Hackers in the house: Why your IoT devices may have already joined a botnet

Unbeknown to you, your home connected devices could be unwitting participants in a DDoS attack.
Criminals are hacking into Internet of Things devices, taking advantage of their inherently weak security protocols to hijack them into performing distributed denial of service (DDoS) attacks.
DDoS attacks represent a growing threat to businesses, with attacks getting bigger and more dangerous all the time -- and connected devices are now making it even easier for hackers to carry them out.
Security
Many IoT devices are installed in the home or workplace then simply forgotten about by their owners, making them the perfect target for hackers to infect with malware and recruit into a zombie network to attack other targets -- all while the user remains ignorant their own network is being used in this way.
Devices such as web servers, routers, modems, network attached storage (NAS) devices, CCTV systems, and industrial control systems are all being recruited into botnets for the purpose of carrying out DDoS attacks, security researchers at Symantec have warned.
It's the inherent lack of security in some internet-connected IoT devices which makes them an appealing target for hackers, who are highly aware of the lax security employed by some manufacturers.
Many IoT products are shipped with only the most basic security in the form of a default username and password. Many others don't receive future firmware updates against threat protection, or if they do, the user doesn't apply them because they've either forgotten about the device, or they just don't see the need to take time to check for and apply updates.
As a result, any malware infection on connected devices is likely to go unnoticed, which makes them very attractive to malicious actors, specifically those keen to get their hands on as many internet connected devices as possible.
The reason is simple: while embedded devices are unlikely to provide cybercriminals with vast caches of data to steal -- although there's the possibility of infecting them with ransomware -- the fact the device is internet-connected means it can be hijacked and added to a botnet. And, although the processing power of these devices is small, put large groups of them together and you have network which is capable of carrying out DDoS attacks as well as any other machines.
But, despite the threat posed by hacking and the need for strong passwords being well-known, device vendors are still shipping products with only the most basic usernames and passwords -- such as 'admin', 'root', '123456', and 'password' -- leaving them extremely vulnerable to being hacked.
The top ten brute force usernames and passwords used to gain control of IoT devices
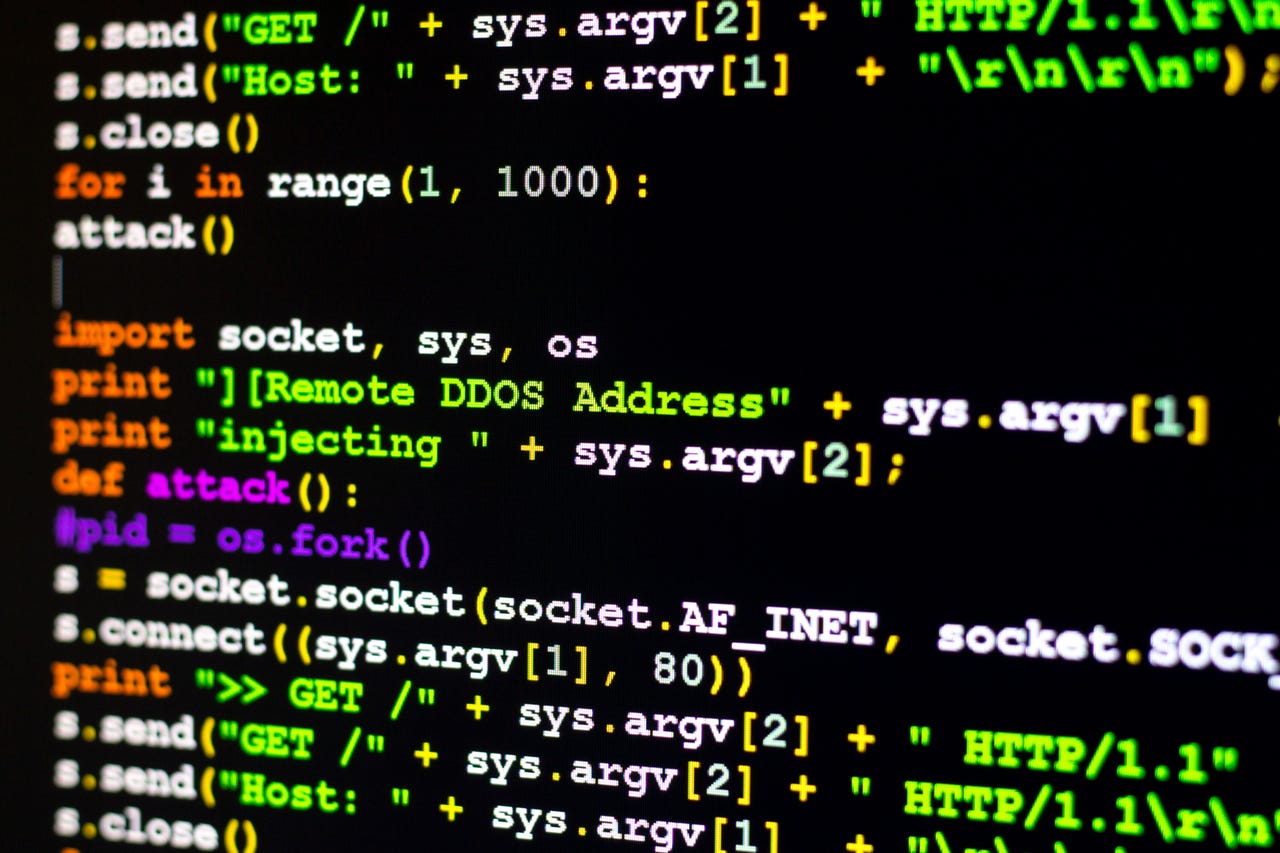
As a result of failures to update passwords or security software, malware targeting IoT devices is often coded to not so much break into the target, but rather calmly open the door by using the correct username and password, before adding it to a botnet. The most common method of finding a target to attack is simply conducting a scan of random IP addresses with open Telnet or SSH ports.
Once installed on the device, a script will execute a bot binary, establishing a connection to a command and control centre to await remote commands from the bot master, when they'll be used to target whichever network the attacker wants to DDoS.
A total of eight new malware families designed to specifically target connected devices during 2015 -- such as the infamous LizardStresser -- and many of these threats have continued to be active into 2016. More than half of attacks involving Internet of Things devices originated from China and the US, although the method of attack is growing across the globe.
Staying protected against IoT malware is relatively simple: users should change the default credentials on any embedded device on their network and replace them with a much stronger password. Users should also regularly check with the manufacture of the device for firmware updates that can help protect them against potential threats.
READ MORE ON CYBERCRIME
- How cybercriminals earned $100,000 just by sending a DDoS threat email
- CNET: Interview with a DDoS troll: Meet 'the Gods of the Internet'
- Blizzard hit with DDoS attack disrupting play for gamers
- This sneaky botnet shows why you really, really shouldn't use the same password for everything
- TechRepublic: How to mitigate ransomware, DDoS attacks, and other cyber extortion threats