Insulin pump vulnerabilities could lead to overdose

Users of the Animas OneTouch Ping insulin pump system have been warned that security vulnerabilities in the device allow attackers to remotely deliver insulin doses.
On Tuesday, researchers from Rapid7 revealed the existence of three vulnerabilities in the Animas OneTouch Ping insulin pump system.
Johnson & Johnson subsidiary Animas produces the device reads user blood glucose levels through a meter before the pump uses these readings by "communicating wirelessly" in the 900mhz band to deliver insulin.
According to the research team, one of the major security flaws within the OneTouch Ping is caused because there is a lack of encryption between these components.
According to Rapid7 researcher Jay Radcliffe, the first vulnerability, CVE-2016-5084, reveals that data flowing between these two modules is transmitted in the clear. This opens the door for eavesdroppers to capture information such as dosage data and blood glucose results.
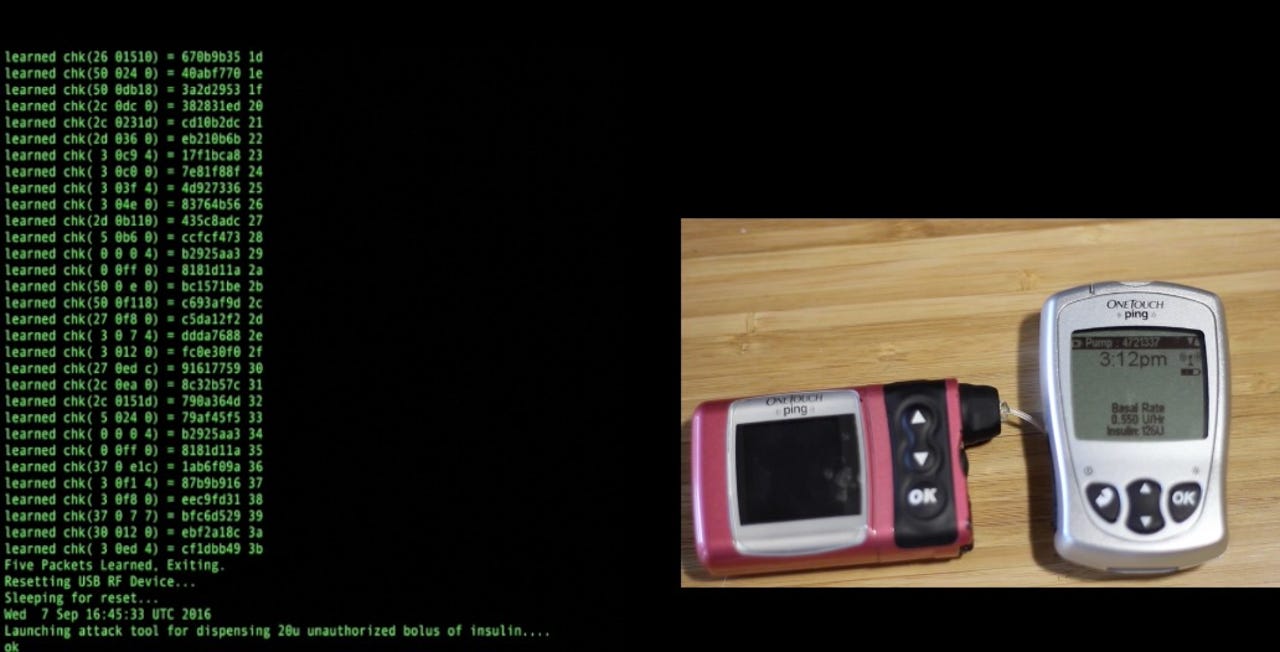
The second critical security flaw, CVE-2016-5085, stems from the weak pairing between the pump and meter. The pairing process takes place during setup to prevent pumps from taking orders from other remotes in the vicinity and is done through a five-packet exchange in cleartext where the devices exchange serial numbers and some additional information.
Once paired, the device uses this information to generate a "key," however, the packet information is the same every time -- and so no encryption is in place.
"Attackers can trivially sniff the remote/pump key and then spoof being the remote or the pump," Radcliffe notes. "This can be done without knowledge of how the key is generated. This vulnerability can be used to remotely dispense insulin and potentially cause the patient to have a hypoglycemic reaction."
The third security vulnerability is equally as dangerous. The bug, CVE-2016-5086, highlights the fact the communication taking place between the pump and meter has no timestamps or sequence numbers and because of this, no defense against replay attacks, in which legitimate commands could be intercepted by an attacker and then played back at a later date.
This, too, could be used in theory by an attacker to re-issue insulin doses.
It is believed attacks against the medical device could take place from up to 10 meters away, but this could be extended to one or two kilometers with off-the-shelf radio kit. However, Radcliffe encourages a clear head when considering the safety threat of the pump, commenting:
"If any of my children became diabetic and the medical staff recommended putting them on a pump, I would not hesitate to put them on a OneTouch Ping. It is not perfect, but nothing is. [..] This is just the advice of one parent and a person who has spent 17 years counting carbs and taking a risk on how much insulin is right. "
In a letter to users of the OneTouch Ping (.PDF), Anima said the company has investigated the issue and wanted to assure customers that the "probability of unauthorized access to the One Touch Ping system is extremely low."
"It would require technical expertise, sophisticated equipment, and proximity to the pump, as the OneTouch Ping system is not connected to the internet or to any external network," the letter continues. "In addition, the system has multiple safeguards to protect its integrity and prevent unauthorized action."
Anima offers a way to mitigate the threat, however. If patients wish they can turn off the radio frequency feature, but this does mean users must enter their blood glucose levels manually.
The issues were disclosed to the vendor in April this year. Mitigations were provided by Anima by September, several weeks before public disclosure.