Android Gmail app security hole lets you pretend to be anyone online

A bug which allows you to pose as anyone when sending an email through the Gmail application has been deemed a non-issue despite the risk of exploit via phishing campaigns.
The bug is found within the standard Gmail application and needs only a few simple steps to implement. As reported by Motherboard, the issue was discovered by security researcher Yan Zhu and disclosed publicly last week.
In order to spoof your email address and masquerade as someone else when sending an email, you need only change your display name in account settings, which hides your legitimate email address.
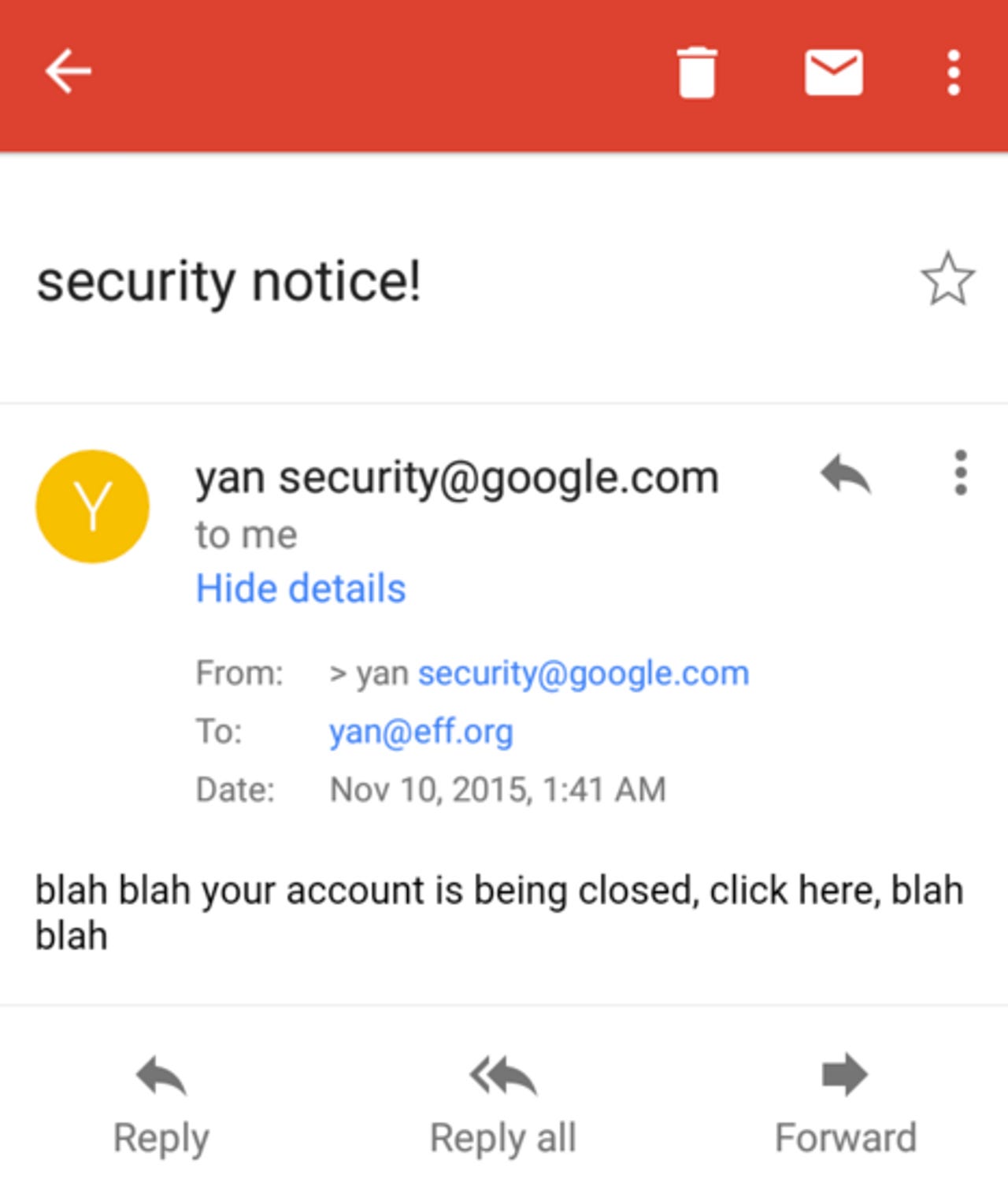
Zhu demonstrated the problem through the email screenshot shown below. The independent researcher did nothing beyond changing her display name to yan ""security@google.com" -- including the important extra quotation mark, which triggers a parsing bug. The bug then forces the real email address to become invisible in the Gmail app, allowing Zhu to conceal herself as a member of Google's security team.
Security
If an attacker is able to spoof their email address in this way and appear as something legitimate -- whether it be security@yourbank.com, account@google.com or your grocery store, a well-known delivery agent or friends and family, mass-phishing campaigns and spear-phishing may become more successful.
These techniques are used by cyberattackers to make fraudulent emails appear legitimate and entice victims to visit malicious websites which may download malware payloads or lure people into entering their account details, paving the way for account takeovers, data theft and empty bank accounts.
Your spam box is full to the brim of fake messages from sources pretending to be your bank, financial institutions and well-known companies such as eBay and PayPal because it is not difficult to spoof email addresses. However, the problem with this bug is that the flaw allows attackers to circumvent the usual spam filters which detect and stop these messages reaching your main inbox.
This is where things get somewhat peculiar. Despite this security concern, according to Zhu, the tech giant does not consider the bug a security vulnerability. On Twitter, Zhu posted:
The bug was filed privately but may not be fixed if this is Google's stance on the issue. However, a number of folks interested in security have joked about Zhu's next step -- such as emailing the Google Security team with notifications like "payroll suspension notice," or, as Phred says, send the email from "Sergey or Larry and tell them it's a high priority bug that they need to fix immediately. Problem solved."
Last week, the Mountain View, CA-based firm said Gmail will be updated as part of a ramped-up security effort. While the email service already uses HTTPS to encrypt connections and implements a protocol called STARTTLS to prevent snooping, Gmail will warn users when they are about to receive emails from unencrypted sources "in the coming months."
Top tips to stay safe on public Wi-Fi networks
Read on: Top picks