Windows security: Cryptocurrency miner malware is enslaving PCs with EternalBlue

Trend Micro says Coinminer's use of fileless WMI scripts and EternalBlue makes its threat to Windows machines "extremely stealthy and persistent".
Criminals are infecting Windows machines with fileless malware that runs in memory, and puts the hijacked PCs to work on mining cryptocurrency.
Security
Two features in particular make this malware, known as Coinminer, "extremely stealthy and persistent", according to malware researchers at Trend Micro.
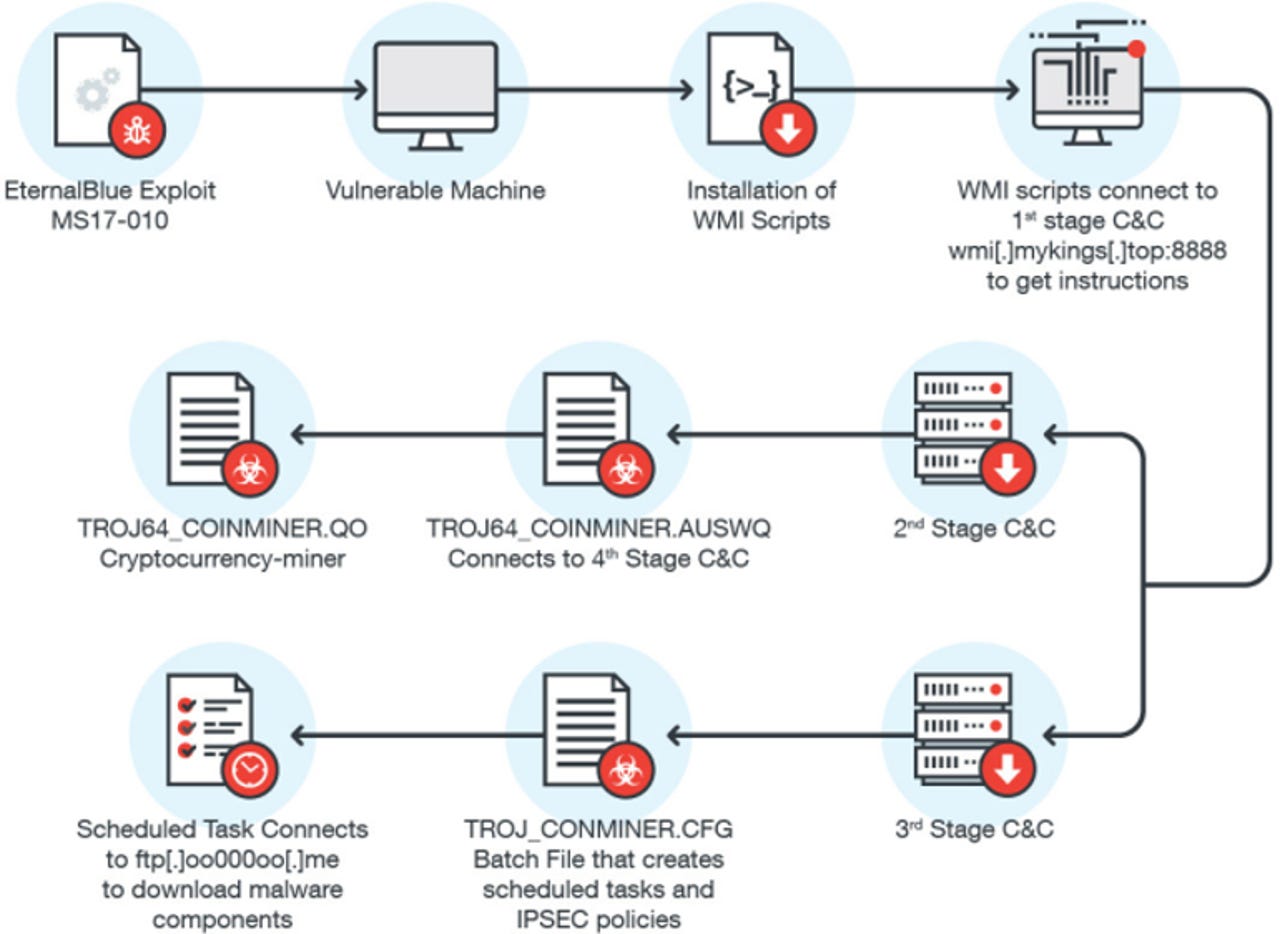
To infect Windows machine, it's using the so-called EternalBlue vulnerability employed by WannaCry and NotPetya as a spreading mechanism. Microsoft released a patch for the flaw in March but a spate of infections in Asia, mostly in Japan, suggest some systems have not been updated.
On machines vulnerable to this bug, the malware runs a backdoor that installs several Windows Management Instrumentation (WMI) scripts that run in memory, which makes them more difficult to detect.
IT admins can use WMI to run scripts that automate administrative tasks on remote computers and acquire management data from these computers and installed Windows applications.
However, in this case the cryptocurrency mining malware uses WMI for more nefarious purposes, including connecting to the attacker's command-and-control domains to download the mining software and malware.
WMI malware isn't new and was used in the infamous Stuxnet malware. FireEye has also found an advanced hacker group APT29 using WMI capabilities to create persistent and stealthy backdoors by automatically triggering a backdoor when a system starts up.
Malwarebytes identified WMI techniques being used to hijack Chrome and Firefox to redirect users to an attack site.
According to Trend Micro, the mining malware operation includes a timer that automatically triggers the malicious WMI script every three hours.
Admins should disable the SMBv1 file-sharing protocol to prevent attacks using Eternal Blue, an exploit for SMBv1 thought to be created by the NSA and leaked in April by the Shadow Brokers.
Even before the leak of EternalBlue and WannaCry's adoption of it, Microsoft was urging customers to stop using the 30-year-old protocol.
Trend Micro also points to a Microsoft tool that can trace WMI activity and recommends restricting WMI on an as-needs basis, as well as disabling WMI on machines that don't need access to it.
Related coverage
Hackers are making their malware more powerful by copying WannaCry and Petya ransomware tricks
The group behind Trickbot is attempting to give its Trojan malware the self-spreading worm-like capabilities that have made recent ransomware attacks go global.
Leaked NSA hacking exploit used in WannaCry ransomware is now powering Trojan malware
EternalBlue Windows security flaw is being leveraged to make Nitol and Gh0st RAT cyberespionage tools more effective, warn researchers.
Read more on malware
- Now criminals turn to PowerPoint files to spread malware
- This Android banking malware steals data by exploiting smartphone accessibility services
- Microsoft PowerPoint exploit used to bypass antivirus and spread malware
- New Trojan malware campaign sends users to fake banking site that looks just like the real thing
- Fileless malware: An undetectable threat (TechRepublic)
- Fake anti-virus filled with malware are flooding app stores (CNET)