Critical Yahoo email flaw patched through bug bounty program

A critical flaw in Yahoo Mail which allowed attackers to hijack accounts has been fixed.
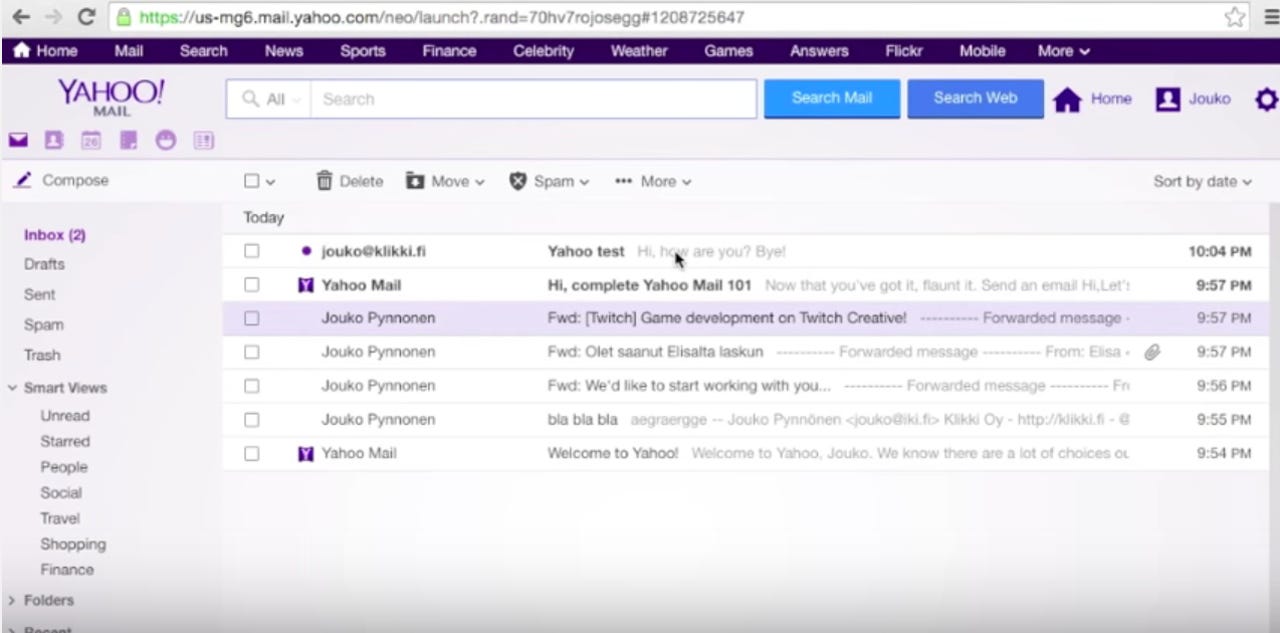
Disclosed privately by security researcher Jouko Pynnonen, Yahoo was informed of the vulnerability on 26 December 2015 through the HackerOne bug bounty program.
The stored XSS vulnerability allowed attackers to embed malicious JavaScript code in tailored email messages. A victim needed to do nothing else but read the message, which would then execute the code and give cyberattackers the ability to fully compromise the account, hijack settings, and both forward or send email to the attacker's server without the victim's knowledge or consent.
According to the researcher, the problem lies within how Yahoo filters HTML-formatted email messages. While the company performs this task to prevent malicious code from landing in user inboxes, Pynnonen says "certain malformed HTML code could pass the filter."
Security
In particular, some boolean HTML attributes could circumvent the filter and permit the execution of JavaScript code.
The proof of concept video below demonstrates how the vulnerability could be exploited to forward a compromised inbox to an external server, as well as how a virus could be loaded to attach itself to all outgoing emails sent by a victim.
The XSS vulnerability affected all versions of Yahoo Mail but not the tech giant's accompanying mobile application.
The bug was fixed on 6 January 2016. Pynnonen says the vulnerability was patched before the security issue was exploited in the wild.
Pynnonen was awarded $10,000 for his efforts through HackerOne. Yahoo uses the crowdsourced bug bounty platform to award researchers and contributors up to $15,000 for each flaw submitted.
14 Chrome browser extensions for a streamlined experience
Read on: Top picks