Encryption ransomware now 'tried and trusted' attacker business model

Ransomware which encrypts user files to blackmail victims into paying a ransom is now a "tried and trusted" cybercrime model which is only gaining in popularity, researchers claim.
On Tuesday, human phishing training and defense firm PhishMe released the findings of the company's Q2 2016 malware review at Black Hat USA, Las Vegas.
Within the report, the firm's security team says that during the second quarter of 2016, the usage rates of ransomware in cyberattacks including phishing campaigns and inclusion in exploit kits suggests this particular type of malware is now "firmly established as a business model, which shows no signs of diminishing."
PhishMe says that encryption ransomware now accounts for 50 percent of all malware configurations, and is, therefore, likely to remain a permanent fixture in the threat landscape.
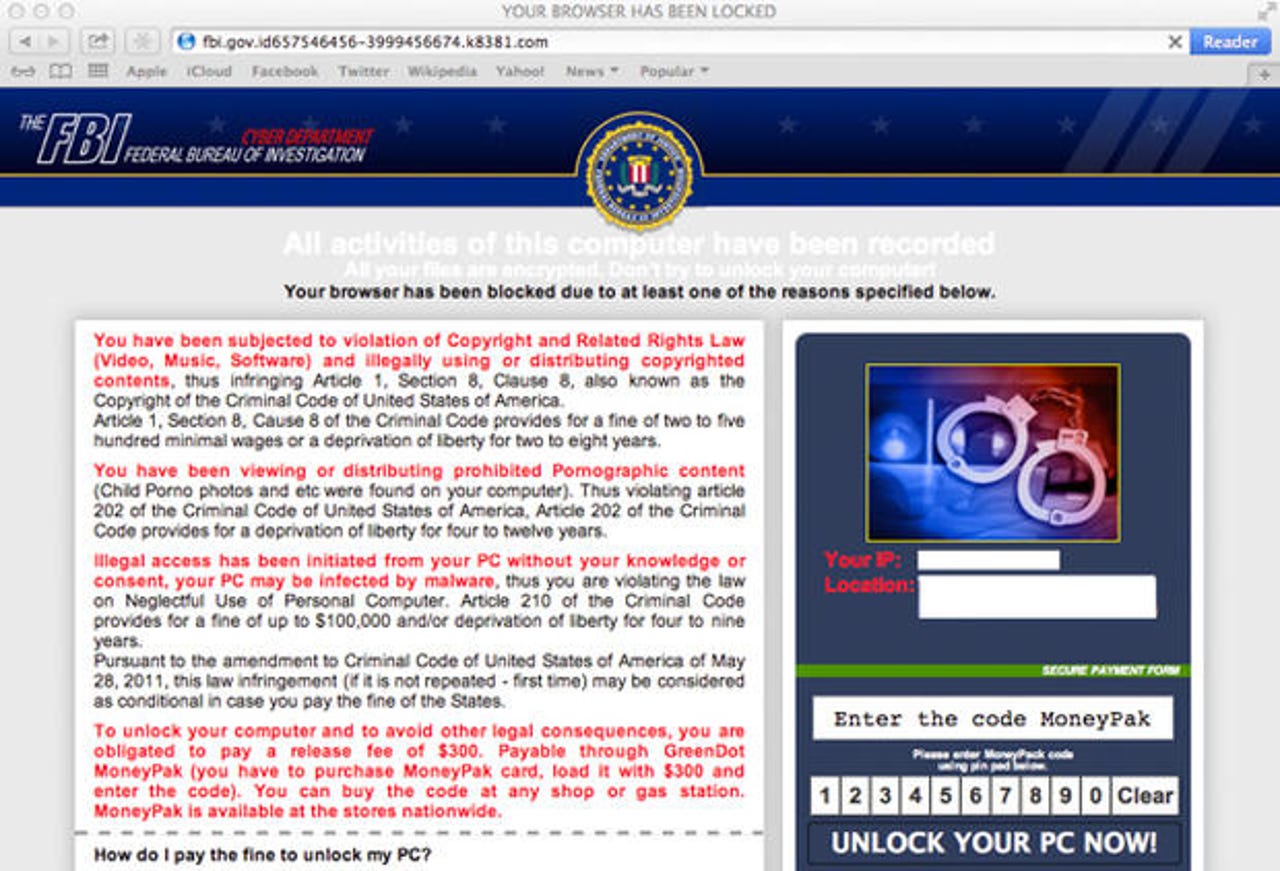
Ransomware is a rather nasty breed of malware. Once downloaded and executed on a vulnerable system, the malware usually encrypts files -- or even full drives -- and then throws up a landing page demanding payment in Bitcoin in return for a decryption key.
The problem is, paying up never guarantees victims will get their files back.
Researchers are attempting to stem the flow of ransomware by poking holes in the malware's code and creating free key generators, but for some, there is simply no way to retrieve victim content.
There are several main trends that the cybersecurity firm says are now firmly established in relation to ransomware. According to the team, ransomware which harnesses encryption to force victims to pay up is no longer a tool for a quick profit; rather, business is booming and deployments are increasing.
In addition, while simple attacks using ransomware can be debilitating, there is an increase in the strains of ransomware which are now employing "robust" feature sets and evasion techniques to circumvent protection offered by security solutions.
In March 2016, the researchers noted a change in ransomware families and strains. The team says that in total, ransomware variants were responsible for 93 percent of malware payloads delivered through exploit kits and phishing -- with consolidation rising.
It appears that Cerber and Locky are now "dominating" the ransomware scene. Both types use strong encryption to prevent access to files and often result in victims giving in and paying a fine.
"Barely a year ago, ransomware was a concerning trend on the rise. Now, ransomware is a fully established business model and a reliable profit engine for cybercriminals, as threat actors involved treat it as a legitimate industry by selling information, tools and resources to peers based all around the world," explained Rohyt Belani, CEO of PhishMe.
"Empowering the human element to detect and report these campaigns needs to be a top priority for organizations if they are to protect themselves from a threat that is here for the long term," Belani added.
In addition, the report highlights the increased use of remote access Trojans (RATs), which are able to open backdoors for threat actors looking to seize control of a compromised system remotely, steal data and spy on their victims. A recent high-profile case using RATs is the network intrusion and apparent theft of data from the US Democratic National Committee (DNC).
"The risks associated with these less-sophisticated, yet feature-packed malware utilities have been underscored through frequent use by advanced actors," the report notes.
Read on: FBI investigate US political party hacks, Russian ties