Amazon Silk browser ignored SSL searches, failing to protect your privacy

Amazon's Silk internet browser contained a serious bug which not only ignored SSL security standards in Google searches but prevented redirection to the secure version of the search engine.
The Google Chrome-based Silk browser, loaded with Amazon Kindle tablets, was set up without Secure Sockets Layer (SSL) technology -- which encrypts communication between servers and web browsers -- and also prevented automatic redirections to Google's SSL version of the tech giant's search engine.
This security problem left user connections unencrypted and potentially open to man-in-the-middle (MitM) attacks and snooping.
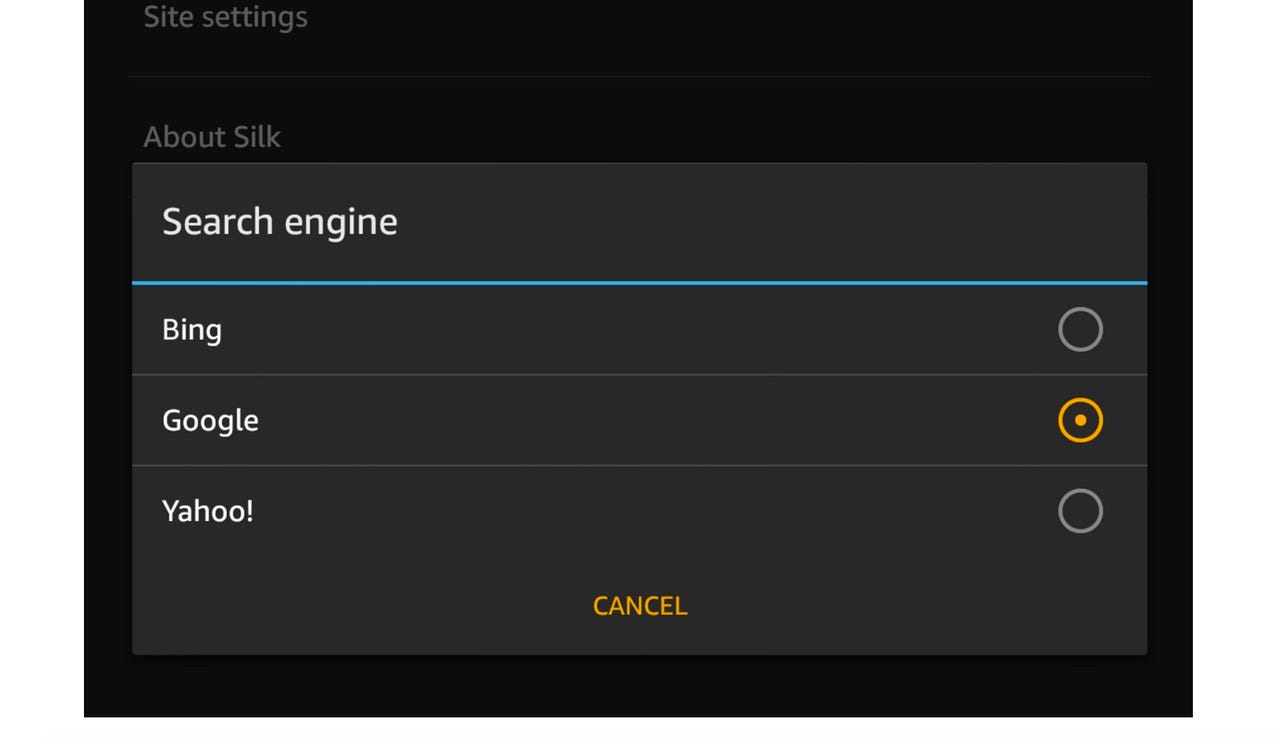
On Monday, Nightwatch Security revealed its findings in a public security disclosure. The company's security team said the browser, which allows users to choose between Google, Bing, and Yahoo for search results, does not connect using SSL if Google is selected.
"All searches via the browser's omnibox are done without HTTPS resulting in ability of malicious third parties to monitor user's search engine traffic," the team says.
"Furthermore, going to 'http://www.google.com' which normally would redirect to the SSL version, stayed in HTTP mode and prevented redirection. All other Google international domains (like google.ru, google.fr, etc) automatically redirected to the SSL versions."
Nightwatch security verified the problem existed on v.49.3.1, and the problem was fixed in the Silk browser version 50.
Amazon and Google were notified of the security issue on May 1, 2016. A day later, the Nightwatch security team received a generic response from Amazon, and a fix was issued and verified in July before public disclosure. A CVE assignment for the security flaw is pending.
Users of Amazon's Kindle range permit automatic updates to the newest version of the Silk browser.