Hacking robots: Why it could be a lot easier than it should be

Researchers have warned of flaws in a range of robots.
Robots manufactured by some of the biggest brands in the industry contain cybersecurity flaws leaving them vulnerable to hacking, according to research published by an IT security company.
While unsecured Internet of Things devices already pose a risk to businesses, they're fixed items, while robots can move and physically interact with the world and the people around them, making it even more important that they are extremely secure and protected from hackers.
But researchers at IOActive tested numerous home, business and industrial robots built by six of the biggest names in robotics and identified vulnerabilities which could be exploited to spy via the robot's microphone and camera, to leak personal or business data.
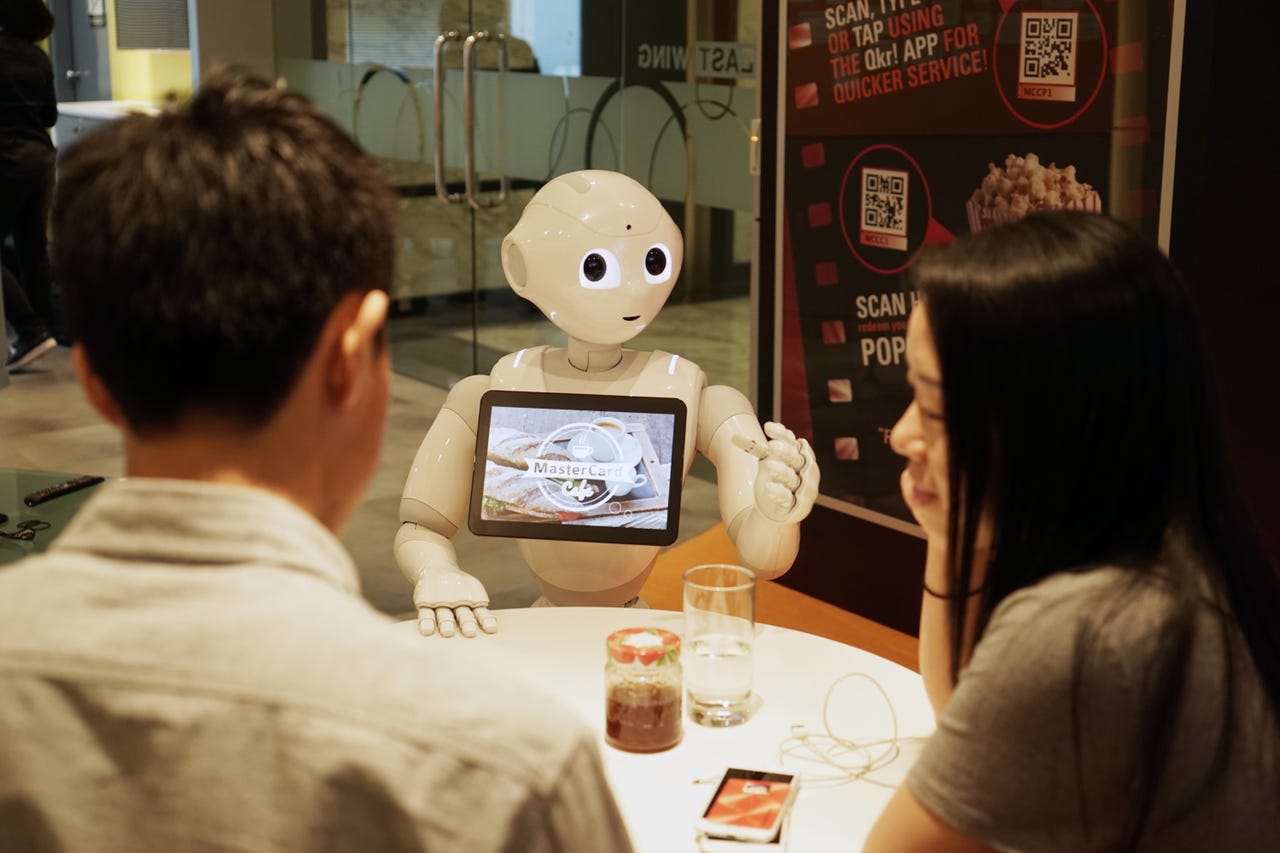
In total, researchers said they had discovered almost 50 cybersecurity vulnerabilities across the SoftBank Robotics' NAO and Pepper robots, UBTECH Robotics' Alpha 1S and Alpha 2 robots, the ROBOTIS ROBOTIS OP2 and THORMANG3 robots, Universal Robots' UR3, UR5, UR10 robots, Rethink Robotics' Baxter and Sawyer robots and several robots using technology by Asratec Corp.
