Checkm8 iOS jailbreak used as lure in online scam

Threat actors are using the hype around the recently announced Checkm8 iOS jailbreak exploit to trick users into installing unwanted iOS apps on their devices.
These apps aren't malicious per-se, but crooks are earning commissions from pay-per-install schemes.
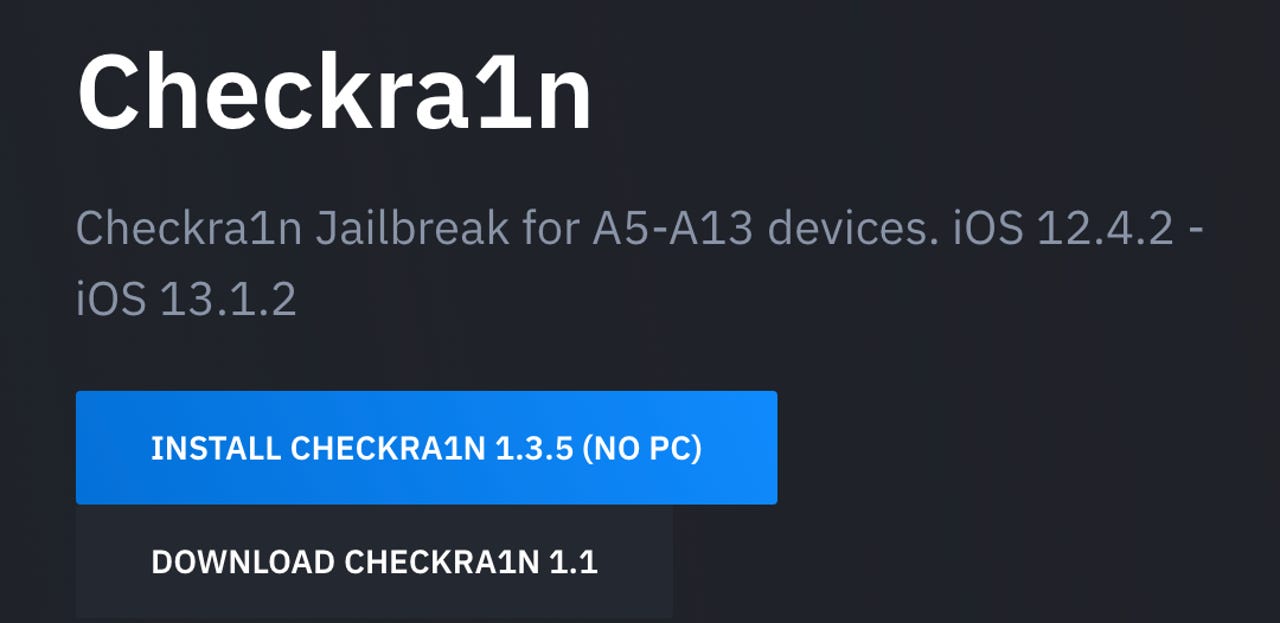
This online scam is currently hosted on checkrain[.]com.
This malicious website is a clone of the authentic checkra1n[.]com, a website where a team of security researchers said they plan to publish the first user-friendly Checkm8 jailbreaking tool.
But while devs are still working on the Checkra1n tool, crooks have already jumped on the hype bandwagon by registering a lookalike domain and using it to host their pay-per-install scam.
According to a Cisco Talos report published today, crooks are using the fake checkrain[.]com website to distribute a mobile configuration (.mobileconfig) file. When installed on a victim's device, this file adds a shortcut on the user's screen.
Clicking the shortcut starts a headless browser (a browser window to no user interface elements) that loads a page from the scam site, but pretends to be a native app. This disguised page uses JavaScript and CSS animations to mimic the process of jailbreaking a device.
Once the animation ends, the site urges users to install a game and reach Level 8 in seven days to finish the jailbreaking process.
Multiple apps are presented, and they are legitimate games hosted on the iOS App Store. The end goal of this scheme is for crooks to earn money, rather than infect users with malware. Talos researchers have documented this process in the video below.
This entire process is obviously nonsense, and anyone who has ever jailbroken an iPhone would be able to spot the ruse from a mile away.
However, malware authors never target tech-savvy users, but instead, they prey on users without advanced technical knowledge.
Those users who have spotted the malicious site and its tricks have already warned others to stay away [see Reddit thread].
For what it's worth, users should be aware that Checkm8 is not a one-click jailbreak -- like some have been in the past. Using the Checkm8 exploit to jailbreak an iOS device involves going through a series of complicated steps.
These steps include putting the iPhone into DFU mode, connecting it via a USB cable to a laptop or desktop, and using special software (such as the upcoming Checkra1n tool) to run the Checkm8 exploit against the iPhone during its boot-up process.
Furthermore, the Checkm8 jailbreak only roots an iOS device temporarily. The exploit is not boot-persistent, and iPhone owners will have re-jailbreak their device after every reboot.
Any jailbreaking tools that tell users different should not be trusted and are making claims beyond the original Checkm8 exploit's capabilities.