Apple iOS flaw Ins0mnia hides malicious apps which run forever

A security flaw which permitted malicious applications to run in the background of iOS devices for an unlimited amount of time has been patched by Apple.
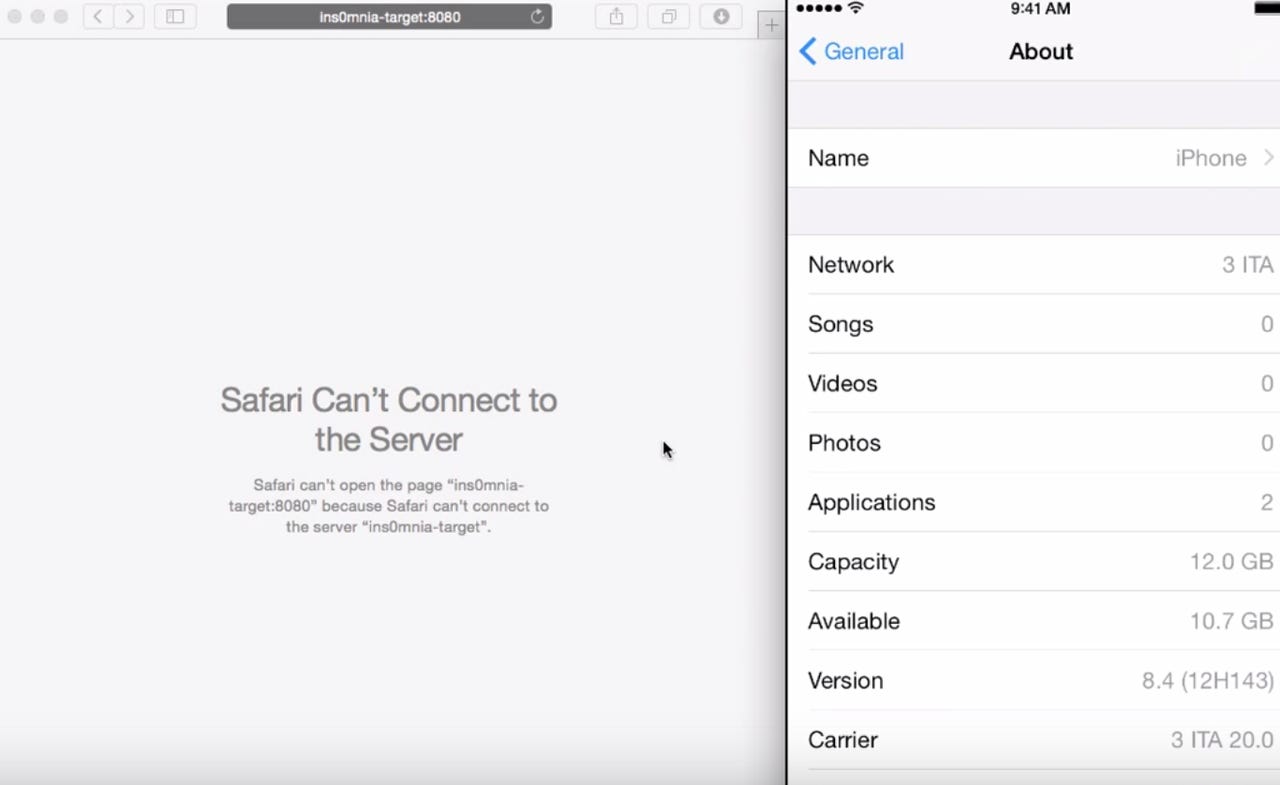
The vulnerability, dubbed Ins0mnia by FireEye researchers, allowed iOS applications to continue to run in the background of an Apple device even when the process was terminated by the user and no longer visible in the task switcher -- bypassing Apple background restrictions and timeout protocols.
If an application is downloaded to an iOS system, the application has a set time imposed by Apple before the app is suspended and operations stopped. FireEye researchers say in general, this time limit can be counted in minutes. This can prevent an app from eavesdropping in the background -- for example, a music app which asks permission for GPS information can be legitimate, but few users would want this program continually monitoring GPS locations.
Therefore, the control over such application processes is meant to protect the abuse of permissions granted by a user.
Featured
If the owner of the iPad or iPhone uses the iOS task switcher, they can view a list of recently opened apps. When an app is closed down, the software will be pushed into the background -- and is subject to the same time limit restrictions -- or the user can choose to completely close the app by removing it from the list.
However, the Ins0mnia vulnerability allows applications to bypass these Apple-imposed controls. The exploit fools the device into believing the system is being debugged, and therefore the system suspends any timeout features relating to the malicious app.
The malicious app could then run in the background and steal user data for an unlimited amount of time, and could also be used to hamper device performance and battery life.
According to FireEye:
"To fool iOS, a malicious application could leverage ptrace, and utilize the ptrace code that handled the PT_TRACE_ME request to set the flag P_LTRACED and gracefully return 0. By setting the P_LTRACED flag, the application prevented the assertiond process from suspending the malicious application. Note that PT_TRACE_ME was a request made by the traced process to declare that it expected to be traced by its parent.
If an app exploited this vulnerability and the user removed the app from task switcher, the application would continue to run in the background, while the user believed the application had been completely shut down."
The researchers also noticed that an iOS app does not need the get-task-allow entitlement to be set to true or any other specific background modes set. As a result, hypothetically, the flaw would "not need anything not allowed by Apple," according to FireEye. Therefore, such an app could pass through Apple's App Store review without a hitch.
Apple has been informed of the vulnerability and patched the problem in iOS version 8.4.1, released earlier this month.
A recent security breach which took place on the iOS platform left 220,000 iCloud users vulnerable to spying and remote hijacking. However, as reported by Hack Read, the security issue is caused by the installation of a malicious jailbreak device tweak -- and as you void your warranty and compromise your own security when you jailbreak a device, this has nothing to do with Apple security in itself.
This week, FireEye's 2015 Advanced Threat Report revealed that China and Russia are prime locations for launching advanced persistent threats (APTs) against targets including telecommunications firms, government entities, education, technology firms and the finance sector.
Beach reads for tech junkies
Read on: Top picks
- How to access Wi-Fi anonymously from miles away
- Apple OS X zero-day flaw hands over root access without system passwords
- Getting physical: A $10 device to clone RFID access keys on the go
- Amazon dreams of drones-only airspace
- Strike the source: RIAA targets BitTorrent protocol to block pirate content
- Three top tips to keep connected cars safe from hackers
In pictures: