Privacy Icons: A graphical approach to online privacy

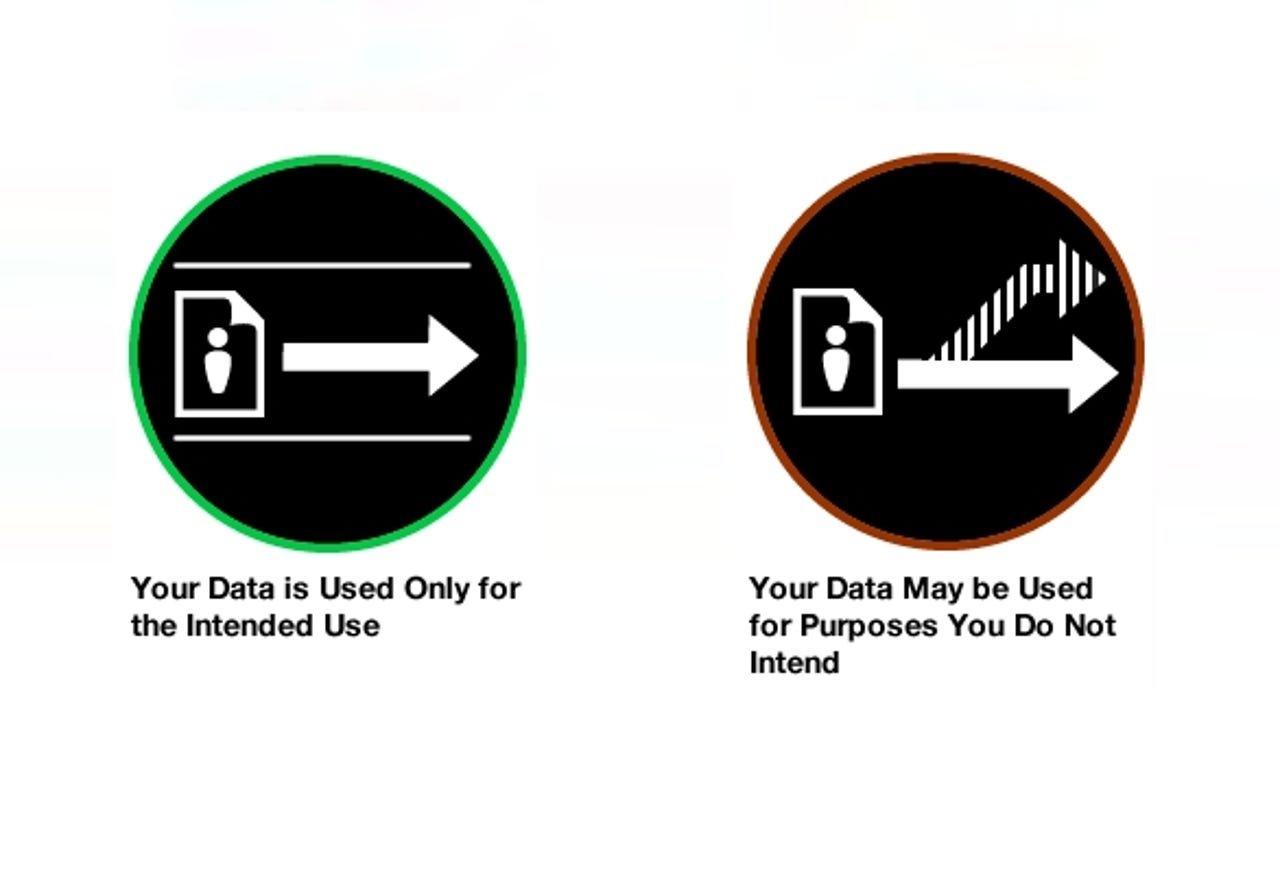
Left: This means that data is only collected and used to carry out the interaction you are engaged in with the website. The website is only using your data in ways that are functionally necessary to carry out the relationship as users intend.
Right: This means that your data is collected and used in ways that go beyond what is necessary for the interaction, like selling on to spammers and junk mailers.
Source: Aza Raskin's blog
--
To read more about Privacy Icons, head on over to the ZDNet iGeneration blog.
Left: The site that is collecting data about you is not trading or selling it. It will only share your data with other organizations in order to carry out the intended transaction.
Right: This means that a website is collecting data about you and selling or trading it with another organization, government, or person.
Source: Aza Raskin's blog
--
To read more about Privacy Icons, head on over to the ZDNet iGeneration blog.
Left: Besides the information exposed via on-page advertisement, the site does not share the data it collects about you with advertisers.
Right: This means that a site either shares the data it has about you with marketing or advertising companies or allows those companies to collect info about you while on its site.
Source: Aza Raskin's blog
--
To read more about Privacy Icons, head on over to the ZDNet iGeneration blog.
Both: Your data is deleted before 1, 3, 6, or 18 months from the date of transmission have elapsed, respectively. Alternatively the data is never deleted.
Source: Aza Raskin's blog
--
To read more about Privacy Icons, head on over to the ZDNet iGeneration blog.
Left: This means that when an organization gets a phone call, letter, or other legally insufficient request for your data, they don’t comply because the law requires the government to take additional steps before getting your data.
Right: These organizations might provide your data to a government that asks for it without following the legally required process.
Source: Aza Raskin's blog
--
To read more about Privacy Icons, head on over to the ZDNet iGeneration blog.