Chrome extension caught hijacking users' search engine results

Google has removed a Chrome extension from the official Web Store yesterday for secretly hijacking search engine queries and redirecting users to ad-infested search results.
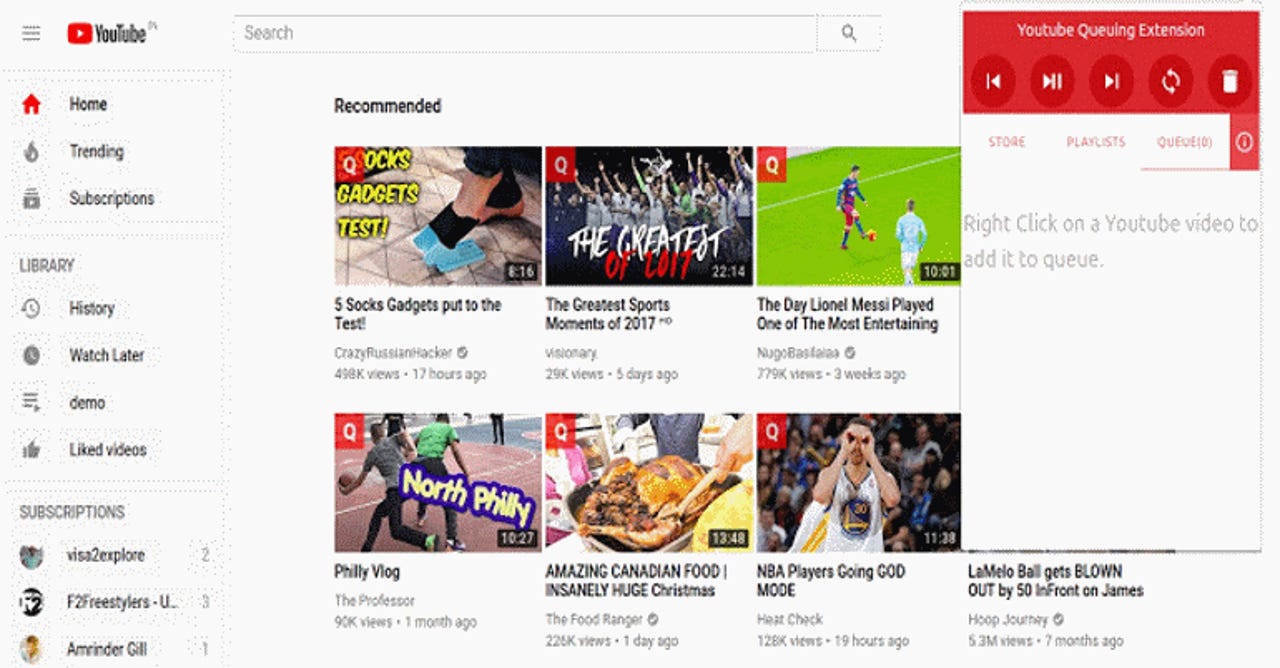
The extension's name was "YouTube Queue," and at the time it was removed from the Web Store, it had been installed by nearly 7,000 users.
The extension allowed users to queue multiple YouTube videos in the order they wanted for later viewing.
Extension turned into adware in early June
But under the hood, it also intercepted search engine queries, redirected the query through the Croowila URL, and then redirected users to a custom search engine named Information Vine, which listed the same Google search results but heavily infused with ads and affiliate links.
Users started noticing the extension's shady behavior almost two weeks ago, when first reports surfaced on Reddit, followed by two more, a few days later [1, 2].
The extension was removed from the Web Store yesterday after Microsoft Edge engineer (and former Google Chrome developer) Eric Lawrence pointed out the extension's search engine hijacking capabilities on Twitter.
Oh. pic.twitter.com/kbeJtXNUzZ
— Eric Lawrence 🎻 (@ericlaw) June 18, 2019
Lawrence said the extension's shady code was only found in the version listed on the Chrome Web Store, but not in the extension's GitHub repository.
Developer quietly sold the extension
In an interview with The Register, the extension's developer claimed he had no involvement and that he previously sold the extension to an entity going by Softools, the name of a well-known web application platform.
In a following inquiry from The Register, Softools denied having any involvement with the extension's development, let alone the malicious code.
The practice of a malicious entity offering to buy a Chrome extension and then adding malicious code to the source is not a new one.
Such incidents have been first seen as early as 2014, and as recently as 2017, when an unknown party bought three legitimate extensions (Particle for YouTube, Typewriter Sounds, and Twitch Mini Player) and repurposed them to inject ads on popular sites.
In a 2017 tweet, Konrad Dzwinel, a DuckDuckGo software engineer and the author of the SnappySnippet, Redmine Issues Checker, DOMListener, and CSS-Diff Chrome extensions, said he usually receives inquiries for selling his extensions every week.
I get such propositions every week. They offer quite a lot of money too.
— Konrad Dzwinel (@kdzwinel) July 13, 2017
In a February 2019 blog post, antivirus maker Kaspersky warned users to "do a bit of research to ensure the extension hasn't been hijacked or sold" before installing it in their browser.
Developers quietly selling their extensions without notifying users, along with developers falling for spear-phishing campaigns aimed at their Chrome Web Store accounts, are currently the two main methods through which malware gangs take over legitimate Chrome extensions to plant malicious code in users' browsers.
Coming around to the ad blocker debate
Furthermore, Lawrence points out that the case of the YouTube Queue extension going rogue is the perfect example showing malicious threat actors abusing the Web Request API to do bad things.
This is the same API that most ad blockers are using, and the one that Google is trying to replace with a more stunted one named the Declarative Net Request API.
[Alt Text: Browser extension abuses webRequestBlocking API and redirects user's search query from HTTPS website to unexpected search engine laden with ads using unsecured HTTP.]
— Eric Lawrence 🎻 (@ericlaw) June 18, 2019
This change is what triggered the recent public discussions about "Google killing ad blockers."
However, Google said last week that 42% of all the malicious extensions the company detected on its Chrome Web Store since January 2018, were abusing the Web Request API in one way or another -- and the YouTube Queue extension is an example of that.
In a separate Twitter thread, Chrome security engineer Justin Schuh again pointed out that Google's main intent in replacing the old Web Request API was privacy and security-driven, and not anything else like performance or ad blockers, something the company also officially stated in a blog post last week.
The Chrome position on this point has been very consistent. Yes, there are very real performance benefits for Declarative Net Request over Web Request, but the primary motivation has always been to improve security and privacy by scoping extensions to the access they need.
— Justin Schuh 🤬 (@justinschuh) June 18, 2019
Awesome Google Chrome extensions (May 2019 edition)
More browser coverage:
- JavaScript Template Attacks expose new browser fingerprinting vectors
- Opera launches Opera GX, world's first gaming browser
- Google promises to play nice with ad blockers (again)
- Google launches Chrome extension for flagging bad URLs to the Safe Browsing team
- Mozilla patches Firefox zero-day abused in the wild
- Microsoft Edge Reddit AMA: Edge might come to Linux
- How to use the Tor browser on an Android device TechRepublic
- Brave's privacy-first browser ads arrive with promised payout for you CNET