New BlindSide attack uses speculative execution to bypass ASLR

Academics have developed a new technique for attacking secure computer systems by abusing speculative execution, a CPU mechanism that's normally used for performance optimizations.
The technique, named BlindSide, was detailed in a paper [PDF] published last week by a team of academics from the Stevens Institute of Technology in New Jersey, ETH Zurich, and the Vrije University in Amsterdam.
Researchers say that BlindSide can be used to craft exploits that bypass ASLR (Address Space Layout Randomization) on modern operating systems.
BlindSide can bypass ASLR
Memory addresses are important for an attacker. If an attacker knows where an app executes its code inside the memory, a hacker can fine-tune exploits that attack particular applications and steal sensitive information. As its name hints, ASLR works by randomizing the location where code executes inside memory, effectively neutralizing attacks until attackers find a way around ASLR.
To bypass ASLR, an attacker typically needs to find an "information leak" type of vulnerability that leaks memory locations; or the attacker can probe the memory until they find the proper location where another app runs and then modify their code to target that memory address space.
Both techniques are hard to pull off, and especially the second, which often leads to system crashes or to the attacker's noisy probing being detected by security systems.
The new BlindSide attack works by moving this probing behavior into the realm of speculative execution.
Speculative execution, to the rescue!
Speculative execution is a performance-boosting feature of modern processors. During speculative execution, a CPU runs operations in advance and in parallel with the main computational thread.
When the main CPU thread reaches certain points, speculative execution allows it to pick an already-computed value and move on to the next task, a process that results in faster computational operations. All the values computed during speculative execution are discarded, with no impact on the operating system.
Academics say that this very same process that can greatly speed up CPUs can also "[amplify] the severity of common software vulnerabilities such as memory corruption errors by introducing speculative probing."
Effectively, BlindSide takes a vulnerability in a software app and exploits it over and over in the speculative execution domain, repeatedly probing the memory until the attacker bypasses ASLR.
Since this attack takes place inside the realm of speculative execution, all failed probes and crashes don't impact the CPU or its stability as they take place and are suppressed and then discarded.
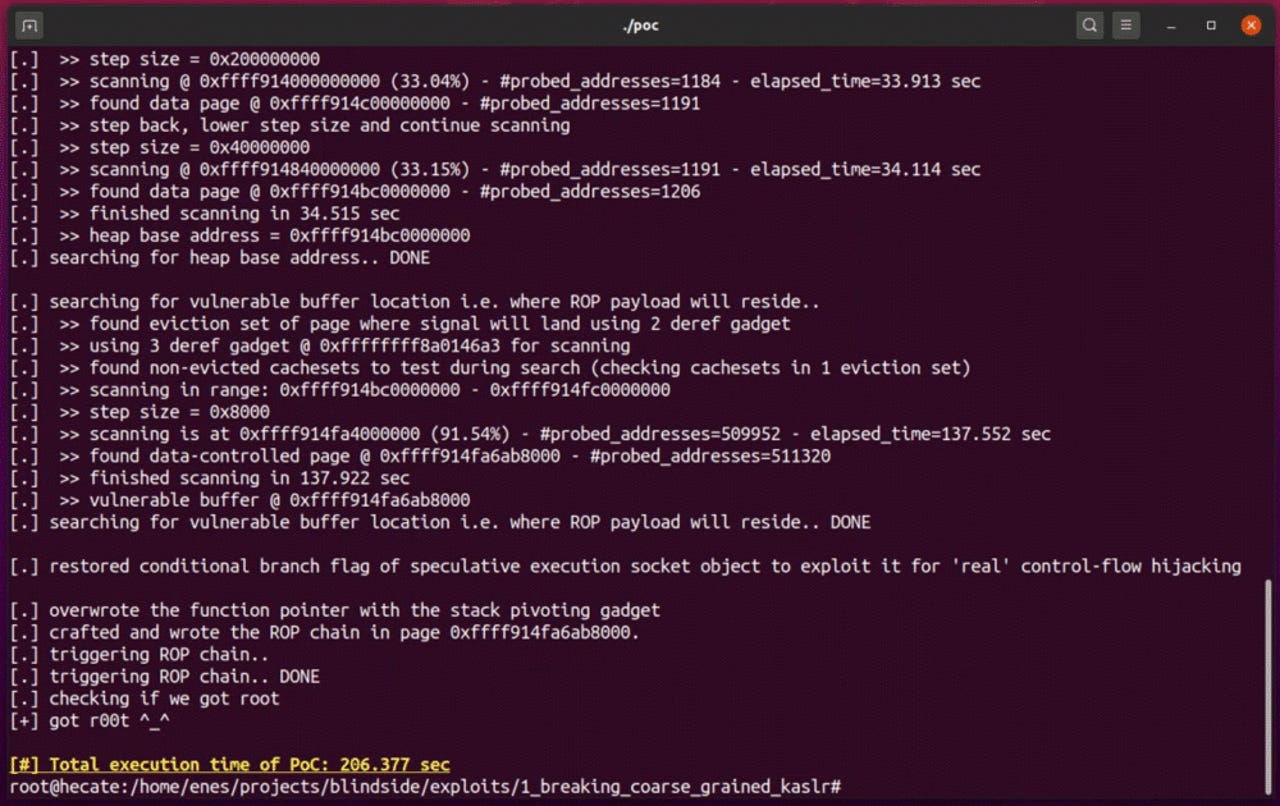
All the attacker needs is a simple memory corruption vulnerability they can exploit on a system. In their research paper, the team used a single buffer overflow on the Linux kernel to:
- Break KASLR with BlindSide to mount a reliable ROP exploit;
- Break arbitrary randomization schemes with BlindSide to mount an architectural data-only exploit (leaking the root password hash);
- Break fine-grained randomization and kernel execute-only memory to dump the full kernel text and mount a reliable ROP exploit.
The researchers said that BlindSide effectively allows attackers to "hack blind," without needing to worry about ASLR.
BlindSide attacks also work regardless of architecture, being tested on both Intel and AMD CPUs alike.
In addition, BlindSide attacks also work despite the recent mitigations that CPU vendors have added against speculative execution attacks like Spectre, Meltdown, and others.
The team's research paper proposes several mitigations that OS makers could deploy to counter BlindSide attacks.