Android Trojan infiltrates mobile firmware, Trend Micro apps

[Update 21.3, 8.26 GMT: Clarification added and comment from Gmobi.)
An Android Trojan which displays unwanted ads and installs nuisance software on mobile devices has been discovered in the firmware of smartphones and in popular Android applications, according to researchers.
The adware, dubbed Gmobi, has infected the firmware of at least 40 low-end smartphone models and is in a number of applications provided by well-known companies, researchers from Dr. Web said on Thursday.
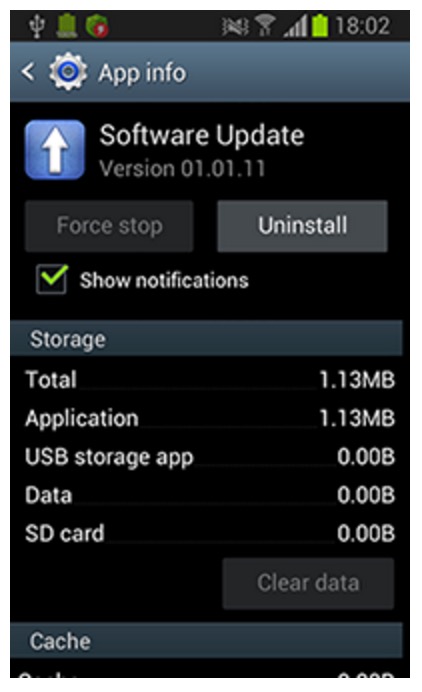
Gmobi is packaged as a tailored program in software development kits (SDKs) for Google's Android platform. The team says that while SDKs are used by developers to expand the functionality of Android apps, the Trojan module is able to "remotely update the operating system, collect information, display notifications (including advertising ones), and make mobile payments."
On the surface, this sounds simply like the functionality of many legitimate apps we download every day.
However, Gmobi also performs typical functions linked to adware -- such as displaying unwanted and potentially malicious ads and software without user consent -- and is able to entrench itself in device firmware.
As a result, the Dr. Web team detected the SDKs installed on at least 40 low-end smartphones as malicious, as well as a number of apps hosted on the Google Play store, and labeled these functions as malicious.
According to Dr. Web, the Trojan's main purpose is to collect sensitive information from user devices and send them to the command and control (C&C) server controlled by an operator. The information gathered includes user emails, roaming availability, GPS coordinates, device information and the presence of apps on the smartphone or tablet.
This data is gathered and sent every time the device is connected to the Web or the home screen is active. The C&C then responds with an encrypted JavaScript Object Notification (JSON) which contains commands such as display an ad or notification, launch an installed application, and create advertising shortcuts on the home screen. In addition, the Trojan may also be ordered to automatically download and install APK files.
If a device has the Gmobi module installed, it may display ads in the device's status bar, dialogs and on top of both running applications and the GUI of the operating system -- as well as open up nuisance advertising pages in browsers or through an infected Google Play application.
When these display, users click on ads and software is downloaded (unwittingly) by the user, profit is generated. However, with ad-supported free mobile applications, you often expect to deal with nuisance ads in return for software.
Security
The researchers say that apps including Trend Micro Dr.Safety, Dr.Booster, and Asus WebStorage have been affected by the malware.
The security team informed the companies of the issues, and now TrendMicro Dr.Safety and TrendMicro Dr.Booster, at least, have disabled intrusive functions. Asus is considering how best to tackle the problem.
Raimund Genes, CTO of Trend Micro, told ZDNet the module was included in the freemium versions of the apps, but was never part of the paid mobile security alternatives. The adware was integrated as part of an initiative in Asia, in which Trend Micro "offered free products to receive information in return for upsell opportunities." Genes commented:
"As Dr. Web categorizes this function as potential unwanted software or malware, we discussed this business model with the vendor.
While they did not hide the function of the integrated module, and we clearly stated on Google Play which data will be accessed by our apps, we concur with Dr. Web that this data collection could be perceived as offensive or malicious activity. As a result, we have made the decision to remove the module in question until we reach a resolution with our partner on more transparent methods for freemium offers."
The company behind the "adware," General Mobi, disputes Dr. Web's claims, telling ZDNet that the module is not a threat to users, and rather acts as a means for vendors to provide users with quick firmware over-the-air (FOTA) updates. In addition, when a contract is signed between a vendor and GMobi, there are strict clauses to prevent misuse.
The firm said in a statement to ZDNet over email:
"In the context of proliferation of malwares in the connected world where millions of new users are coming online probably for the first time, GMobi FOTA allows OEMs to provide timely SW updates to protect the devices and reduce expensive customer service handling cost.
All SW releases happen with close coordination with respective OEMs. All customer communications happen with OEM consent and approval.
We are fully aware of the potential misuse and grey area operation by many of our competitors, GMobi has never ever crossed the boundary of ethical business operations and beyond the contractual obligation with OEMs and end users.
We have extended our FOTA service to app partners like Trend Micro and various other partners in the form of SDK where the purpose is again very well defined [...] and falls under the End User License Agreement ( EULA) scope between app publisher and the end user.
Overall, it is suffice to say that there has been not a single incidence of misuse of the power of access and user data by GMobi."
Must-have high-end smartphones for business users
Read on: Top picks
- How to increase your Bitcoin mining profit by 30 percent with less effort
- SMS Android malware roots and hijacks your device - unless you are Russian
- Bug bounties: Which companies offer researchers cash?
- Shodan: The IoT search engine privacy messenger
- What happens when you leak stolen bank data to the Dark Web?