Researchers uncover Samsung SmartThings connected home security flaws

Design flaws could place homes controlled by Samsung SmartThings at risk.
A team of security researchers has unveiled multiple security flaws in Samsung's SmartThings platform which granted cyberattackers the ability to compromise Internet of Things (IoT) homes in a variety of ways.
The team discovered multiple design flaws on the IoT platform and were able to exploit software vulnerabilities to unlock doors, set new virtual keys without an owner's permission, control fire alarms and kill vacation modes which automatically adapt lighting and security settings while owners are away.
Researchers from the University of Michigan, together with Jaeyeon Jung from Microsoft Research, are due to present a paper titled "Security Analysis of Emerging Smart Home Applications" later this month documenting their full findings at the IEEE Symposium in San Jose.
The paper reveals the IoT platform contained "significant" design vulnerabilities and it did not take long for proof-of-concept (PoC) attacks to be successfully levied against Samsung's SmartThings system.
During testing, the research team created a malicious SmartThings app which in the wild could be downloaded by an unwitting user or installed through a malicious link.
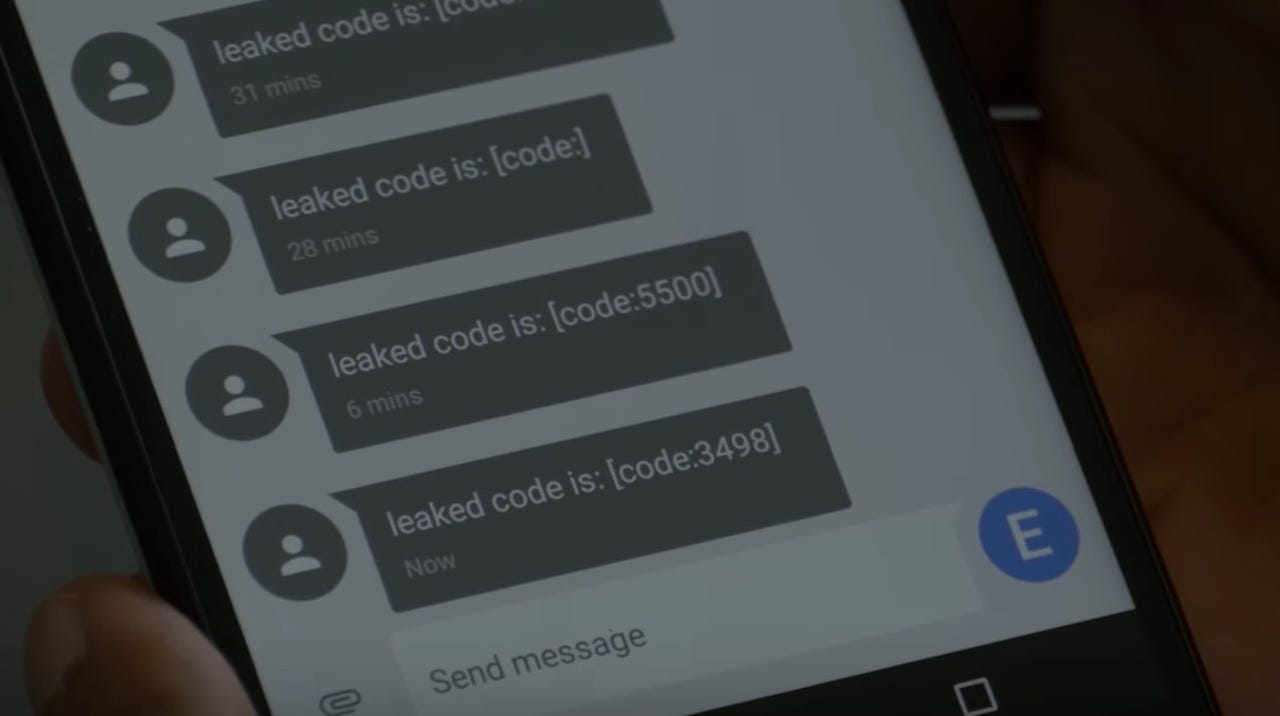
Once this app was established, the "lock-pick malware app" -- disguised as a battery level monitor -- was able to eavesdrop on the IoT network, set a new PIN code for smart door locks and send that PIN to a cyberattacker.
This app could also exploit vulnerabilities in the SmartThings platform to turn off "vacation mode," a high-profile function of the connected home platform. Through the platform, users can automatically set lights to automatically switch on and off and to open and close home accessories such as blinds to dupe potential burglars into thinking someone is home, but the researcher's malicious app was able to turn off this mode in a separate application, potentially placing homes at risk.
In addition, the team was able to show an existing and popular SmartApp used by the IoT system could be remotely exploited by attackers to generate a spare door key "by programming an additional PIN into the electronic lock," the digital equivalent of handing out a spare key to your home to a stranger.
To make matters worse, the original SmartApp was not designed to program PIN codes into locks.
Security
A malicious app could also be used to inject false messages into a SmartApp to falsely turn on fire alarms.
According to the team, the SmartThings app store hosts over 500 apps for controlling your home, but many of these apps ask for privileges they do not need, which compounds these security problems.
The team found that over 40 percent of these 500 applications are "over-privilege," a trend which must change if IoT homes are going to pass a basic level of security.
"The access SmartThings grants by default is at a full device level, rather than any narrower," Atul Prakash, U-M professor of computer science and engineering said. "As an analogy, say you give someone permission to change the light bulb in your office, but the person also ends up getting access to your entire office, including the contents of your filing cabinets."
Earlence Fernandes, leader of the study, said that Samsung's platform is fine for controlling basic functions such as window shades, but consumers should consider just how much control of their home they really want to give to a computer system in its infancy.
Fernandes commented:
"One way to think about it is if you'd hand over control of the connected devices in your home to someone you don't trust and then imagine the worst they could do with that and consider whether you're okay with someone having that level of control."
In a subsequent blog post, SmartThings CEO Alex Hawkinson acknowledged the team's findings, and said that over the past few weeks SmartThings and the researchers have been working together to remove these avenues for exploit.
A number of updates to the SmartThings platform have already been released to protect against these vulnerabilities.
How to protect your connected home and Internet of Things devices
Read on: Top picks