, says Microsoft
- Is Windows 10 S for you? The good, the bad, and the target users
- Leaked NSA hacking exploit used in WannaCry ransomware is now powering Trojan malware
- Blue screen of death saved Windows XP from WannaCry ransomware, say security researchers
- Windows ransomware: WannaCrypt shows why NSA shouldn't stockpile exploits, says Microsoft