Researchers spent six months testing mobile applications, robot operating systems, firmware images, and other software in order to identify the flaws in the robots, which for the purposes of maintaining security haven't be specifically detailed in IOActive's newly released Hacking Robots Before Skynet report.
However, it said there are a number of common vulnerabilities in robot ecosystem components across the tested robots.
These included include insecure communications - such as robots with Bluetooth connections - authentication issues, privacy issues as a result of how robots store and send data, weak default configurations and vulnerable open source frameworks.
This range of cybersecurity vulnerabilities could easily be exploited by hackers to carry out activities like spying through microphones and cameras and stealing data.
IOActive senior security consultant Lucas Apa said robot manufactures appear to be repeating the same cybersecurity mistakes as Internet of Things vendors.
"It's the same story over and over again, after this report some vendors will start to worry about security, but many will continue working in the same way without taking care of security," he said.
"It's the same with IoT; some vendors are starting to worry about security, but we still see a lot of new products coming out with the same old security problems. It's the same old story we've see with the car industry, IoT and medical devices".
IOActive has contacted all of the robotics manufacturers mentioned mentioned in the report, but the cybersecurity firm said it had made the research public in the hope that the industry and the wider public will grow more aware of the issue.
"We need to tell everyone about these problems and that they need to be addressed," Cesar Cerrudo, CTO at IOActive told ZDNet.
"Because in the future when there are robots everywhere, if they're not secure, there will be a lot of problems which will have impacts on our lives. We need to do something about securing robots now, because if not, it'll be crazy in the future".
Researchers contacted all six of the vendors mentioned in the report about the vulnerabilities, but Apas said only four responded, with two indicating they were going to investigate the issues.
In an email to ZDNet, Rethink Robotics spokeperson said "safety and security have always been a top priority for our company" and confirmed that they'd been in touch with IOActive and were aware of the issues detailed in the report.
"Two of the items noted by IOActive are intentional design features for the research and education version of Rethink's robots only. These users need a greater degree of accessibility into the system to create new uses for the robot as part of their research," they said, adding "The other items noted by IOActive were already known to us and addressed in Rethink's latest software release"
Rethink also describes how the company regularly provides bug fixes and security patches for Baxter and Sawyer and thanked IOActive "for their efforts in this important area".
For Cerrudo, it's important that all robotics manufactures take cybersecurity seriously and described vulnerabilities in robots as "a real problem" which needs to be addressed sooner rather than later.
"If we don't start doing something right now then having insecure robots will get really, really bad for businesses and for people because they could end up hurting people or animals, damaging property," he said.
"It's different from IoT because IoT devices can be insecure, but they don't move around; they don't have wheels, legs or arms. But with robots, they could do anything, they can move, grab and throw things, so there's a high risk here if we don't do something," Cerrudo concluded.
ZDNet contacted all the manufacturers mentioned in the report, but at the time of publication hadn't received a response from Softbank, UBTECH, ROBOTIS, Universal Robots or Asratec Corp.
UPDATE - Since the initial publication of this piece, some of the robotics manufacturers named in the report have responded to queries. One of them is Universal Robotics, which says it's aware of IOActive's research.
"While our products meet their specifications and stated standards, we've been made aware of the report and are investigating the potential vulnerability described and potential countermeasures," a spokesperson told ZDNet via email.
UBTECH also reacted to the report - and a spokesperson said the company hasn't been contacted by IOActive about the findings.
"The security of our robots and of our customers is a top priority at UBTECH. We have not been contacted by IOActive in regards to the accusations in their report," said a spokesperson.
IOActive said it had contacted UBTECH but only received an autoreply message stating someone would be in touch within 48 hours. "I never received any response from them," said IOActive's Apa.
FURTHER READING
- Robots: An amazing tour through the biggest collection ever assembled
- Smart gadgets need security. Startups, that's your cue [CNET]
- Robots and AI: Should we treat them like pets, or people?
- Why the age of connected cars presents a 'very real threat' in cybersecurity [TechRepublic]
- Horrible hacks, death robots, and kamikaze phones: Meet the scariest tech of the year