Chinese hackers developed malware to steal SMS messages from telco's network

One of China's state-sponsored hacking groups has developed a custom piece of Linux malware that can steal SMS messages from a mobile operator's network.
The malware is meant to be installed on Short Message Service Center (SMSC) servers -- the servers inside a mobile operator's network that handle SMS communications.
US cyber-security firm FireEye said it spotted this malware on the network of a mobile operator earlier this year.
How MessageTap worked
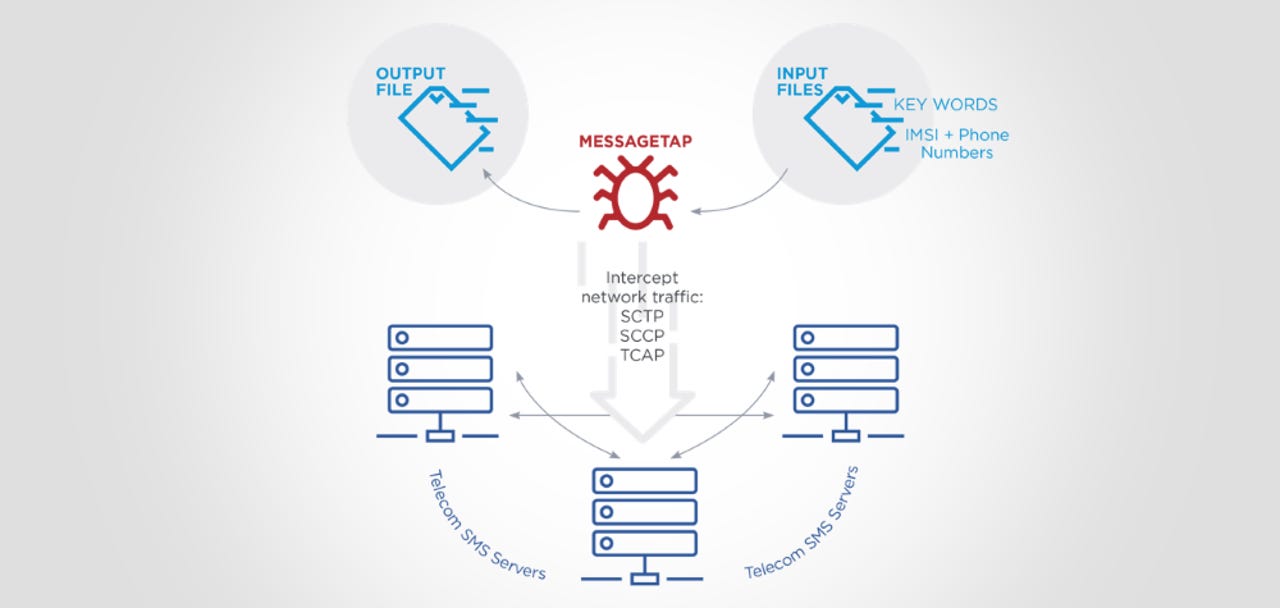
FireEye analysts said hackers breached a yet-to-be-named telco and planted the malware -- named MessageTap -- on the company's SMSC servers, where it would sniff incoming SMS messages, and apply a set of filters.
First, MessageTap would set SMS messages aside to be stolen at a later point if the SMS message's body contained special keywords.
"The keyword list contained items of geopolitical interest for Chinese intelligence collection," FireEye said. "Sanitized examples include the names of political leaders, military and intelligence organizations and political movements at odds with the Chinese government."
Second, MessageTap would also set SMS messages aside if they were sent from or to particular phone numbers, or from or to a device with a particular IMSI unique identifier. FireEye said the malware tracked thousands of device phone numbers and IMSI codes at a time.
Part of APT41's arsenal
The company's analysts linked the malware to a relatively new Chinese hacker group it calls APT41 [PDF report].
In a previous report, FireEye said that APT41 stood apart from other Chinese groups because besides performing politically-motivated cyber-espionage, the group's members also carried out financially-motivated hacks, most likely for their private benefits.
Furthermore, FireEye also found evidence on the hacked telco's network that APT41 interacted with the mobile operator's call detail record (CDR) database -- a database that stores metadata on past phone calls.
FireEye said APT41 queried for the "CDR records [that] corresponded to foreign high-ranking individuals of interest to the Chinese intelligence services."
While FireEye didn't name the hacked telco or the spied on targets, Reuters journalists said that MessageTap was related to China's efforts to track its Uyghur minority, with some of these efforts involving hacking telcos to track Uyghur travelers' movements.
Chinese hacking operations are changing
The discovery of this campaign is significant, in the grand scheme of things of Chinese cyber-espionage operations, as a whole.
For the past years, Chinese hacking groups have been known for their smash-and-grab approach, where they hacked a target and stole as much data as they could, to analyze it at later points.
APT41's modus operandi shows a carefully planned and very targeted surveillance operation aimed at a very small group of targets.
That's different from what Chinese hacking groups have done in the past, but it appears to have become the norm these days -- if we take into account the CCleaner and ASUS Live Update hacks, where Chinese hackers also breached a company just to go after a small subset of its customers.
The overall arch is that Chinese hacker groups are now getting very good at targeted operations, on par with what we've usually seen from US or Russian operations.
On a side note, FireEye's report today also confirms a general trend of Chinese hackers going after telecom opertions, first detailed in a June 2019 Cybereason report which found that Chinese government hackers had breached the networks of at least ten foreign mobile operators.