Account details for 4 million Quidd users shared on hacking forum

Quidd, an online marketplace for trading stickers, cards, toys, and other collectibles, appears to have suffered a data breach in 2019, and the details of around four million users are now being shared for free on underground hacking forums.
The data, of which ZDNet has obtained samples from three different sources, contains Quidd usernames, email addresses, and hashed account passwords.
A hacker known as ProTag believed to be behind the breach
In the cybercrime landscape, there are different groups and entities, each with different roles. There are hackers, the ones who carry out the actual security breaches, and there are data traders, individuals who engage in selling and re-selling the hacked data.
Two different sources have told ZDNet that a hacker known as ProTag was the one who took credit for the breach and first put the Quidd data for sale.
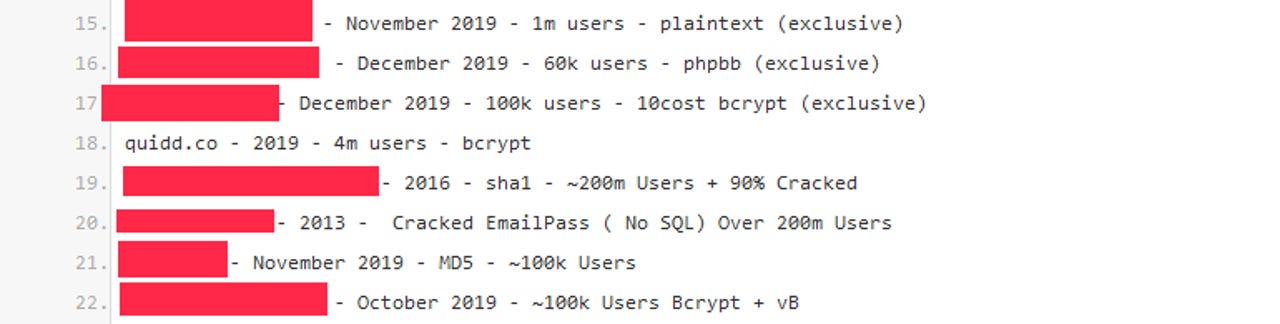
In addition, ZDNet has also learned from a data trader that the Quidd information has been trading privately among high-level groups for months, with ads for the Quidd info being posted on hacking forums and Pastebin since at least October and December 2019, respectively.
But while the data has traded privately in exclusive rings for months, the Quidd user info has now leaked into the public domain.
This happened last month after a data trader posted a copy of the Quidd data on a publicly accessible hacker forum.
Ever since then, the data has been shared and reshared among other members of the hacking community, constantly re-uploaded on multiple forums.
Quidd has not disclosed any recent security incident, and it is unclear if the company is aware of the breach. ZDNet contacted the company for comment and will update the article with any statement the company wants to make.
ZDNet has also obtained copies of the leaked data and reached out to some users to confirm that their details were correct.
Risk Based Security, who first reported on the Quidd breach on Friday, also said that "after initial testing, the data appears to be valid."
The only positive in the leaked data is that the passwords were not in plaintext format, but were secured with the bcrypt hashing algorithm.
Reversing bcrypt-protected passwords into their plaintext format is considered incredibly difficult and a time and resource-consuming operation.
Ironically, the use of the bcrypt algorithm is also very likely the reason why the Quidd data has leaked on public hacking forums in the first place.
"It's bcrypt, so it hasn't been in high demand really," a data trader told ZDNet today (quote edited for clarity).
The trader is referring to the fact that spam, malware, and online fraud groups are normally interested in hacked data that contains cleartext passwords, since it's easier to take over those accounts and carry out their respective spam, malware, and fraud campaigns.
Unfortunately, some hackers have now begun working on cracking the Quidd passwords. One individual is currently selling access to more than 135,000 cracked Quidd passwords, while Risk-Based Security says it's tracking another individual claiming to provide access to more than one million cracked Quidd accounts.
Quidd users are advised to change account passwords as soon as possible.