Google Chrome to block SHA-1 certificates in 2016

From next year, websites with new SHA-1 certificates will not be supported by Google Chrome in the interest of security.
Last September, Google announced plans to slowly sunset support for the SHA-1 algorithm used within online certificates, used to validate websites.
Despite resistance from some certificate authorities (CAs), the tech giant has now joined the likes of Mozilla and Microsoft and increased momentum for the move.
SHA-1 is a hash algorithm used to encrypt websites. While SHA-1 uses hashes which are 160 bits long, there are also other standards -- namely SHA-2, which implements a variety of hash sizes, and SHA-3, which is yet to become commercial or widely adopted as a standard.
In a blog post on Monday, Lucas Garron from Chrome security and David Benjamin from Chrome networking said further research has accelerated the move away from SHA-1. The research, conducted by academics from the Netherlands-based Centrum Wiskunde & Informatica (CWI), Inria in France and the Nanyang Technological University in Singapore (NTU Singapore) discovered that the cost of breaking the cryptographic algorithm is "significantly lower than previously thought."
As SHA-1 is not expensive to break, it is only a matter of time before attacks against the algorithm become commonplace and certificates potentially become forged with the protocol. As a result, many services which rely on SHA-1-based digital signatures -- such as credit card transactions, e-banking and software downloads -- can be deemed insecure and may place users at risk.
Security
Mozilla, Microsoft and Google have all announced their browsers will mark SHA-1 certificates as insecure by 2017 in favor of SHA-2, but Google has decided to stop support completely a little earlier than expected.
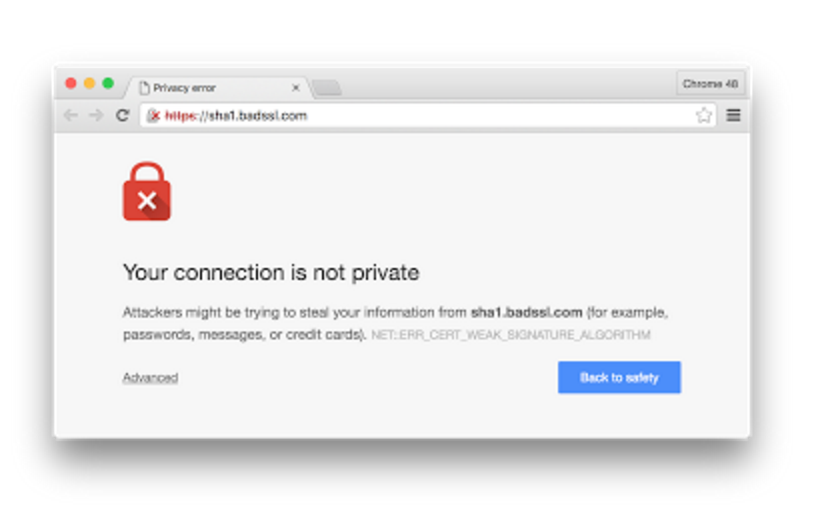
The move will come in two stages: the tech giant will block new SHA01 certificates with Chrome 48, before eventually blocking all SHA-1 certificates altogether at a later stage.
From early 2016, Chrome will display a certificate error if websites are signed with an SHA-1-based signature, use an SHA-1 certificate issued after 1 January 2016 or are chained to a public CA. (There are not meant to be any new SHA-1-based certificates issued by CAs after this date.) New SHA-1 certificates that chain to local trust anchors -- rather than public CAs -- will work without certificate errors, however.
"In line with Microsoft Edge and Mozilla Firefox, the target date for this step is January 1, 2017, but we are considering moving it earlier to July 1, 2016 in light of ongoing research," the Chrome team says. "We therefore urge sites to replace any remaining SHA-1 certificates as soon as possible."
Google says that by 1 January 2017 at the latest, Chrome will completely stop supporting the SHA-1 cryptographic protocol within certificates. The firm says:
"At this point, sites that have an SHA-1-based signature as part of the certificate chain (not including the self-signature on the root certificate) will trigger a fatal network error. This includes certificate chains that end in a local trust anchor as well as those that end at a public CA."
This is not the only drastic change to security the tech giant plans to make within the next few years. In addition, Chrome 48 will also stop supporting RC4 cipher suites for TLS connections, also deemed unsafe. The timeline matches Microsoft Edge and Mozilla's planned dates to end support.
2015 Holiday guide: Gifts and gadgets for under $100
Read on: Top picks