Apple security features can be easily bypassed, says researcher

Security tools baked into Macs designed to protect users from malicious content can be easily bypassed, according to one security researcher.
More from RSA 2018
In a talk at the RSA Conference in San Francisco on Thursday, Synack director of research Patrick Wardle described how two OS X security tools can be bypassed to run malware.
"It's trivial for any attacker to bypass the security tools on Macs," said Wardle, according to ThreatPost. "If Macs were totally secure, I wouldn't be here talking."
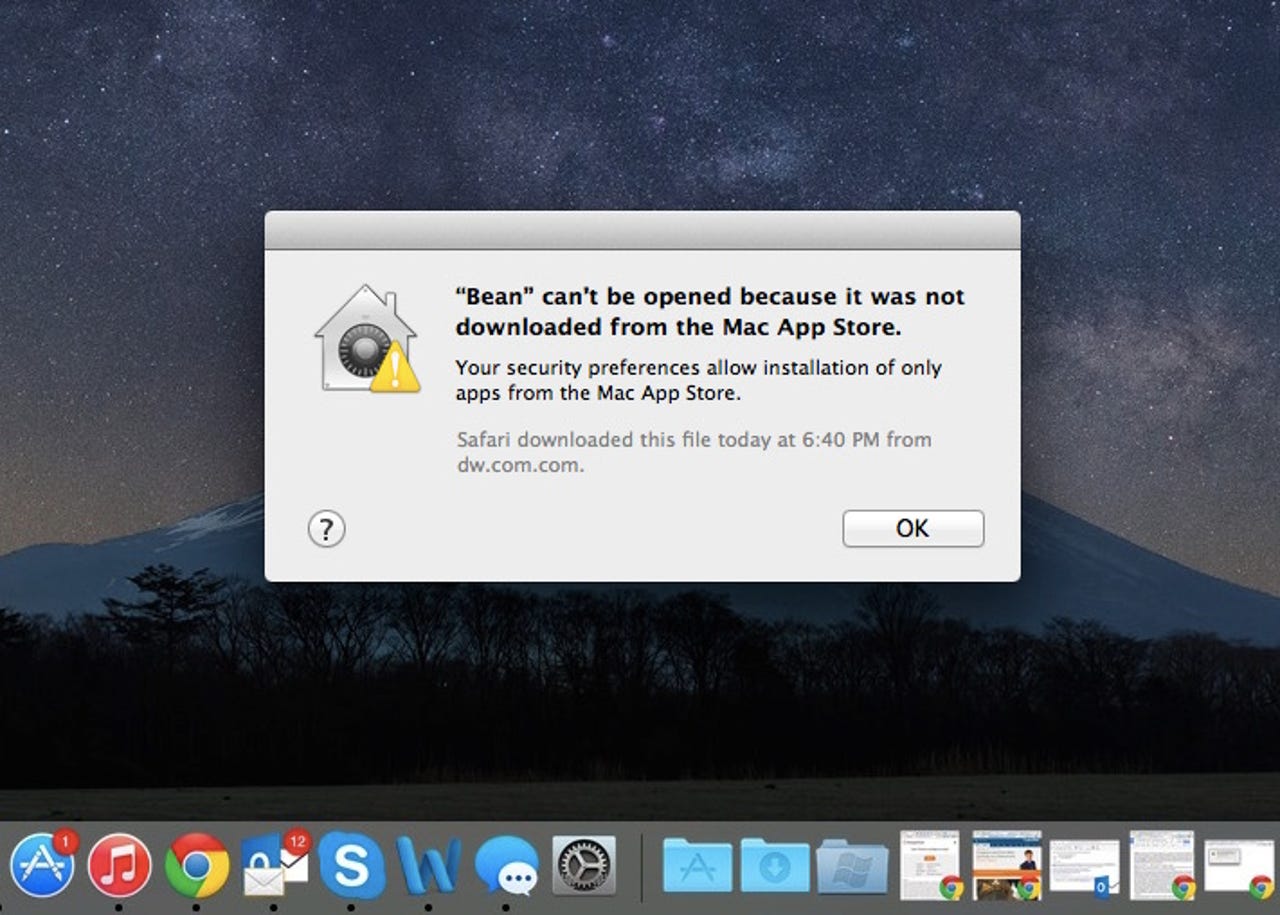
Those two security features, Gatekeeper and XProtect, were added in the more recent versions of OS X in response to a rising threat of malware aimed at the alternative operating system.
Gatekeeper, added in OS X 10.8 "Mountain Lion," restricts which apps can be opened and run on a computer. Most have it set to apps verified through the Apple App Store, or from verified developers. XProtect, a rudimentary malware scanner for the Mac introduced even earlier in OS X 10.6 "Snow Leopard," can block certain apps and plugins from running if there are known vulnerabilities.
"Gatekeeper doesn't verify extra content in the apps," said Wardle. When the app is opened, either Gatekeeper knows where it's from and allows it, or it doesn't and it shuts the app down. But it doesn't continually check the app, which Wardle said can be a problem. "So if I can find an Apple-approved app and get it to load external content, when the user runs it, it will bypass Gatekeeper," he said.
He also said XProtect was "trivial" to bypass.
By recompiling a known malware sample to change its hash, Wardle could sneak the malware past XProtect and run it on the target computer. Although he called XProtect's sandboxing feature "strong," it can be bypassed with a number of known vulnerabilities at the kernel level, which he said undermine its security.
We reached out to Apple for comment, but did not immediately hear back.