Stabbing fruits to breaking your skull: robot bugs make hacking too easy

Researchers have demonstrated how easy it is to hack consumer and industrial robots to do everything from spy to injure in the hopes of waking up vendors that dismiss security in their product cycles.
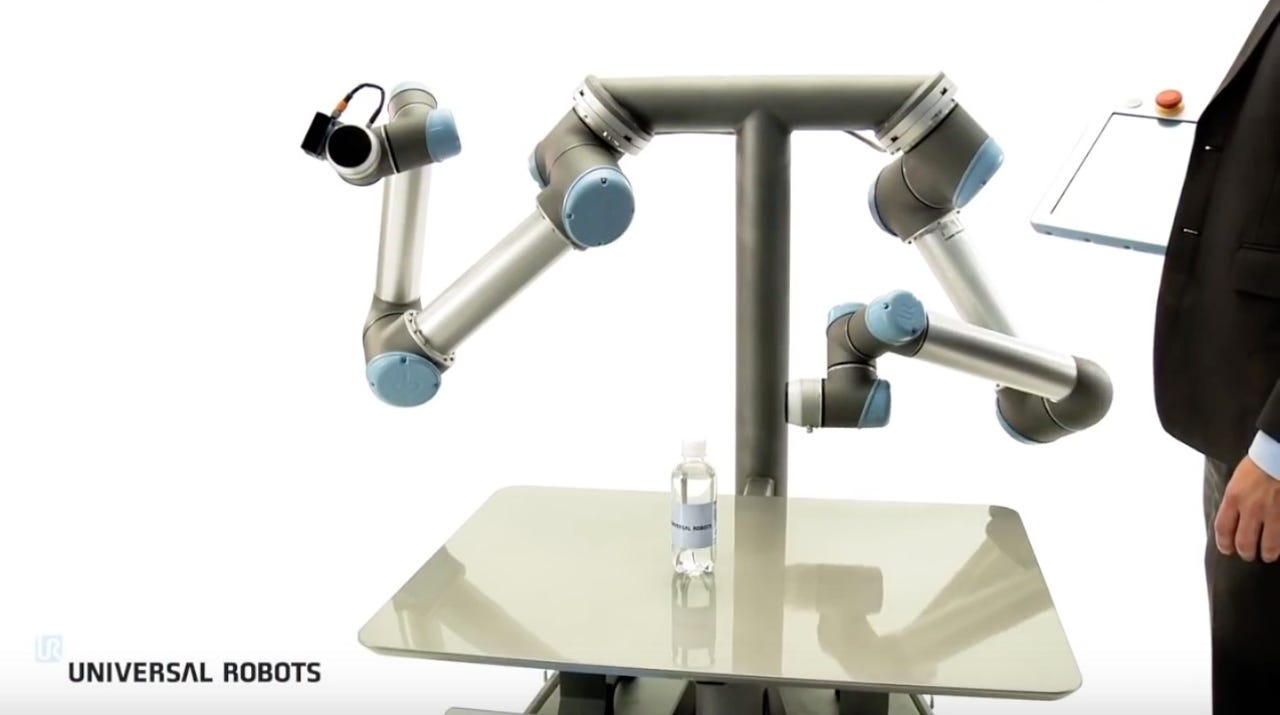
On Tuesday, the security team at IOActive revealed security flaws in robotic products developed by Universal Robots, the UR3, UR5, and UR10.
These models contain a swathe of critical security issues which can not only lead to remote code execution, but the violation of robotic safety laws, the release of safety systems, and spying in both home and business environments.
In a blog post, the researchers note that today's robots have moved beyond automatic, limited, repetitive tasks and now not only are robotic inventions becoming common in our homes, but many are considered "collaborative" robots which work closely with humans in shared workspaces. Robots have also been granted new capabilities, ranging from "sight" through cameras to the ability to "hear" with microphones and voice recognition algorithms.
These extensive abilities can make dangerous or repetitive manufacturing tasks easier to bear in industrial settings, but unless they are controlled, they could also be an avenue for covert surveillance or perhaps even cause destruction and injury.
Last February, IOActive published a preview of a research project into the security standards of such robots, called "Hacking Robots Before Skynet." The security team found almost 50 critical security issues in the home, business, and industrial robots from manufacturers including Universal Robots and Rethink Robotics.
Authentication issues, default deployment problems, physical tampering weaknesses and insecure communications bugs were only some of the issues discovered, many of which could be used to cause harm to industries, employees, and their environments.
Universal Robots is yet to patch the problems, reported in January this year, while Rethink Robotics appears to have smoothed over the worst of the vulnerabilities.
"Our goal is to make cobots (collaborative robots) more secure and prevent vulnerabilities from being exploited by attackers to cause serious harm to industries, employees, and their surroundings," says IOActive researcher Lucas Apa. "I truly hope this blog entry moves the collaborative industry forward so we can safely enjoy this and future generations of robots."
To further this goal, IOActive has released the details of an attack against Universal Robot products which utilizes a vulnerability chain to manipulate safety limits and disable emergency buttons -- a scenario which the researchers say "could directly threaten human life."
By chaining six vulnerabilities together, the team was able to remove safety limits and cause a UR robot's arms to swing wildly. While one robot may not be such an issue, in an industrial setting with many of these robots working together with humans, such a scene could wreak havoc and cause widespread harm. The team says that even with the smallest model, the UR5, the force caused is "more than sufficient to cause a skull fracture."
"A very technical bug, like a buffer overflow in one of the protocols, exposed the integrity of the entire robot system to remote attacks," Apa commented. "We reported the complete flow of vulnerabilities to the vendors back in January, and they have yet to be patched. What are we waiting for?"
When it comes to home models, IOActive also mentioned UBTech's Alpha2, and SoftBank's Pepper and NAO robots. As shown in the video below, the team were able to completely take over the Alpha 2, transforming it from a household assistant to a tomato-stabbing maniac.
In addition, IOActive was able to take control of the robots' camera and microphone systems to theoretically spy on their owners.
Universal Robots told Bloomberg that the company's products "undergo rigorous safety certification," and this "includes monitoring any potential vulnerability, not just cybersecurity." SoftBank has claimed to fix all of IOActive's reported bugs.
While the idea of a tomato-stabbing robot may at first seem amusing, the vulnerabilities in all of the robotic models are nothing to laugh at. Unless vendors start taking responsibility for security in their product cycles and during installation, the consequences in the future could be severe.
Update 16.55 BST: An UBTECH spokesperson told ZDNet:
"UBTECH has been made aware of a sensationalistic video produced by IOActive featuring the Alpha 2. The video is an exaggerated depiction of Alpha 2's open-source platform. UBTECH encourages its developer community to code responsibly and discourages inappropriate robot behavior."
Related coverage
- Enigma ethereum marketplace hijacked, investors duped by phishing scam
- ShadowPad: Backdoor in enterprise server software exposed
- Google awards student $10k for discovery of App Engine data leak flaw