Researchers say Intel's Management Engine feature can be switched off

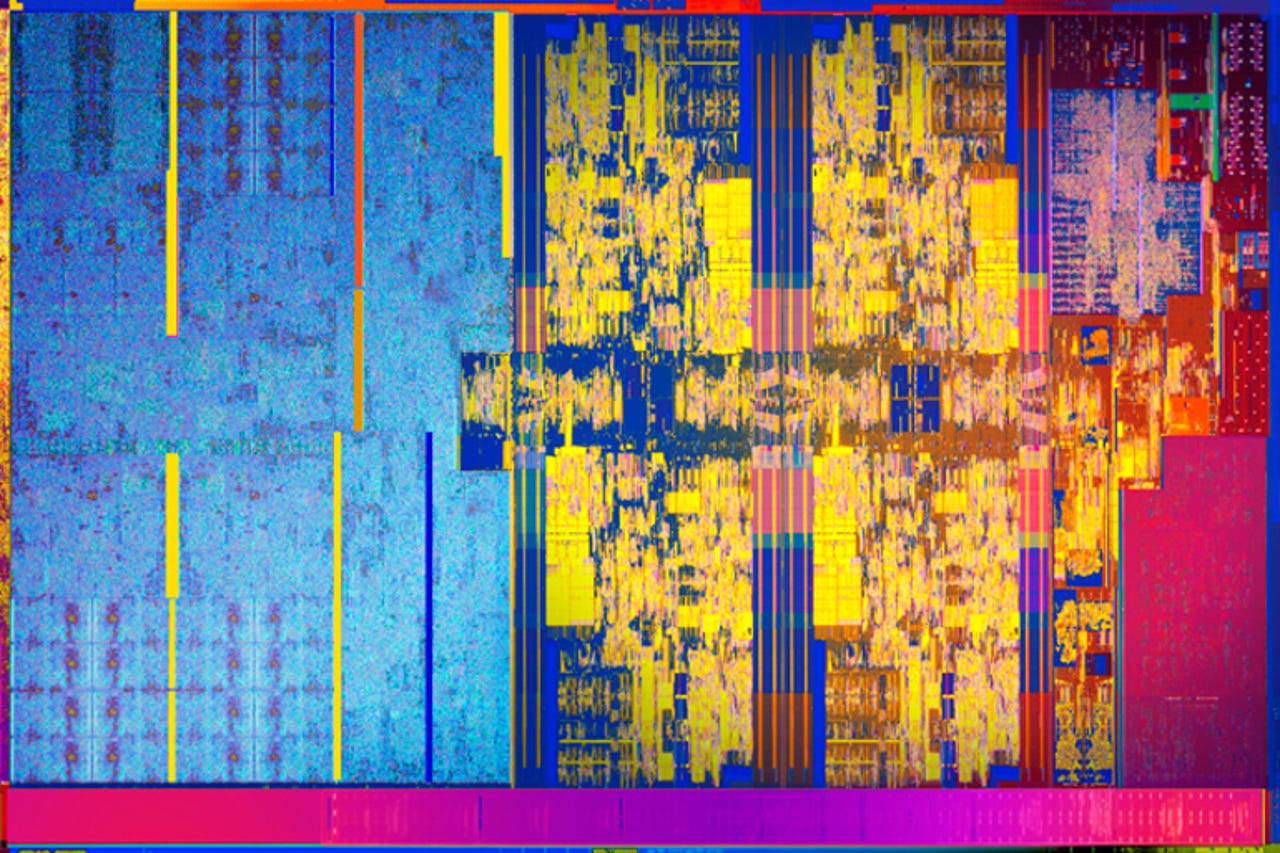
Management Engine, a core component of modern Intel chips, could provide an attacker with a powerful backdoor if compromised.
It seems some government customers can request Intel's always-on Management Engine (ME) 'master controller' for its CPUs to be disabled.
Security
That's not an option for the general public, but researchers at Russian security firm Positive Technologies have found a way to use these government-only privileges to disable ME.
ME is a core component of modern Intel chips that if compromised can provide an attacker with a powerful backdoor. As the researchers note, ME can't be completely disabled because of its role in initializing hardware, power management, and launching the main processor.
Security researchers have long been worried by Intel ME because it's impossible for anyone but Intel to audit for any backdoors, which has led to numerous attempts to disable it, including the me_cleaner project.
Concern over it was raised again in May after a critical flaw was found in Intel's Active Management Technology firmware, an enterprise feature for remote PC management that runs on ME.
The AMT bug prompted the EFF's call on Intel to provide a way disable or limit ME, which it described as an "undocumented master controller for your CPU".
Without a disabling mechanism and greater transparency from Intel, the EFF cautioned that Intel chips might not be safe to use in critical-infrastructure systems.
Positive Technologies researchers Mark Ermolov and Maxim Goryachy discovered that Intel ME can be disabled by setting a 'HAP mode activation bit' found in the ME firmware code. The researchers found a field in ME's firmware files called 'reserve_hap' with a comment next to it stating 'High Assurance Platform enable'.
HAP refers to the US government's High Assurance Platform Program, a secure computing program run by the NSA in collaboration with the tech industry. According to Bleeping Computer, disabling ME requires setting the relevant bit to '1'.
Intel confirmed to Positive Technologies that the undocumented HAP mode activation bit is present to support customers participating in the HAP program.
"In response to requests from customers with specialized requirements we sometimes explore the modification or disabling of certain features," Intel said in a statement.
"In this case, the modifications were made at the request of equipment manufacturers in support of their customer's evaluation of the US government's High Assurance Platform program. These modifications underwent a limited validation cycle and are not an officially supported configuration."
Ermolov and Goryachy speculate that the HAP mode is designed to reduce the chances of side-channel leaks.
The researchers have provided a utility on GitHub for others to disable ME without Intel's assistance, but warn users may destroy their device by using it.
Nonetheless, the researchers have provided a way to disable ME after the hardware has initialized, and the main processor has started.
Update - Intel has told ZDNet: "Intel does not and will not design backdoors for access into its products. Recent reports claiming otherwise are misinformed and blatantly false. Intel does not participate in any efforts to decrease security of its technology."
The headline of this story has been amended. The 'HAP mode' linked to the NSA-run High Assurance Platform Program could enable customers to switch ME off, not to switch it on.
Read more
- Intel unveils AI-focused Movidius VPU chip
- Toyota, Intel, Ericsson, NTT form connected car big data consortium
- Intel's Mobileye is building a fleet of fully autonomous cars
- Intel i9's new rival: Latest Ryzen Threadripper is AMD's cheapest yet
- Computing shifts may rearrange pecking order for Intel, Qualcomm, AMD, Nvidia, chipmakers
- Intel and DARPA look to AI and machine learning to boost graph analytics in big data (TechRepublic)
- 5 reasons you'll want Intel's crazy new Core i9 CPUs, and 3 reasons you won't (CNET)